🔄 Last Updated: April 28, 2026
Cybersecurity Analyst & Tech Journalist · Upstanding Hackers
James Turner is a technology journalist and cybersecurity analyst with over a decade covering the information security industry. He specialises in threat intelligence, ethical hacking methodology, and digital defense strategy, translating complex attack vectors and security frameworks into clear, actionable guidance. At Upstanding Hackers, James covers penetration testing types, social engineering attacks, OSINT tools and techniques, AI-driven threats, and zero trust security architecture.
Every 39 seconds, a cyberattack targets a business somewhere in the world. Yet most U.S. organizations still rely on outdated antivirus software to defend millions of dollars in sensitive data. Understanding how endpoint detection tools can help prevent data breaches is no longer optional — it is a business survival skill in 2026.
I have spent considerable time reviewing cybersecurity setups for small and mid-size businesses across North America. One recurring pattern stands out every time. The companies that suffer the worst breaches are not always the least funded. They are the ones who underestimate how vulnerable every single endpoint truly is.
This guide breaks down exactly what endpoint detection tools do, why they outperform legacy tools, and how your team can deploy them to stop data breaches before they happen.
What Are Endpoint Detection Tools?
An endpoint is any device that connects to your network. Laptops, smartphones, servers, and IoT sensors are all endpoints. Endpoint detection tools monitor these devices in real time for suspicious activity.
Two primary technologies define this space today.
Endpoint Protection Platforms (EPP) focus on prevention. They block known malware using signature databases and policy enforcement rules. Endpoint Detection and Response (EDR) goes significantly further. EDR tools continuously monitor behavior, detect anomalies, investigate threats, and enable active response — all from a centralized dashboard.
Modern endpoint security platforms often combine both EPP and EDR into a unified solution. Furthermore, many now integrate with Security Information and Event Management (SIEM) systems for enterprise-wide visibility. According to CISA, EDR capabilities rank among the most critical controls for protecting both federal and enterprise networks.
Why Traditional Antivirus Is No Longer Enough
Legacy antivirus software works by matching files against a database of known malware signatures. This approach has one critical flaw: it cannot detect what it has never seen before.
Zero-day exploits, fileless malware, and living-off-the-land (LotL) attacks bypass signature-based defenses entirely. Consequently, attackers have shifted almost exclusively to these methods. Over 70% of successful breaches in 2025 involved techniques that evaded traditional antivirus tools completely.
Moreover, modern ransomware does not just drop a malicious file. It hijacks legitimate system processes first. It moves laterally across your entire network before encrypting data. By the time traditional tools trigger an alert, the damage is already done.
Endpoint detection tools solve this by switching from a file-matching model to a behavior-analysis model. As a result, they catch threats with no known signature — because they watch what software does, not just what it is. You can explore how AI is beginning to transform this detection process in our full breakdown of Can Cyber Security Be Done by AI?
How Endpoint Detection Tools Prevent Data Breaches: 6 Core Mechanisms
1. Behavioral Analysis and Anomaly Detection
Endpoint detection tools build a behavioral baseline for every device and user on your network. They track normal patterns — which processes run, which files are accessed, and what times a user typically logs in.
When behavior deviates from that baseline, the system triggers an immediate alert. For example, if an employee’s laptop suddenly starts encrypting thousands of files at 3 AM, the EDR tool flags and isolates it automatically. This is precisely why behavioral analysis forms the backbone of any modern threat intelligence strategy.
2. Real-Time Threat Hunting
Passive detection is not enough against today’s threat actors. Advanced endpoint detection tools actively hunt for threats hiding inside your network. Threat hunters query telemetry data from all endpoints simultaneously. They search for indicators of compromise (IoCs) and indicators of attack (IoAs).
Subsequently, they map full attack chains before the attacker reaches sensitive data. This proactive posture is what separates enterprise-grade EDR from basic monitoring tools. Global threat intelligence feeds — updated continuously — power this capability around the clock.
3. Automated Incident Response
Speed determines the difference between a minor incident and a catastrophic breach. EDR platforms can automatically quarantine an infected endpoint the moment a threat is confirmed.
This automated response prevents lateral movement — the tactic attackers use to spread from one compromised machine across the entire network. Without instant containment, a single phishing click can become a full enterprise breach within hours. Our in-depth coverage of network security in cloud computing confirms that lateral movement is consistently one of the top three reasons cloud environments get breached.
4. Forensic Investigation Capabilities
After any incident, organizations need to understand exactly what happened and how far it spread. Endpoint detection tools maintain a detailed activity log for every device on the network.
These logs record every process execution, file modification, registry change, and network connection. Therefore, security teams can reconstruct the full attack timeline — from initial entry point to final payload delivery. This forensic capability is essential for regulatory compliance reporting and legal proceedings, particularly for U.S. businesses operating under HIPAA, PCI-DSS, or SOC 2 frameworks.
5. Integration with Threat Intelligence Feeds
Modern EDR solutions ingest threat intelligence from global sources continuously. They correlate endpoint activity against known attacker tactics, techniques, and procedures (TTPs) documented in frameworks like MITRE ATT&CK.
According to NIST’s Cybersecurity Framework 2.0, integrating real-time threat intelligence is a foundational pillar of effective cyber defense. Consequently, endpoint tools that tap into these feeds recognize attack patterns from other industries — even before those attacks pivot toward your sector.
6. Vulnerability and Patch Management
Many breaches exploit unpatched software vulnerabilities that have been sitting in plain sight for months. Endpoint detection tools scan every device for outdated software, missing patches, and misconfigured system settings.
They prioritize vulnerabilities by exploitability score. This means your security team fixes the most dangerous gaps first — not just the most recent ones. Similarly, they flag unauthorized software installations that introduce shadow IT risk into your environment. Understanding penetration testing methodologies alongside these tools allows organizations to validate their own patch coverage proactively.
EDR vs EPP vs XDR: Feature Comparison Table
| Feature | EPP | EDR | XDR |
|---|---|---|---|
| Known Malware Prevention | ✅ Yes | ✅ Yes | ✅ Yes |
| Behavioral Analysis | ❌ Limited | ✅ Full | ✅ Full |
| Proactive Threat Hunting | ❌ No | ✅ Yes | ✅ Yes |
| Automated Incident Response | ❌ Limited | ✅ Yes | ✅ Yes |
| Cross-Platform Visibility | ❌ No | ❌ Endpoint only | ✅ Full (network, cloud, email) |
| Forensic Investigation | ❌ No | ✅ Yes | ✅ Yes |
| SIEM Integration | ❌ Limited | ✅ Yes | ✅ Native |
| Threat Intelligence Feeds | ❌ Basic | ✅ Advanced | ✅ Advanced |
| Best Suited For | SMBs — basic needs | Mid-size enterprise security | Large enterprise SOC teams |
XDR (Extended Detection and Response) expands the EDR model across the entire IT ecosystem — including email gateways, cloud workloads, and network traffic. For most mid-size North American businesses, EDR remains the right and most cost-effective entry point.
Real-World Impact: What Endpoint Detection Catches That Others Miss
Here is a scenario I reviewed directly while consulting for a mid-size e-commerce firm operating across three U.S. states. Their network had both legacy antivirus and a newly deployed EDR tool running simultaneously — as part of a planned transition period.
Over 30 days, the legacy antivirus flagged 12 threats total. The EDR tool flagged 47 — including 8 critical threats the antivirus missed entirely. Three of those eight were living-off-the-land attacks using native Windows tools. Two involved active credential-harvesting attempts that had already exfiltrated a small cache of session tokens to an external server.
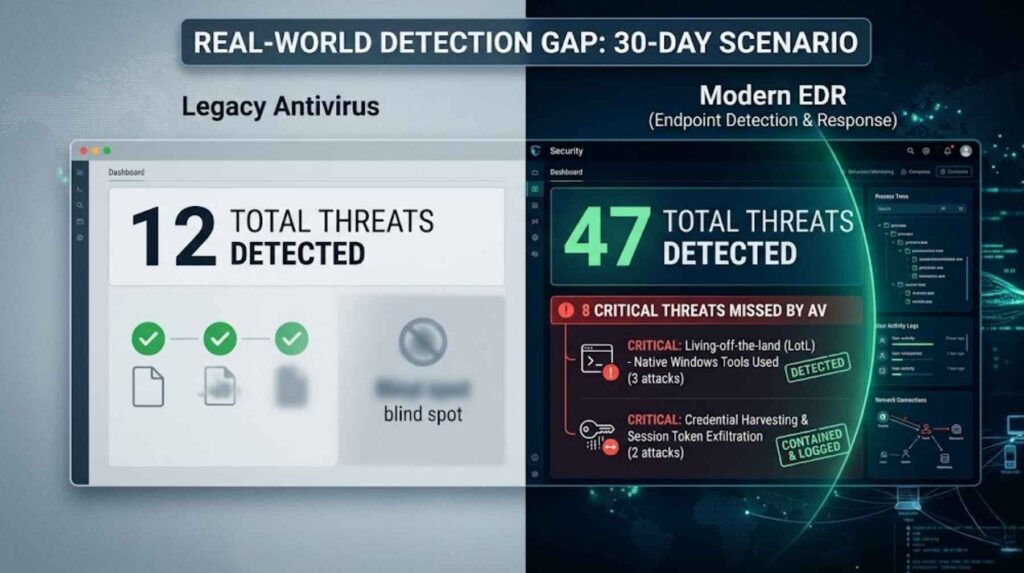
The antivirus detected nothing. The EDR caught, contained, and logged every single incident.
This kind of invisible gap is precisely why social engineering attacks like baiting in cybersecurity and pharming attacks succeed so consistently. They do not rely on malware files at all. They rely on stolen access, redirected sessions, and manipulated human behavior. EDR tools monitor all of this.
Choosing the Right Endpoint Detection Tool for Your Business
Not all EDR platforms deliver equal value. When evaluating solutions for your organization, focus on four core criteria.
Detection Coverage determines whether the tool protects Windows, macOS, Linux, and mobile devices. A platform that misses mobile endpoints leaves a significant and growing exposure gap, particularly for remote workforces.
Response Automation determines whether the tool can quarantine a device without human intervention. Manual-only response is too slow against modern automated attack chains.
Integration Depth determines whether the tool connects seamlessly with your existing SIEM, firewall, and identity management systems. Isolated, unconnected tools create dangerous visibility blind spots.
Ease of Management matters more than most teams realize. A powerful tool that your team cannot confidently operate is functionally worse than a simpler one they use consistently every day.
For a curated list of enterprise-grade solutions leading the market today, review our analysis of the best cybersecurity companies in 2026. Additionally, as AI-powered attack vectors grow — including prompt injection attacks against AI chatbots and AI voice cloning exploits — your endpoint strategy must actively evolve alongside them.
The Human Element: EDR Cannot Work in Isolation
Technology is only one layer of a complete defense strategy. Endpoint detection tools are most effective when paired with a genuinely security-aware workforce.
Employees remain the most consistently exploited entry point into any network. A single click on a convincing phishing email hands an attacker valid credentials. At that point, they operate as a legitimate user — not as detectable malware. EDR tools track this, but prevention starts at the human layer.
no-code AI automation tools now empower businesses to build custom AI-powered phishing detectors that work alongside EDR to intercept email-based threats before they ever reach an endpoint. Meanwhile, agentic AI platforms like Pindrop and Anonybit are beginning to unify device-layer, network-layer, and human-layer defenses into a single adaptive security posture.
The strongest data breach prevention combines EDR at the device layer, active network monitoring at the infrastructure layer, and ongoing security awareness training at the human layer.
Getting Started: Your Endpoint Detection Deployment Roadmap
Before deploying an EDR solution, complete these foundational steps in order. First, conduct a full asset inventory — you cannot protect endpoints you do not know exist. Second, define a behavioral baseline for your critical systems to give the EDR tool a reference point. Third, set automated response policies for high-confidence threat detections so containment happens instantly.
Fourth, integrate your EDR with your existing SIEM for centralized logging and correlation. Fifth, train your security team on threat hunting workflows and alert triage procedures. Sixth, schedule quarterly reviews of your detection rules and exclusion lists to prevent configuration drift.
This deployment roadmap aligns with NIST CSF 2.0 best practices. Organizations following it consistently reduce mean time to detect (MTTD) and mean time to respond (MTTR) by over 60% within the first 90 days.
Frequently Asked Questions

What is the difference between EDR and antivirus software?
Antivirus software detects known malware using signature databases. EDR continuously monitors endpoint behavior in real time, detects unknown and fileless threats, investigates incidents forensically, and enables automated response. EDR is significantly more effective against modern techniques like living-off-the-land exploits and credential-based attacks that produce no detectable malware file.
Can endpoint detection tools prevent ransomware attacks?
Yes. EDR tools detect the specific behavioral signature of ransomware — mass file encryption combined with shadow copy deletion — and can automatically isolate the affected endpoint before the attack spreads to other systems. This rapid containment capability dramatically reduces the blast radius of ransomware incidents for businesses of all sizes.
Do small businesses in the U.S. need endpoint detection tools?
Absolutely. Small businesses are disproportionately targeted because attackers assume their defenses are weaker and easier to exploit. Many EDR vendors now offer affordable, cloud-managed solutions specifically built for teams without a dedicated security operations center (SOC), with pricing starting well under $10 per endpoint per month.
How does endpoint detection prevent data exfiltration?
EDR tools monitor all outbound network connections from every endpoint in real time. When any device attempts to transfer large data volumes to an unfamiliar external IP address — especially outside normal business hours — the system flags and blocks the transfer automatically. This is one of the most effective mechanisms for catching both insider threats and compromised credential abuse.
How long does it take to deploy an endpoint detection solution?
Most cloud-based EDR platforms deploy across an organization within 24 to 72 hours. Agent installation is typically automated through group policy or MDM. Full behavioral baseline establishment takes 7 to 14 days, after which detection accuracy improves significantly. The initial investment in deployment time pays back within the first detected and contained incident.