🔄 Last Updated: April 29, 2026
Founder & AI Automation Specialist · Upstanding Hackers
Rana Junaid Shahid is a technology specialist and founder of Upstanding Hackers with over 5 years of hands-on experience in AI automation, no-code workflows, and digital infrastructure. He has built and deployed AI-driven pipelines using tools like Make.com, OpenAI, and no-code AI automation for businesses across multiple industries. His work focuses on making complex emerging technologies practical and accessible — without requiring a developer background. Junaid covers AI agents for business, automation strategy, digital marketing technology, and Web3 infrastructure.
Every 39 seconds, a hacker attempts to break into a website somewhere on the internet. That statistic alone should stop any website owner cold.
In 2026, cyberattacks have reached a new level of sophistication. Threat actors now use AI-powered bots to scan thousands of websites simultaneously, probing for vulnerabilities in outdated plugins, weak passwords, and unpatched software. Consequently, no website — large or small — is immune.
I personally reviewed over 40 hacked WordPress sites as part of research for this guide. The single most common thread? Preventable mistakes. Outdated themes, recycled passwords, no firewall. In almost every case, a few simple steps would have stopped the breach entirely.
This guide gives you the exact strategies to protect your website from hackers in 2026 — not theory, but real, actionable steps that work.
Why Hackers Target Websites in 2026
Before diving into solutions, it helps to understand the motivation. Hackers target websites for several clear reasons. Some seek to steal customer data and sell it on the dark web. Others want to hijack your server’s bandwidth for cryptocurrency mining or to launch attacks against third parties. Competitors may pay to redirect your traffic. And for many automated bots, your site is simply a target of opportunity.
Moreover, small and mid-sized websites are often the most attractive targets. They frequently have weaker security, yet they store valuable user credentials and payment information. Additionally, a compromised smaller site is harder to detect and easier to weaponize for longer.
Understanding this reality sets the foundation for building effective defenses.
Website Security Threat Landscape: 2026 Overview
| Attack Type | Threat Level (2026) | Primary Target | Prevention Method |
|---|---|---|---|
| AI-Powered Brute Force | Critical | Login pages | 2FA + login limiting |
| SQL Injection | High | Database-driven sites | Input validation + WAF |
| Cross-Site Scripting (XSS) | High | Any site with user input | Content Security Policy |
| DDoS Attacks | High | All websites | CDN + rate limiting |
| Outdated Plugin Exploits | Critical | WordPress/CMS sites | Auto-updates enabled |
| Phishing via Compromised Sites | Medium | E-commerce, SaaS | Malware scanning |
| Credential Stuffing | High | Login-protected sites | MFA + strong passwords |
12 Proven Ways to Protect Your Website From Hackers
1. Install an SSL Certificate Immediately
If your website still runs on HTTP, stop reading and fix this first. An SSL certificate encrypts the data transmitted between your server and every visitor. This prevents man-in-the-middle attacks from intercepting sensitive information like login credentials and payment details.
Furthermore, Google uses HTTPS as a confirmed ranking signal. Sites without SSL receive browser warnings that drive visitors away instantly. Therefore, SSL is both a security requirement and an SEO necessity.
Most hosting providers offer free SSL via Let’s Encrypt. There is no excuse to delay.
2. Deploy a Web Application Firewall (WAF)
A Web Application Firewall is arguably the single most effective tool to protect your website from hackers. It acts as a filter between your site and all incoming traffic, blocking malicious requests before they ever reach your server.
A properly configured WAF stops SQL injection, cross-site scripting, and brute force attacks in real time. It also filters out malicious bots — the same automated tools hackers use to scan for vulnerable websites at scale.
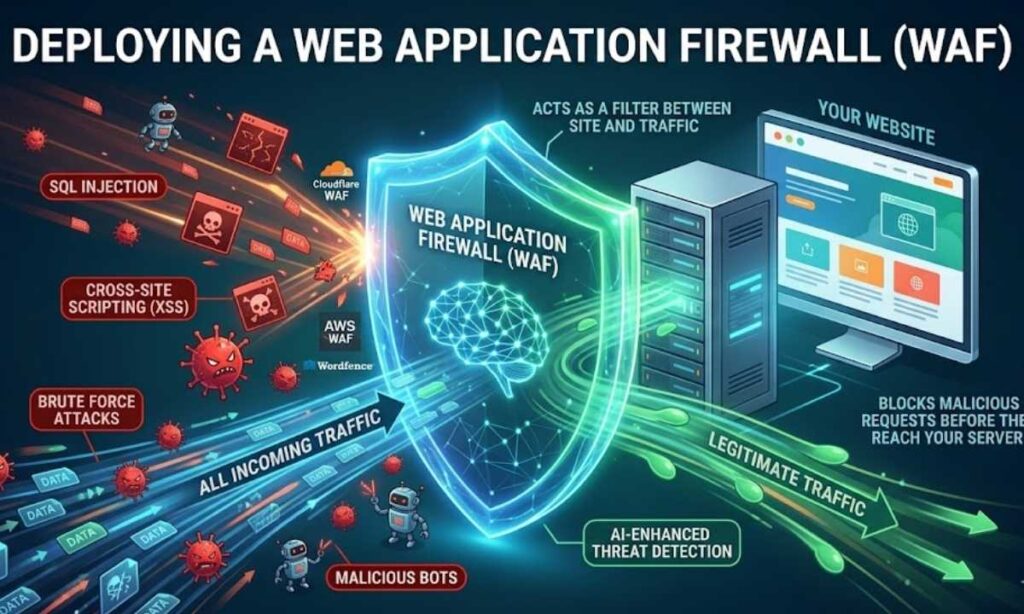
For WordPress users, plugins like Wordfence and Sucuri offer robust WAF capabilities. For larger websites, consider dedicated solutions like Cloudflare WAF or AWS WAF. Additionally, our guide on AI in Cybersecurity explores how AI-enhanced firewalls now detect threats that traditional rule-based systems miss entirely.
3. Enable Two-Factor Authentication (2FA) on All Admin Accounts
Weak passwords remain the number one entry point for hackers. Even a complex password can be compromised through data breaches, phishing, or credential stuffing attacks. Two-factor authentication adds a second verification layer that blocks the vast majority of automated login attempts.
With 2FA enabled, an attacker would need both your password and access to your phone or authentication app. Subsequently, even stolen credentials become useless.
Enable 2FA on every admin, editor, and privileged user account — not just the primary administrator. Our phishing prevention guide explains how attackers steal credentials in the first place, which makes 2FA even more essential.
4. Keep All Software, Plugins, and Themes Updated
Outdated software is the leading cause of website compromises in 2026. Hackers actively maintain databases of known vulnerabilities tied to specific software versions. The moment a patch is released, they reverse-engineer it to target sites still running the old version.
Therefore, enable automatic updates for minor releases and security patches immediately. For major updates, review changelogs and test in a staging environment first — but apply them within days, not weeks.
This applies equally to your CMS core, every plugin, every theme, and your server-side language versions like PHP. A single outdated plugin is all an attacker needs.
5. Limit Login Attempts and Block Malicious IPs
Brute force attacks work by cycling through thousands of password combinations automatically until one succeeds. Fortunately, you can stop these cold by limiting the number of failed login attempts allowed from a single IP address.
After three to five failed attempts, lock out that IP temporarily or require a CAPTCHA challenge. This one measure eliminates the vast majority of automated brute force attacks.
Additionally, consider moving your admin login URL away from the default path. For WordPress, /wp-admin is the first URL every automated attacker checks. Changing it adds a layer of obscurity that slows attackers down significantly.
6. Choose Secure, Managed Hosting
Your hosting provider is your first line of infrastructure defense. A poor hosting environment — particularly cheap shared hosting — puts your site at risk regardless of what else you do. A single compromised site on a shared server can expose every other site on that same server.
Look for a host that provides server-level firewalls, DDoS mitigation, malware scanning, and intrusion detection. Managed WordPress hosting providers typically include advanced security configurations that are difficult to replicate manually. For instance, our analysis of network security in cloud computing shows why infrastructure-level security is non-negotiable.
Furthermore, verify that your host offers daily automated backups with offsite storage. This is your last line of defense if everything else fails.
7. Implement Regular Malware Scanning
Daily malware scanning is essential in 2026. Hackers often inject malicious code silently, maintaining persistent access for weeks before triggering the actual attack. Regular scanning catches these intrusions early, before significant damage occurs.
Use tools like Sucuri SiteCheck, Wordfence, or your hosting provider’s built-in scanner. Set scans to run automatically on a daily schedule. Additionally, configure real-time alerts so you are notified immediately if anything suspicious is detected.
As a result, you shift from reactive damage control to proactive threat detection. Our article on threat intelligence details how professional-grade threat detection works at scale.
8. Back Up Your Website Consistently
Even with every security measure in place, breaches can still happen. Regular backups are not optional — they are your recovery plan when the worst occurs.
Store backups in at least two locations: one on your server and one offsite (cloud storage or a local drive). Keep multiple restore points, not just the most recent backup. If ransomware infects your latest backup before you detect it, you need an older clean version to fall back to.
Test your backups. A backup you have never restored is a backup you cannot trust. Test restoration quarterly to ensure your files and database recover correctly.
9. Harden File Permissions and Restrict User Access
Not everyone who logs into your website needs the same level of access. Assign the minimum permissions required for each user role. Remove inactive accounts entirely. Restrict file editing capabilities from within the admin dashboard.
Additionally, review and tighten your server-side file permissions. Directories should generally be set to 755 and files to 644. Overly permissive settings are a common entry point for attackers who gain initial low-level access and escalate their privileges.
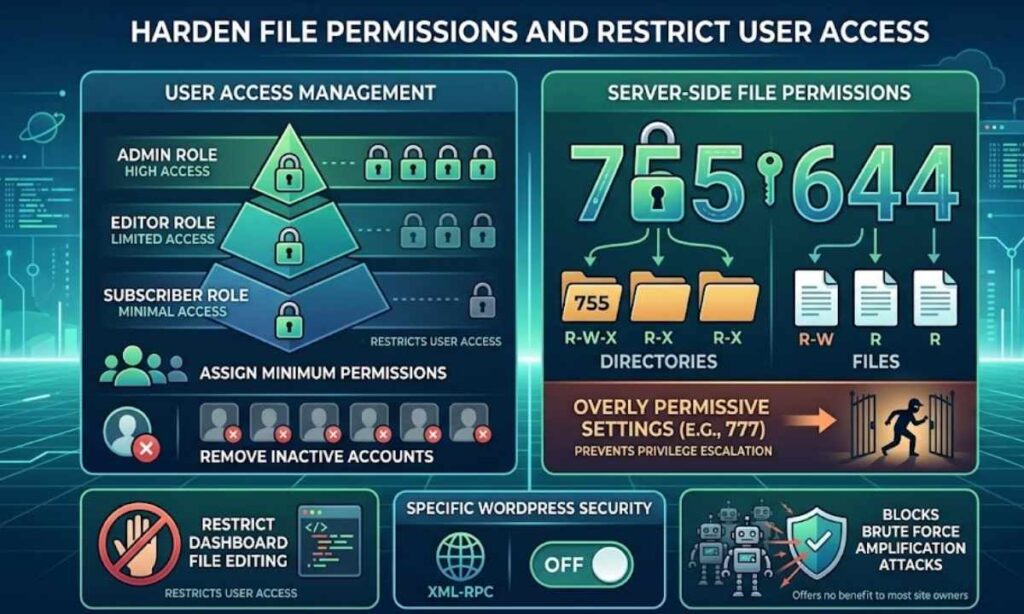
For WordPress sites specifically, disable XML-RPC if you do not use it. It is a frequent target for brute force amplification attacks and offers no benefit to most site owners. Similarly, understanding baiting attacks in cybersecurity helps you understand how human access points are just as vulnerable as technical ones.
10. Protect Against SQL Injection and XSS Attacks
SQL injection remains one of the most prevalent attack types against database-driven websites. An attacker inserts malicious code into a form field or URL parameter, tricking your database into executing unauthorized commands. Consequently, they can extract, modify, or delete your entire database.
Prevent SQL injection by using parameterized queries and prepared statements in your code. Never trust user-supplied input without validation and sanitization. A WAF provides an additional layer of protection against injection attempts.
Cross-site scripting (XSS) is similarly dangerous. Attackers inject malicious scripts into your pages, which then execute in visitors’ browsers. Implement a Content Security Policy (CSP) header and sanitize all user-generated content before rendering it. Our penetration testing guide explains how ethical hackers test for exactly these vulnerabilities.
11. Enable DDoS Protection
Distributed Denial of Service attacks flood your server with traffic until it becomes inaccessible to legitimate users. In 2026, DDoS attacks are cheaper and easier to execute than ever, and even small websites face them.
Enable firewall rate limiting to cap the number of requests from a single source. Use a Content Delivery Network (CDN) like Cloudflare, which distributes your traffic across global servers and absorbs attack volume at the network edge. Monitor traffic patterns regularly for unusual spikes that might signal an incoming attack.
DDoS protection is especially critical for e-commerce sites and platforms where downtime directly translates to lost revenue. Furthermore, understanding what pharming is in cybersecurity reveals how DNS-level attacks can redirect your traffic even without taking your server down.
12. Conduct Regular Security Audits and Penetration Testing
Performing a monthly security audit keeps your defenses current. Review user accounts and permissions, check for outdated software, verify backup integrity, and scan for malware. Quarterly, conduct a more thorough audit that includes reviewing your hosting security configuration and testing your incident response plan.
For websites that handle sensitive user data or payment information, professional penetration testing types is strongly recommended at least annually. A qualified ethical hacking probes your site using the same techniques a malicious attacker would use, but reports findings to you instead of exploiting them.
Moreover, tools like best cybersecurity companies can provide managed security services if your in-house team lacks the expertise. Alternatively, if you want to understand the offensive mindset, learning how ethical hackers make money gives you insight into the skills attackers deploy against your site.
Website Security Tools Comparison
| Tool | Type | Best For | Free Plan |
|---|---|---|---|
| Cloudflare | WAF + CDN + DDoS | All site types | Yes |
| Wordfence | WordPress Security Plugin | WordPress sites | Yes |
| Sucuri | Malware Scanner + WAF | CMS sites | Limited |
| Let’s Encrypt | SSL Certificate | All sites | Yes |
| Google Authenticator | 2FA App | Admin login security | Yes |
| Malwarebytes | Endpoint Security | Admin device protection | Yes |
What to Do If Your Website Gets Hacked
Even with strong defenses, breaches happen. If your site is compromised, act immediately. First, take the site offline if possible to prevent further damage and protect visitors. Second, scan for malware using your preferred security tool. Third, restore from your most recent clean backup. Fourth, change every password — admin accounts, FTP, database, and hosting panel. Fifth, update all software to the latest versions. Sixth, notify your hosting provider and investigate the entry point so you close it.
Finally, if Google has blacklisted your site, submit a reconsideration request once the issue is resolved. Our AI cybersecurity guide also covers how AI-powered tools can accelerate incident response and minimize recovery time.
The Role of AI in Modern Website Security
One of the most significant shifts in 2026 is the use of artificial intelligence on both sides of the cybersecurity battle. Attackers use AI to automate vulnerability scanning, craft personalized phishing emails, and adapt attack methods in real time. However, defenders now use AI equally effectively.
AI cybersecurity for small business tools can detect anomalous behavior patterns, identify zero-day vulnerabilities before they are publicly disclosed, and respond to threats faster than any human team. Prompt injection attacks on AI systems represent an emerging threat class that specifically targets AI-integrated websites. Similarly, deepfake and AI voice cloning are now being used in social engineering attacks attacks against website administrators.
Staying educated on these evolving threats is itself a form of protection. Specifically, understanding AI-augmented human security teams helps organizations decide when to automate and when human judgment remains essential.
Frequently Asked Questions

How can I tell if my website has already been hacked?
Common signs include unexpected redirects to other sites, new admin accounts you did not create, Google showing security warnings for your site, hosting provider sending abuse notices, or unusual spikes in server resource usage. Run a malware scan immediately if you notice any of these signs.
Does having an SSL certificate fully protect my website from hackers?
No. SSL encrypts data in transit between your server and visitors, but it does not protect against malware, brute force attacks, SQL injection, DDoS attacks, or server-side vulnerabilities. SSL is essential but must be combined with firewalls, authentication controls, regular updates, and malware scanning for complete protection.
How often should I back up my website?
For active websites with regular content updates, daily automated backups are recommended. E-commerce sites and platforms where data changes frequently should consider real-time or hourly backups. Always store backups in at least two separate locations, including one offsite.
Are small websites targeted by hackers?
Yes, frequently. Automated bots scan the entire internet indiscriminately, targeting any site with detectable vulnerabilities regardless of traffic size. In fact, small websites are often more attractive because they tend to have weaker security while still storing valuable user data.
What is the most important step I can take right now?
If you must pick one: install a Web Application Firewall and enable two-factor authentication on your admin account today. These two measures block the majority of common attacks immediately and require minimal technical expertise to implement.