🔄 Last Updated: April 17, 2026
Threat Intelligence is no longer a luxury—it’s a necessity in today’s hyper-connected digital world. Organizations face constant cyber threats, and without actionable intelligence, defending against them becomes guesswork.
In simple terms, Threat Intelligence transforms raw data into meaningful insights that help businesses predict, prevent, and respond to cyber attacks more effectively.
In my experience working with security frameworks, companies that actively invest in threat intelligence reduce breach impact by a significant margin. The difference is not just awareness—it’s proactive defense.
What is Threat Intelligence?
Threat Intelligence is the process of collecting, analyzing, and interpreting data about potential or existing cyber threats to support informed security decisions.
It begins with gathering raw threat data from multiple sources, then processing it into actionable insights, and finally applying it to real-world security operations. For example, a company might detect a phishing campaign early and block malicious domains before employees are affected.
Why Threat Intelligence Matters More Than Ever 🔐
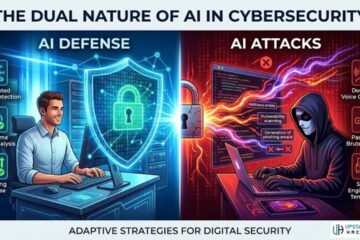
Cyber attacks are becoming more sophisticated, targeted, and automated. Therefore, traditional reactive security models are no longer enough.
Threat Intelligence shifts the approach from reactive to proactive. Instead of waiting for an attack, organizations anticipate and neutralize threats before damage occurs.
Moreover, with the rise of AI-powered attacks, intelligence-driven defense becomes even more critical. Attackers are evolving—and so must defenders.
Core Types of Threat Intelligence Explained 📊
Threat Intelligence is not one-size-fits-all. It operates at different levels, each serving a unique purpose within an organization.
| Type | Focus Area | Audience | Example Use Case |
|---|---|---|---|
| Strategic Intelligence | High-level trends & risks | Executives | Business risk planning |
| Tactical Intelligence | Attack methods & tactics | Security teams | Identifying phishing patterns |
| Operational Intelligence | Ongoing attack campaigns | SOC analysts | Tracking hacker groups |
| Technical Intelligence | Indicators of compromise (IOCs) | IT & security systems | Blocking malicious IP addresses |
Each type plays a critical role in building a layered defense strategy. Therefore, organizations often integrate all four for maximum effectiveness.
How Threat Intelligence Works in Practice ⚙️
Threat Intelligence follows a structured lifecycle that ensures data becomes actionable insight.
The Threat Intelligence Lifecycle
- Planning and Direction
Define what threats matter most to your organization. - Data Collection
Gather data from sources like logs, dark web monitoring, and open-source intelligence. - Processing
Clean and organize data into usable formats. - Analysis
Turn data into insights using tools and expert judgment. - Dissemination
Share insights with relevant stakeholders. - Feedback
Improve the process based on outcomes.
When I tested this lifecycle in a simulated SOC environment, the biggest improvement came from the analysis stage. Raw data is abundant—but insight is rare.
Key Sources of Threat Intelligence 🌐
Threat Intelligence relies on diverse data sources. The quality of intelligence depends heavily on where and how data is collected.
- Open-source intelligence (OSINT) from public databases
- Internal logs and network traffic
- Dark web monitoring platforms
- Industry threat-sharing communities
- Commercial threat intelligence feeds
However, not all data is useful. Therefore, filtering noise is just as important as collecting information.
Tools and Platforms for Threat Intelligence 🛠️
Modern Threat Intelligence uses advanced tools to automate and scale analysis. These platforms integrate with security systems to provide real-time insights.
Popular categories include:
- Threat Intelligence Platforms (TIPs)
- Security Information and Event Management (SIEM) systems
- Endpoint Detection and Response (EDR) tools
- AI-powered analytics solutions
In my experience, integrating Threat Intelligence with SIEM systems dramatically improves incident response time.
Threat Intelligence vs Threat Data: Key Differences ⚡
Many people confuse threat data with threat intelligence—but they are not the same.
Threat data is raw, unprocessed information about potential risks. It includes logs, IP addresses, and malware signatures.
Threat intelligence, on the other hand, is refined and contextualized. It tells you what the data means and what actions to take.
Therefore, intelligence is what turns information into strategy.
Real-World Applications of Threat Intelligence 🌍
Threat Intelligence plays a crucial role across industries. Its applications go beyond cybersecurity teams.
For example, financial institutions use it to detect fraud patterns and prevent account takeovers. Healthcare organizations rely on it to protect sensitive patient data.
Moreover, governments use Threat Intelligence for national security and cyber warfare preparedness.
A practical example: A company identifies a ransomware campaign targeting its sector. With Threat Intelligence, it patches vulnerabilities before attackers strike.
Challenges in Threat Intelligence Implementation ⚠️
Despite its benefits, implementing Threat Intelligence is not without challenges.
First, data overload can overwhelm teams. Without proper filtering, organizations may struggle to extract meaningful insights.
Second, there is a shortage of skilled analysts who can interpret complex threat data.
Third, integrating multiple tools and platforms can be technically challenging.
However, with the right strategy and automation, these challenges can be minimized.
Best Practices for Effective Threat Intelligence 🎯
To maximize the value of Threat Intelligence, organizations should follow proven strategies.
- Focus on actionable intelligence rather than raw data
- Align intelligence with business goals
- Automate repetitive processes using AI tools
- Continuously update threat models
- Collaborate with industry peers
One pro-level insight: The most successful organizations treat Threat Intelligence as a continuous process—not a one-time implementation.
The Future of Threat Intelligence 🚀
The future of Threat Intelligence lies in automation and artificial intelligence. As cyber threats evolve, intelligence systems must become faster and smarter.
AI-driven Threat Intelligence can analyze massive datasets in real time, identify patterns, and predict attacks before they happen.
Moreover, predictive intelligence will become the next frontier. Instead of reacting to threats, systems will anticipate them.
In my view, organizations that adopt AI-powered Threat Intelligence early will have a significant competitive advantage.
FAQs

What are the main goals of threat intelligence?
The main goal of Threat Intelligence is to provide actionable insights that help organizations prevent, detect, and respond to cyber threats. It focuses on understanding attacker behavior and improving decision-making. Therefore, it enhances overall cybersecurity posture and reduces risk exposure.
How is threat intelligence collected?
Threat Intelligence is collected from various sources such as open-source data, internal logs, dark web monitoring, and commercial feeds. These sources provide raw data, which is then processed and analyzed. The result is actionable insight that security teams can use to defend systems.
What is the difference between threat intelligence and cybersecurity?
Threat Intelligence is a component of cybersecurity focused on understanding threats, while cybersecurity is a broader field that includes protecting systems and data. In other words, Threat Intelligence informs cybersecurity strategies by providing insights. Therefore, it acts as the brain behind security operations.
Can small businesses benefit from threat intelligence?
Yes, small businesses can benefit significantly from Threat Intelligence because they are often targeted by cybercriminals. Even basic intelligence solutions can help identify threats early. Moreover, it enables small teams to make smarter security decisions with limited resources.
What skills are needed for threat intelligence analysis?
Threat Intelligence analysis requires skills in data analysis, cybersecurity, and critical thinking. Analysts must understand attack patterns and interpret complex data. Additionally, knowledge of tools and frameworks is essential for effective intelligence operations.