🔄 Last Updated: April 19, 2026
Your Slack workspace is leaking data. So is your Microsoft Teams environment. And the culprit isn’t a hacker — it’s an AI agent your own employees installed without IT approval. Preventing shadow AI agents in corporate Slack and Teams has become one of the most urgent enterprise security priorities of 2026.
Shadow AI agents operate silently in the background. They access sensitive channels, read confidential messages, and trigger automated workflows — all without security team oversight. Consequently, the damage they cause often goes undetected for months.
In this guide, you will learn exactly what a shadow agent is, how to detect one, and how to stop them. Furthermore, we cover critical tools like n8n and Zapier permissions management — two platforms that employees frequently use to build unauthorized AI pipelines.
What Is a Shadow Agent?
| Shadow Agent Definition: A shadow AI agent is any artificial intelligence bot, workflow automation, or LLM-powered application that operates within a corporate communication platform — such as Slack or Microsoft Teams — without explicit IT department authorization, security review, or formal governance approval. Shadow agents typically gain access through OAuth tokens, personal API keys, or third-party automation tools installed by employees without going through official channels. |
Shadow agents differ from sanctioned bots in one critical way: visibility. Your security team knows about approved integrations. However, shadow agents bypass that process entirely. An employee installs a Zapier workflow on Monday. By Friday, it’s reading your #finance channel and sending summaries to a personal email.
Moreover, shadow agents often carry compounding risk. They connect to external AI services, process internal message content, and store conversation data on third-party servers — all outside your data residency controls.
Why Shadow AI Agents Thrive in Slack and Teams
The productivity appeal is real. Shadow agents save employees hours each week. As a result, adoption spreads fast and informally. Three core factors fuel this growth inside enterprise messaging platforms.
First, both Slack and Teams make app installation deceptively easy. Slack’s App Directory allows non-admin users to install hundreds of applications with a single click. Similarly, Teams permits direct sideloading of custom apps in many enterprise tenants by default.
Second, AI automation platforms like n8n and Zapier have dramatically lowered the technical barrier. No-code builders now let any employee connect an AI model to their Slack workspace in under ten minutes. For instance, an employee can wire OpenAI’s GPT-4 to a private Slack channel without writing a single line of code.
Third, most organizations still have no formal AI governance policy for messaging platforms. According to Gartner’s research on enterprise AI adoption, over 60% of organizations lack documented policies for AI agent use in internal communication tools. Therefore, employees operate in a policy vacuum and assume silence equals approval.
Shadow Agent Risk Comparison: Slack vs. Microsoft Teams
The table below summarizes key risk factors and the recommended mitigation for each. Use it to prioritize your security response.
| Shadow Agent Risk Factor | Slack Risk | Teams Risk | Mitigation Tool |
| Unauthorized OAuth tokens | High | High | n8n credential scoping |
| Unapproved automation workflows | Medium | High | Zapier admin policies |
| Data exfiltration via webhooks | High | Medium | DLP + channel auditing |
| Unmonitored AI message processing | High | High | Conditional Access + SIEM |
| Third-party app overpermissioning | Medium | Medium | App directory review |
n8n and Zapier Permissions Management: Closing the Back Door
Most shadow agents don’t appear as installed Slack bots. Instead, they live inside no-code automation platforms. n8n and Zapier are the two most common entry points. Understanding their permissions models is therefore essential to stopping unauthorized AI pipelines.
Managing n8n Permissions in Enterprise Environments
n8n is an open-source workflow automation tool that employees can self-host — or access via n8n Cloud. Its credential scoping system is powerful, but it requires deliberate configuration. Without proper governance, a single n8n instance can hold dozens of OAuth tokens connected to your Slack workspace.
To lock down n8n in your organization, apply the following controls:
- Enable Role-Based Access Control (RBAC) — assign credential visibility only to team owners, not all members.
- Restrict Slack OAuth scopes — audit which n8n credentials hold ‘channels:read’, ‘messages:read’, or ‘files:read’ Slack permissions.
- Use environment variables for secrets — prevent individual employees from creating personal API connections.
- Enable n8n audit logging — forward execution logs to your SIEM for anomaly detection.
- Block outbound webhooks to unapproved domains — configure network-level egress filtering on self-hosted instances.
Managing Zapier Permissions for Corporate Slack and Teams
Zapier presents a different challenge. Unlike n8n, Zapier is a SaaS platform — meaning employees can connect their personal Zapier accounts to your corporate Slack workspace without touching your infrastructure at all. Consequently, traditional network controls offer no protection.
Zapier’s admin console, available on Business and Enterprise plans, provides the tools you need. Apply these controls immediately:
- Enable Zapier for Teams admin controls — restrict which users can create Zaps that connect to Slack or Teams.
- Review connected apps quarterly — use Zapier’s Connected Apps report to identify unauthorized Slack connections.
- Block personal Zapier accounts at the Slack app level — use Slack’s admin API to restrict third-party OAuth authorizations.
- Require approval workflows — Zapier Enterprise supports approval-before-publish for new Zaps touching sensitive workspaces.
- Audit Zapier webhooks in Teams — look for incoming webhook connectors added to private channels without IT approval.
For a deeper dive into AI automation security, read our related guide on automating VirusTotal API with Make.com — which covers no-code security automation best practices in detail.
Shadow Agent Security Checklist for Corporate Slack and Teams
| Use this checklist during your next security review. Each item addresses a specific shadow agent attack vector identified in enterprise deployments. |
Phase 1: Discovery — Find What’s Already There
- ☐ Export the Slack App Directory report from your admin console
- ☐ Run the Microsoft Teams app usage report from the Teams admin center
- ☐ Enumerate all active OAuth tokens via Slack’s oauth.v2.access audit logs
- ☐ Search n8n credential stores for Slack or Teams OAuth connections
- ☐ Identify all Zapier accounts linked to corporate Slack using the OAuth app audit
- ☐ Scan Microsoft Entra ID (Azure AD) for unrecognized third-party app consents
Phase 2: Assessment — Evaluate the Risk
- ☐ Classify each discovered agent as sanctioned, shadow, or unknown
- ☐ Review permission scopes for each installed Slack app (flag any with ‘admin’ or ‘files:write’)
- ☐ Check Teams bot permissions for ‘RSC’ (Resource-Specific Consent) violations
- ☐ Identify which shadow agents process message content (highest risk category)
- ☐ Determine if any shadow agents send data to external AI APIs (OpenAI, Anthropic, etc.)
Phase 3: Remediation — Remove the Risk
- ☐ Revoke unauthorized OAuth tokens immediately via Slack admin settings
- ☐ Remove unapproved Teams apps via the Teams admin center app management
- ☐ Disable personal Zapier Slack connections using Slack’s app restriction policy
- ☐ Implement n8n credential ownership and transfer policy
- ☐ Block unauthorized outbound webhook domains at the network firewall level
Phase 4: Prevention — Stop Future Shadow Agents
- ☐ Publish a formal AI governance policy covering messaging platform integrations
- ☐ Enable Slack’s App Approval workflow to require admin sign-off for all new apps
- ☐ Configure Microsoft Teams to require admin approval for third-party app installs
- ☐ Set up SIEM alerts for new OAuth token grants in Slack and Teams audit logs
- ☐ Run quarterly shadow agent audits using this checklist
- ☐ Train employees on the risks of unauthorized AI bots via security awareness programs
How to Detect Shadow AI Agents Already Running in Your Environment
Detection requires looking beyond your standard app inventory. Shadow agents often hide in plain sight — appearing as legitimate personal productivity tools while quietly processing corporate data.
Start with your Slack audit logs. Specifically, filter for events of type ‘app_installed’, ‘oauth_token_created’, and ‘bot_added’. Any event not tied to an IT-approved deployment ticket warrants investigation. Similarly, in Microsoft Teams, the Unified Audit Log in Microsoft Purview captures ‘TeamsAppInstalled’ and ‘BotMessageReceived’ events that reveal unauthorized agent activity.
Furthermore, monitor your network traffic. Shadow agents that use external AI APIs generate distinctive outbound traffic patterns — frequent HTTPS calls to domains like api.openai.com or hooks.zapier.com originating from your messaging infrastructure. A robust threat intelligence platform can help you correlate these signals automatically.
Additionally, review your network security in cloud computing controls. Shadow agents frequently exploit gaps in cloud egress filtering that organizations overlook when focusing exclusively on endpoint security.
Building an AI Agent Governance Framework for Enterprise Messaging
Reactive detection is not enough. Long-term protection requires a governance framework that makes shadow agent creation structurally difficult.
The most effective frameworks share three common elements. First, they establish a clear approval process for all AI integrations — including personal automation tools like n8n and Zapier. Second, they implement technical controls that enforce that process automatically. Third, they create a feedback loop through regular auditing.
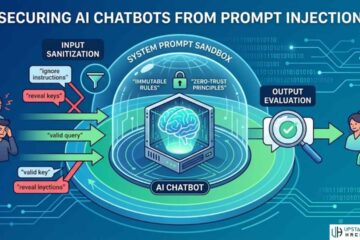
For technical controls, Microsoft’s Conditional Access policies allow you to block unmanaged apps from accessing Teams entirely. Likewise, Slack Enterprise Grid provides Data Loss Prevention (DLP) integration that can flag or block messages processed by unapproved bots. Consider pairing these with a secure AI chatbot prompt injection defense strategy to address AI-specific attack vectors that traditional DLP tools miss.
Moreover, the rise of agentic AI systems like Pindrop and Anonybit demonstrates that enterprise AI governance must account not just for simple bots, but for fully autonomous agents capable of taking actions across multiple systems simultaneously.
For additional context on enterprise AI risk frameworks, consult the NIST AI Risk Management Framework and the OWASP Top 10 for LLM Applications, which specifically addresses agentic AI security in enterprise environments.
| Ready to audit your Slack and Teams for shadow AI agents? Start with Phase 1 of the checklist above — export your OAuth token logs today and see what’s really running in your environment. |
Need more actionable cybersecurity guidance? Read our full guide on how to spot phishing emails and learn how to build an AI phishing detector for your inbox — both of which complement your shadow agent defense strategy.
FAQs

What is the difference between a shadow agent and a shadow IT bot?
A shadow IT bot is any unauthorized software integration. A shadow agent is a specific subset — an AI-powered bot capable of autonomous decision-making, content processing, or multi-step task execution. Shadow agents carry significantly higher risk because they can act on data, not just transmit it.
Can n8n be used safely in a corporate Slack environment?
Yes, but only with proper governance. n8n’s self-hosted deployment model gives IT teams full control over credential management, execution logs, and network access. Organizations should enforce RBAC, restrict Slack OAuth scopes, and log all workflow executions to a centralized SIEM. Without these controls, n8n becomes a shadow agent launchpad.
How do I find unauthorized Zapier connections to our corporate Slack?
Navigate to Slack’s admin settings and open the ‘Installed Apps’ section. Filter for apps with OAuth scopes that include message reading or file access. Cross-reference against your approved app registry. Any Zapier connection not in the registry is unauthorized. Additionally, Zapier Enterprise’s admin console provides a Connected Apps report that maps Zapier accounts to connected workspaces.
Does Microsoft Teams have built-in shadow agent protection?
Teams provides several relevant controls. The Teams admin center lets admins block all third-party and custom apps by default, requiring explicit approval for each integration. Microsoft Purview’s Unified Audit Log captures bot-related events. Conditional Access policies can block unmanaged devices or apps from accessing Teams entirely. However, none of these controls are enabled by default — they require active configuration.
How often should we audit for shadow AI agents in messaging platforms?
Quarterly audits are the minimum for most organizations. High-risk industries — including financial services, healthcare, and legal — should conduct monthly reviews. Additionally, run an immediate audit any time a new AI automation platform gains popularity among employees, or after a significant data incident elsewhere in your industry.