🔄 Last Updated: April 29, 2026
Most people hear the word “hacker” and think crime. The reality is far more interesting. Ethical hackers protect companies, governments, and millions of users worldwide. This complete How To Become A Hacker Guide For Beginners gives you a structured, legal, and practical roadmap to break into cybersecurity in 2026.
I remember starting out with nothing but curiosity and a slow laptop. I installed Kali Linux for the first time. I typed a command into the terminal and immediately broke my virtual machine. That was the best lesson I ever had. Consequently, this guide will save you those painful early mistakes. You will learn the right foundations first, the right tools second, and the right mindset throughout.
Furthermore, the cybersecurity industry desperately needs talent. The global shortage of cybersecurity professionals currently exceeds 4 million workers. As a result, the doors are wide open for committed beginners. Let us walk through every step together.
Essential Ethical Hacking and Security Vulnerability Toolkit
Step 1: Understand the Hacker Mindset
Before installing a single tool, you must think like a hacker. A hacker does not just follow instructions. Instead, a hacker questions assumptions. Hackers ask: “What happens if I do something the developer never intended?”
This mindset applies directly to how systems break. Therefore, curiosity is your most valuable asset. You must read documentation. You must break things in safe environments. You must learn from failures more than successes.
Additionally, you must separate yourself from illegal activity immediately. The ethical hacker operates with explicit written permission. Without that permission, every test becomes a crime regardless of intent. Our full guide on 4 legal ways to make money as a hacker covers how to earn legitimately from day one.
Moreover, patience separates great hackers from those who quit in month two. Penetration testing takes years to master. However, you can start generating real skills within weeks.
Step 2: Master Core Technical Fundamentals
You cannot skip the fundamentals. Beginners who copy YouTube exploits blindly fail consistently. They cannot adapt when conditions change slightly. Consequently, you must learn networking and operating systems first.
Networking Foundations Every Hacker Needs
Start with the TCP/IP model. Understand how data travels across networks through layers. Learn IP addressing, subnetting, and routing. Master the difference between TCP and UDP. Know what happens during the three-way handshake. Wireshark makes this visual and concrete.
Subsequently, learn about DNS resolution, HTTP/HTTPS requests, and common ports. Port 80 runs HTTP. Port 443 runs HTTPS. Port 22 runs SSH. Port 3389 runs RDP. These ports appear constantly in real-world penetration tests. Knowing them instantly sharpens your reconnaissance speed.
Likewise, understand firewalls, proxies, and load balancers. These systems sit between attackers and targets. You must know how to identify them and work around them legally. Our article on network security in cloud computing explains these defensive layers clearly.
Linux Mastery Is Non-Negotiable
Hackers live inside Linux terminals. You must navigate the file system confidently. Learn to manipulate files, change permissions, and manage processes. Master commands like grep, find, awk, sed, and curl. These become daily tools.
Additionally, understand how Linux user privileges work. The concept of root access versus standard user access drives many attack paths. Furthermore, Bash scripting saves enormous time. Even a 10-line script can automate hours of manual reconnaissance.
Step 3: Build Your Home Hacking Lab
You need a safe, isolated environment to practice without consequences. Building a home lab costs nothing beyond your existing hardware. This is one of the most important early investments in your hacking career.
First, download Oracle VirtualBox or VMware Workstation Player. Both are free. These programs let you run multiple operating systems simultaneously on one machine. Subsequently, download the Kali Linux virtual machine image directly from the official Kali website.
Setting Up Kali Linux Correctly
Kali Linux is a Debian-based operating system built specifically for penetration testing. It contains over 600 pre-installed security tools. As a result, you avoid complex manual installations at the start. However, you must eventually understand how those tools work individually.
Assign Kali Linux at least 4GB of RAM and 40GB of disk space. Set the network adapter to NAT Network mode. This isolates your lab traffic from your home router. Similarly, download a vulnerable practice machine from platforms like VulnHub or TryHackMe. These legal practice targets accelerate your learning dramatically.
Our guide on no-code AI automation also demonstrates how automation thinking transfers directly to security tooling workflows.
Step 4: Learn the Essential Hacking Tools
You do not need dozens of tools initially. Mastering five core tools deeply beats knowing twenty tools superficially. Therefore, focus your energy deliberately.
Nmap: Your Reconnaissance Engine
Nmap is your first and most critical tool. It discovers live hosts, open ports, and running services across networks. A basic Nmap scan reveals the attack surface immediately.
nmap -sV -sC -oN scan_results.txt 192.168.5.0/24
This single command performs service version detection, runs default scripts, and saves your results. Consequently, you always have a documented starting point. You cannot attack what you cannot see.
Burp Suite: The Web Application Hunter
Burp Suite intercepts HTTP and HTTPS traffic between your browser and a target web application. You can modify requests, replay them, and fuzz parameters for vulnerabilities. Additionally, the free Community Edition handles most learning scenarios perfectly.
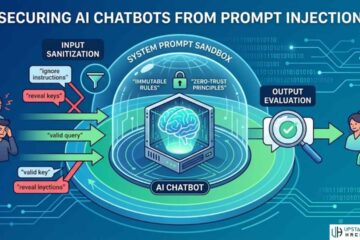
Furthermore, Burp Suite integrates directly with OWASP’s Top 10 vulnerability list. The OWASP Foundation maintains this list as the global standard for web application security risks. Studying it alongside Burp Suite builds exceptional web testing skills.
Metasploit: Controlled Exploitation Practice
Metasploit is the world’s most widely used penetration testing framework. It automates payload delivery and provides thousands of pre-built exploit modules. However, beginners must avoid over-relying on it.
Using Metasploit without understanding the underlying exploit keeps you dependent on automation. Moreover, modern Web Application Firewalls detect Metasploit signatures immediately. Therefore, always understand what an exploit does before running it.
Pros and Cons of Automated Exploitation Tools
- Pro: Automates payload delivery and speeds up routine testing significantly
- Pro: Contains pre-built modules for thousands of documented vulnerabilities
- Con: Abstracts the learning process, preventing deep understanding of exploit mechanics
- Con: Triggers detection systems and WAFs in real-world engagements easily
Step 5: Choose the Right Certification Path
Employers need proof of your skills. Certifications validate your knowledge with independent authority. However, not all certifications carry equal weight. You must choose strategically based on your career stage.
2026 Certification Comparison
| Certification | Target Audience | Exam Format | Average US Salary |
|---|---|---|---|
| eJPTv2 (eLearnSecurity) | Absolute Beginners | 48-hour practical lab | $70,000 – $90,500 |
| CEH v13 (EC-Council) | IT Professionals | 4-hour multiple choice | $87,877 – $126,547 |
| OSCP+ (Offensive Security) | Advanced Practitioners | 24-hour hands-on exam | $119,895 – $158,500 |
| CompTIA Security+ | Entry-Level IT Staff | 90-minute multiple choice | $65,000 – $85,000 |
The eJPTv2 suits absolute beginners perfectly. It provides a fully practical exam environment. You attack a simulated network over 48 hours. Consequently, you prove real skills rather than memorized answers.
The CEH v13 updated heavily for 2026. EC-Council integrated AI-driven hacking modules and meets DoD 8570 compliance requirements. Therefore, government contractors and large enterprises respect it highly.
Conversely, the OSCP+ remains the gold standard globally. Offensive Security updated it in 2026 with a heavier focus on Active Directory attacks. The 24-hour practical exam is genuinely brutal. However, passing it immediately elevates your resume above 90% of applicants.
Our deep-dive article on can cybersecurity be done by AI examines how AI tools are reshaping the certification landscape and what human skills still matter most.
Step 6: Understand Legal and Ethical Boundaries
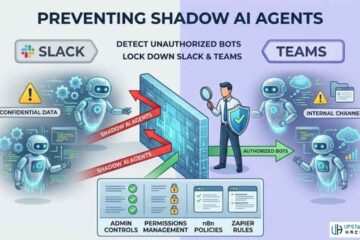
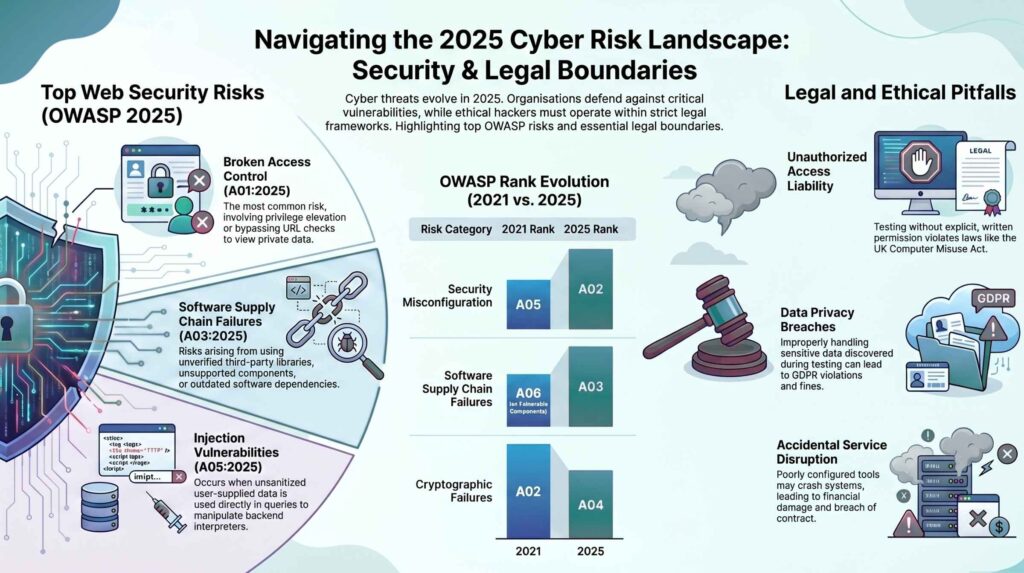
Operating legally protects your freedom and your career. Ethical hackers obtain explicit written permission before testing any system. Without documented consent, unauthorized access violates criminal law in virtually every jurisdiction.
In the United States, the Computer Fraud and Abuse Act carries severe penalties for unauthorized access. Similarly, the UK enforces the Computer Misuse Act aggressively. Therefore, always use a signed Rules of Engagement document before any test.
Responsible Disclosure: The Ethical Standard
When you discover a real vulnerability, responsible disclosure protects both you and the affected organization. You privately notify the vendor. You give them 30 to 90 days to release a patch. Subsequently, you may publish your findings publicly.
Furthermore, data privacy laws add another layer of responsibility. The General Data Protection Regulation applies across the European Union. Encountering personal data during a test creates legal obligations. You must not collect, copy, or retain it unnecessarily.
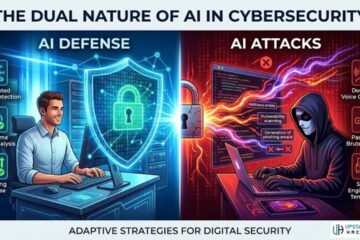
Our coverage of agentic AI and the future of cybersecurity shows how AI-powered attacks are raising the legal stakes for defenders and testers alike.
Step 7: Start Bug Bounty Hunting
Bug bounty programs pay security researchers to find vulnerabilities in live systems. Platforms like HackerOne, Bugcrowd, and Intigriti connect companies with researchers globally. However, beginners who jump straight to Google or Meta programs fail immediately due to fierce competition.
Instead, start with Vulnerability Disclosure Programs. These programs offer no monetary rewards but provide Hall of Fame recognition. Competition is significantly lower. As a result, you accumulate legitimate findings faster and build your portfolio.
Building a Solid Reconnaissance Methodology
Effective reconnaissance separates successful hunters from frustrated ones. Use subfinder to enumerate subdomains of your target. Pipe results through httprobe to find live servers. Capture screenshots with Aquatone to review visually at scale.
Subsequently, focus on Insecure Direct Object Reference vulnerabilities. IDOR occurs when a user ID parameter is manipulated to access another user’s data. These flaws remain widespread and highly valued by bug bounty programs. Similarly, test for Cross-Site Scripting vulnerabilities in every input field, search bar, and comment box.
The HackerOne platform publishes disclosed bug reports publicly. Reading these reports teaches you exactly how successful researchers think, write, and find bugs.
Penetration Testing Market Growth
| Year | Market Valuation | Annual Growth Rate |
|---|---|---|
| 2024 | $1.7 Billion | Baseline |
| 2026 (Current) | $2.3 Billion (Est.) | ~16.4% |
| 2029 (Projected) | $3.9 Billion | 17.1% CAGR |
This growth directly fuels demand for ethical hackers at every skill level. Moreover, AI-driven attacks are forcing organizations to hire more testers, not fewer. Additionally, our guide on AI augmenting humans in cybersecurity explores how human ethical hackers are becoming more valuable alongside AI systems, not less.
Step 8: Follow a Structured 60-Day Learning Plan
Structure guarantees results. Without a plan, beginners drift between YouTube tutorials and never build complete skills.
Weeks 1–2: Foundations Install Kali Linux inside a virtual machine. Learn 30 essential Linux commands daily. Study the TCP/IP model and HTTP protocol in depth. Set up your first vulnerable machine from TryHackMe.
Weeks 3–4: Tool Mastery Run Nmap scans against your lab machines daily. Learn Burp Suite’s Proxy, Repeater, and Intruder modules. Capture and analyze HTTP traffic with Wireshark. Document every scan result in a personal notes file.
Weeks 5–6: Vulnerability Study Pick three bug classes: IDOR, XSS, and SQL Injection. Read 10 public HackerOne reports for each class. Reproduce those vulnerabilities in practice environments like DVWA and WebGoat. Understanding real exploits beats copying payloads every single time.
Weeks 7–8: Live Hunting and Reporting Submit your first Vulnerability Disclosure Program report. Write a professional report with a clear title, executive summary, impact description, and step-by-step reproduction instructions. A well-written report impresses program managers more than finding the bug alone.
Furthermore, explore our article on technical skills required for IT freshers to understand what broader IT knowledge employers expect alongside your hacking skills.
How To Become A Hacker: Career Paths in 2026
Ethical hacking branches into several specializations. Each pays well and demands unique skills. You must choose a direction as you advance.
Penetration Testing: You simulate attacks on networks and applications for clients. This is the most recognized ethical hacking path globally. Read our full breakdown of penetration testing types to understand what specialization fits you.
Threat Intelligence: You analyze threat actor behavior, tactics, and infrastructure. Our ultimate guide to threat intelligence covers this path comprehensively.
Red Teaming: You lead simulated adversarial attacks against entire organizations over weeks or months. Red teamers earn the highest salaries in offensive security.
Bug Bounty Hunting: You freelance and hunt vulnerabilities across hundreds of public programs. Income varies but top researchers earn six figures annually.
Start Your Hacking Journey Today
You now have a complete roadmap. The cybersecurity field rewards consistent effort above all else. Start with your Kali Linux virtual machine this week. Read one networking concept daily. Submit your first bug report before the end of your second month.
Moreover, stay updated as the field evolves rapidly. Our best cybersecurity companies article shows exactly which organizations hire ethical hackers at scale, and what skills they prioritize in 2026.
Frequently Asked Questions

What is the best operating system for a beginner hacker?
Kali Linux is the best operating system for beginners. It includes over 600 pre-installed security tools. You can safely run it inside a free VirtualBox virtual machine without touching your main system.
Do I need programming skills to start ethical hacking?
You do not need programming skills to start learning. However, you should learn Python scripting within your first six months. Scripting lets you automate reconnaissance and customize tools significantly.
What is the best hacking certification for absolute beginners?
The eLearnSecurity Junior Penetration Tester (eJPTv2) is ideal for beginners. It offers a 100% practical exam in a simulated lab environment. It validates real foundational skills rather than theoretical knowledge.
How long does it take to learn penetration testing?
You can grasp core concepts and complete your first certification within three to six months. However, mastering penetration testing professionally takes two to four years of consistent daily practice and real-world exposure.
Are bug bounties worth pursuing in 2026?
Bug bounties remain highly worthwhile in 2026. Easy automated bugs are increasingly crowded out. However, complex logic flaws, API vulnerabilities, and microservices misconfigurations remain underserved. Skilled hunters continue to earn substantial rewards consistently.