Editorial Commitment & Standards
Expert-led analysis, human-verified accuracy, and technological transparency for the modern digital landscape.
Our Editorial Commitment
Upstanding Hackers serves as a premier destination for original analysis, practical guides, and strategic insights covering artificial intelligence, cybersecurity, Web3, business technology, and digital marketing. In an age of automated misinformation, our mission is to provide a “Human-First” perspective on the tools and threats shaping our future.
Every article published on this platform is written by a named author with demonstrable, real-world expertise in their subject area. We do not publish anonymous content or unverified “spam” articles. This page serves as our social contract with you, our reader, explaining exactly how our content is built, audited, and maintained.
🤖 Human-AI Hybrid Content Disclosure
To remain at the cutting edge of technology, Upstanding Hackers utilizes a Human-AI Hybrid Model. We use Large Language Models (LLMs) to assist with technical data synthesis, initial research aggregation, and code debugging. However, final editorial control is strictly human. Every guide is manually tested, the prose is reviewed for nuance and bias, and every technical command is verified in a sandbox environment before publication.
Our Editorial Board

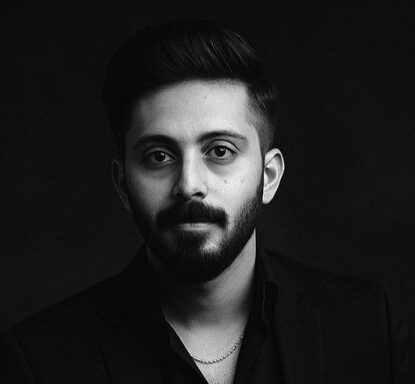
Rana Junaid Shahid
Junaid founded Upstanding Hackers with 5+ years of experience building AI-driven pipelines using Make.com, OpenAI, and n8n. He specializes in AI agents, no-code strategy, and Web3 infrastructure. Contact: junaid@upstandinghackers.com

James Turner
With over a decade in the InfoSec industry, James specializes in threat intelligence, OSINT methodology, and zero-trust architecture. He translates complex attack vectors into actionable defense guides.
Zohaib
A certified Salesforce specialist, Zohaib focuses on CRM architecture, workflow automation, and Sales Cloud customization. He helps businesses scale through measurable, data-driven automation.

Marie Summer
Marie covers the intersection of AI tools and modern work practices. She provides reviews and productivity insights that help business leaders navigate the human impact of digital transformation.
Research & Verification Methodology
Technical accuracy is our highest priority. We follow a “Trust but Verify” workflow for every piece of content:
- Expert Attribution: Every author must have direct, verifiable experience with the software or methodology they are writing about.
- Primary Source Auditing: We cross-reference technical claims against official vendor documentation, academic whitepapers, and authoritative bodies like CISA, NIST, OWASP, and MITRE ATT&CK.
- Dual-Source Requirement: For cybersecurity threats or vulnerabilities, we do not publish claims without at least two independent primary source verifications.
- Data Integrity: All statistical claims must include a direct citation to the original research or report. We clearly separate opinion and analysis from factual reporting.
Technology moves faster than any other industry. A guide from 2024 might be obsolete by 2026. We conduct rolling reviews of our pillar content. If a platform we cover (like Salesforce or OpenAI) releases a major update, we trigger a content audit. Our “Last Updated” timestamps reflect substantive changes, not just minor typos.
We are committed to transparency. If an error is identified, we correct it within 48 hours and append a “Correction Note” at the bottom of the article. We do not “silently edit” factual errors. To report an error, contact info@upstandinghackers.com.
Commercial Independence
Editorial decisions at Upstanding Hackers are made independently of our commercial relationships. To maintain our operations, we use the following disclosures:
- Affiliate Disclosure: We may earn a commission from links to products or services. These are always labeled clearly at the top of the article.
- Sponsored Content: Any article funded by a third party is explicitly labeled “Sponsored” or “Promoted Content.”
- No Pay-to-Play: We do not accept payment in exchange for favorable reviews or positive mentions. Partners and advertisers have zero influence over our editorial testing or final conclusions.
