🔄 Last Updated: November 27, 2023
Founder & AI Automation Specialist · Upstanding Hackers
Rana Junaid Shahid is a technology specialist and founder of Upstanding Hackers with over 5 years of hands-on experience in AI automation, no-code workflows, and digital infrastructure. He has built and deployed AI-driven pipelines using tools like Make.com, OpenAI, and no-code AI automation for businesses across multiple industries. His work focuses on making complex emerging technologies practical and accessible — without requiring a developer background. Junaid covers AI agents for business, automation strategy, digital marketing technology, and Web3 infrastructure.
As cyber threats grow more frequent and sophisticated, securing your online presence has become a strategic imperative. Direct connections to the internet expose your IP address, location, browsing habits, and unencrypted data to risks. Utilizing a proxy is a proactive step towards enhancing your online security and preserving the confidentiality of your information.
Using proxy services adds a layer of protection and provides key security advantages. In this article, let’s dive deep into the strategic benefits proxies confer for security. Understanding these advantages enables smarter proxy selection and deployment.
Boost Security: Benefits of Proxy for Online Safety
1. Anonymity and Identity Protection

You might be wondering why proxies play a big role in protecting against threats. Proxies obscure your real IP address and physical location, improving anonymity. This prevents easy tracking and identification by hackers, advertisers, ISPs, or state-level actors. Your online activity becomes much harder to monitor or profile.
Anonymous proxies are especially useful for privacy-sensitive activities like researching controversial topics, accessing blocked content, or maintaining separation between personal and work browsing. To know more about them and their usage, read more>
2. Encrypted Data Transfer
Proxy connections encrypt data between your device and the proxy server, shielding information from packet sniffing or man-in-the-middle attacks. This protects sensitive data like logins, financial transactions, messaging, and site activity in transit over the local network and internet backbone.
Without a proxy, any unencrypted connections on public WiFi, compromised networks, or insecure websites leave your data exposed. But routing through a proxy tunnel secures the data journey and prevents intermediate snooping or capture.
For privacy-conscious users and security best practices, always use a proxy when submitting passwords or sensitive information outside of secure, private networks. This includes email, banking, insurance portals, retail checkouts, and confidential transactions.

3. Access to Restricted Content
One advantage of proxies is allowing access to content blocked due to geographic restrictions or blocklisting. This facilitates unfiltered internet usage and bypasses censorship. Some websites limit content access based on location detected by IP address, such as region-specific streaming video and TV services.
Other sites are deliberately censored or firewalled by repressive local regimes. Routing traffic through a proxy in an allowed region or country provides open access. Journalists, researchers, and academics often leverage proxies to access materials relevant to their work that may otherwise be filtered or blocked.
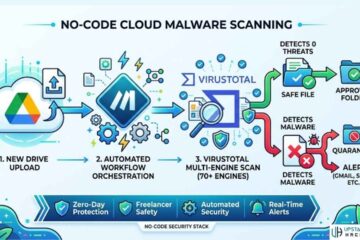
4. Malware and Threat Protection
Proxies isolate your device from malware, phishing scams, drive-by-downloads, and other exploits on accessed sites. By first filtering all traffic through the proxy service, suspicious content and known threats can be screened to reduce risk.
Direct exposure when browsing can lead to malware infiltration, harmful downloads, credential theft via phishing pages, and injection of malicious scripts into your live sessions. But proxies function as intermediaries that handle and scan that traffic before delivery.
This protection is useful both for personal browsing and for enterprise security. Businesses can mandate that remote workers funnel web access through proxies to limit risks from compromised sites.

5. Advanced Network Security
Robust proxies like corporate VPNs incorporate threat protection, intrusion prevention, tunneling, and other features to strengthen network security above basic proxies. This builds on the inherent access control of proxy architecture.
Secure web gateways, next-gen firewalls, threat intelligence feeds, active malware prevention, data loss prevention, and advanced analytics can all be integrated with enterprise proxy solutions. This provides layered inspection and defense tailored to larger organizations.
For global companies, strategic placement of proxy servers also allows traffic management, load balancing, failover capabilities, and congestion avoidance while maintaining security. Proxies become integral components in comprehensive security frameworks.
6. Consistent Connection Origin
Proxies maintain a consistent connection origin so your traffic doesn’t raise flags from different locations, varied IP addresses, or suspicious geographic patterns. This avoids account security measures that trigger lockouts or blocks.
Banks and service providers often deactivate accounts if logins come from rare locations for that user, signaling a potential breach. But proxies funnel the connection through one consistent entry point. This prevents account flagging when traveling or on mobile. Rotating proxy services, in particular, facilitate access automation while avoiding blocks. The traffic appears from consistent IPs versus hundreds of end-user devices directly connecting.
7. Mobile Device Security
Routing mobile traffic through a proxy or VPN protects those vulnerable devices from threats and snooping while on cellular networks or public WiFi. Smaller smartphones and tablets are more easily compromised than PCs when connecting directly.
Given the sensitive nature of mobile usage for email, social media, banking, and work applications, it’s critical to shield those devices as much as possible from risk exposure. Proxies provide an encrypted tunnel for all mobile traffic to keep data secure.
Personal VPNs, mobile proxies, enterprise mobile device management tunnels, and other options exist to proxy-enable smartphones, tablets, and laptops outside the office. This reduces the attack surface.

8. Cost-Effective Security Scaling
Shared proxies reduce expenses for organizations by multiplexing many users through a common pool of IPs. Load balancing, access controls, and usage limits allow cost-efficient security at scale.
Buying fixed, dedicated proxies for each employee would be extremely expensive. However, shared rotating proxy services grant private tunneling with flexible user controls. Organizations can scale security up or down cost-effectively.
To maximize value, combine shared proxy services for general browsing with select dedicated proxies for privacy-sensitive connections, account access, or restricted systems. The hybrid approach balances cost, security, and performance.
Final Thoughts: Gain a Powerful Strategic Advantage with Proxy
As cyber threats accelerate, security can no longer be an afterthought. Proxies offer a versatile way to improve threat protection, anonymity, privacy, access, etc. By understanding the key advantages of proxies, you can incorporate them into your larger security strategy for significant benefit.
Don’t leave your online assets and activity unnecessarily exposed. Implement the right proxy solution to gain a powerful strategic advantage for your organization.
See Also: Everything You Need to Know About Chatbots for Business