🔄 Last Updated: December 14, 2023
Founder & AI Automation Specialist · Upstanding Hackers
Rana Junaid Shahid is a technology specialist and founder of Upstanding Hackers with over 5 years of hands-on experience in AI automation, no-code workflows, and digital infrastructure. He has built and deployed AI-driven pipelines using tools like Make.com, OpenAI, and no-code AI automation for businesses across multiple industries. His work focuses on making complex emerging technologies practical and accessible — without requiring a developer background. Junaid covers AI agents for business, automation strategy, digital marketing technology, and Web3 infrastructure.
Cyberattacks known as “zero-day” attacks exploit undiscovered security flaws for which a patch or other countermeasure has not yet been created. This implies that individuals and companies are vulnerable to exploitation by threat actors as operating systems and software developers are not yet aware of these flaws. Hence, the phrase “day zero” refers to the attack’s setting of the precedent for when developers must start working on a patch or other fix for the vulnerability.
The Catastrophic Effects of Zero-Day Exploits
Zero-day assaults can have disastrous effects. They make it possible for viruses like ransomware to steal sensitive data, compromise operational continuity, and compromise crucial systems.
Companies and software developers are in a race against time to fix vulnerabilities in zero-day attacks before hackers take advantage of them by developing and distributing patches. The intricacy of this procedure emphasizes how closely government authorities, software developers, and the cybersecurity industry must work together to guarantee a prompt and efficient response.
How Do the Attackers Find These Weaknesses?
Cybercriminals spend a lot of time looking for novel ways to launch their attacks. For instance, they can spend hours trying to find potential vulnerabilities in the website, service, or software code. However because a web page or application’s internal structure is so intricate, it can be exceedingly difficult for an individual to identify weak places in its code.
A vulnerability is no longer considered a zero-day vulnerability once it has been identified and addressed. Sadly, these vulnerabilities are not often found right away, and it may take days, weeks, or even years to realize the effects of a cyberattack.
How Does It Affect Us Users?
As a result of the aforementioned, users start to identify app bugs and alert the developer to the issue. The vulnerability is found once the developers look into it. They work promptly to address the issue with an update.
Such a vulnerability poses an extremely high level of harm to us as users. First, because we have no control over the vulnerability or way to defend ourselves, the attacker exploits a weakness in the internal workings of the application or web service. Furthermore, by doing routine tasks like opening a multimedia file, utilizing the web browser, or even just visiting a reputable website, we can put our devices at risk.
How to Protect Against Zero-Day Vulnerability Exploits?
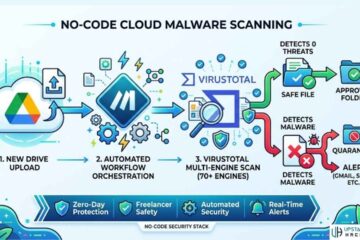
Zero-day exploits are hard to fight against because they are so hard to find. Malware signature checkers are used by software vulnerability scanning programs to compare suspicious code to known malware signatures. Vulnerability scanning is unable to identify or stop harmful code when a zero-day assault employs a zero-day exploit that has never been discovered previously.
Companies cannot identify the precise exploit before it happens because zero-day attacks take use of an unidentified security vulnerability. Nonetheless, there are several ways to lower risk exposure and shield businesses from emerging dangers.
1. Use VLANs

Virtual local area networks, or VLANs, can be used to divide up a network into discrete sections or to isolate important traffic across business servers using physical or virtual network segments. This prevents hackers from being able to take advantage of business-critical network areas for data theft, even if they manage to get past the company’s defenses and access the network.
2. Keep All Systems up to Date
Patch management done right is essential for any size firm. When software developers find out about a potential threat to exploitation, they will release security fixes. While immediately applying zero-day and n-day updates won’t resolve unidentified software vulnerabilities, it will increase the likelihood that a zero-day attack will be unsuccessful.
3. Implement Network Traffic Encryption
It is not feasible to find every security flaw before a zero-day exploit appears. Nonetheless, businesses can impose authentication and encryption on vital network traffic by utilizing the IP security protocol (IPsec). However, if data encryption isn’t used, all of the company’s network’s data might become susceptible, there could be a lot of downtime, and income could suffer greatly.
4. Implement IPS or IDS
Signature-oriented It’s possible that IPS and IDS alone won’t be sufficient to identify and stop an attack. They can, however, notify security personnel of questionable incoming data as a byproduct of an ongoing attack.
5. Implement NAC
Malicious computers can infiltrate vital sections of the business’s environment and jeopardize devices connected to the network. Only those with permission can access certain locations thanks to network access control (NAC), which rejects requests for missing authorization.
6. Carry Out Regular Checks and Inform Employees

Finding vulnerabilities and preventing them before attackers can exploit them requires regular vulnerability scanning throughout enterprise networks. Furthermore, a lot of zero-day exploits depend on human error. Employee protection online and the avoidance of malicious threats and unintentionally enabled zero-day exploits can be achieved through educating staff members on proper cybersecurity hygiene.
7. Use Antivirus
Implementing the most suitable preventive measures is the greatest strategy to lessen the impact of an attack. To begin, make sure your firewall is up to date, keep an eye on your network traffic, and prevent any illegal access. Using a strong antivirus program is also essential. Purchasing one of the top antivirus programs is an additional crucial step. Many threats may be found and stopped by good antivirus software before they have a chance to do any harm. Recall that maintaining cybersecurity requires continuous effort rather than a one-time effort. It’s crucial to keep up with the most recent threats and know how to defend oneself.
Conclusion
Given that zero-day exploits are unknown, it follows that possible vulnerabilities may likewise be unidentified. The payload could be ransomware, denial of service (DoS), remote code execution, or a variety of other threats. Because zero-day vulnerabilities are so sneaky, they could endanger an organization for months before they are found and fixed.
The firm can fall prey to an advanced persistent threat (APT) due to an unidentified vulnerability. Because APTs deploy sophisticated software to navigate the Internet and leave behind backdoors, they pose a particular threat. Organizations frequently believe they have controlled the danger, but after a comprehensive forensic examination of the system, it becomes clear that the APT is still present.
See Also: A Guide On Finding The Best Online Course For Cybersecurity