🔄 Last Updated: April 17, 2026
Cloud computing has transformed how businesses operate, but it has also introduced new attack surfaces that traditional security models struggle to protect. Network security in cloud computing is now a critical discipline, not an optional add-on.
In my experience working with cloud architectures, most breaches don’t happen because of advanced hacking—they happen due to misconfigured networks, weak access controls, or lack of visibility.
Therefore, understanding how cloud network security works—and how to implement it properly—is essential for modern organizations.
What is Network Security in Cloud Computing? 🔐
Network security in cloud computing refers to the policies, technologies, and controls used to protect cloud-based infrastructure, data, and applications from unauthorized access, misuse, and cyber threats.
It works by segmenting networks, controlling traffic flow, encrypting data, and monitoring activity. For example, a company might use virtual firewalls and private subnets to isolate sensitive workloads from public exposure.
Simply put, it ensures that only the right users and systems can access cloud resources—and nothing else.
Why Network Security in Cloud Computing Matters ⚠️
Cloud environments are inherently dynamic, which makes them powerful—but also risky.
Unlike traditional networks, cloud systems scale automatically, expose APIs, and operate across distributed regions. This increases the potential attack surface significantly.
Moreover, shared responsibility models mean that while cloud providers secure the infrastructure, you are responsible for securing your network configurations.
One small misconfiguration can expose an entire system.
Core Components of Cloud Network Security 🧩
Understanding the building blocks helps you design a secure cloud architecture from the ground up.
Virtual Private Clouds (VPCs)
A VPC is an isolated network within a cloud provider’s environment.
It allows you to define IP ranges, subnets, and routing policies. In practice, this means you can separate public-facing services from internal systems.
Firewalls and Security Groups
Firewalls act as the first line of defense.
They filter incoming and outgoing traffic based on predefined rules. Security groups and network access control lists (ACLs) ensure that only approved traffic reaches your resources.
Identity and Access Management (IAM)
IAM controls who can access what.
In my experience, overly permissive IAM policies are one of the biggest security risks in cloud environments.
Encryption Protocols
Encryption protects data both at rest and in transit.
Even if attackers intercept data, encryption ensures they cannot read it.
Monitoring and Logging
Visibility is everything.
Tools that track network traffic and user activity help detect anomalies before they become breaches.
Common Threats in Cloud Network Security 🚨
Cloud networks face a wide range of evolving threats.
Understanding these threats allows you to proactively defend against them.
- Misconfigured cloud storage and open ports
- Distributed Denial of Service (DDoS) attacks
- Insider threats and privilege abuse
- API vulnerabilities and exploitation
- Man-in-the-middle (MITM) attacks
Each of these threats targets a specific weakness in cloud architecture, which is why layered security is essential.
Network Security Models in Cloud Computing ☁️
Different cloud models require different security approaches.
Public Cloud
Public cloud environments are shared across multiple users.
Therefore, strict access controls and encryption are necessary to prevent data leaks.
Private Cloud
Private clouds offer more control but require internal management.
Security depends heavily on how well the organization configures its infrastructure.
Hybrid Cloud
Hybrid models combine both public and private environments.
This adds complexity, making secure network integration a key challenge.
Best Practices for Network Security in Cloud Computing 🛡️
Implementing best practices ensures long-term protection and resilience.
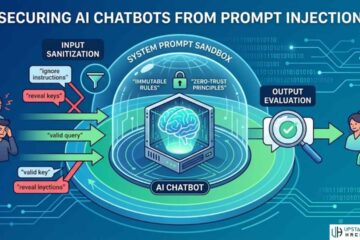
1. Use Zero Trust Architecture
Never trust any user or system by default.
Always verify identity and access permissions before granting entry.
2. Segment Your Network
Divide your cloud network into smaller segments.
This limits the spread of potential attacks and isolates sensitive workloads.
3. Enable Multi-Factor Authentication (MFA)
Passwords alone are not enough.
MFA adds an extra layer of protection, significantly reducing unauthorized access.
4. Monitor Traffic Continuously
Real-time monitoring helps detect unusual patterns.
Therefore, it enables faster response to potential threats.
5. Regularly Audit Configurations
Cloud environments change frequently.
Regular audits ensure that no misconfigurations go unnoticed.
Cloud Security Tools Comparison Table 📊
Below is a comparison of common cloud network security tools and their functions:
| Tool Type | Primary Function | Example Use Case | Security Level |
|---|---|---|---|
| Firewall | Filter network traffic | Blocking unauthorized IPs | High |
| Intrusion Detection | Monitor suspicious activity | Detecting unusual login attempts | High |
| VPN | Secure remote access | Remote employee connections | Medium |
| Encryption Tools | Protect data confidentiality | Securing sensitive customer data | High |
| SIEM Systems | Centralized monitoring and analytics | Incident response and threat detection | Very High |
This table highlights how multiple tools work together to create a comprehensive security posture.
Challenges in Cloud Network Security ⚙️
Despite advancements, several challenges persist.
First, visibility across multi-cloud environments remains limited. Organizations often struggle to track activity across different platforms.
Second, compliance requirements vary by region and industry. Meeting these standards adds complexity.
Third, automation can introduce risks if not properly configured. While automation improves efficiency, it can also scale mistakes rapidly.
Pro-Level Insight: The Hidden Risk Most Teams Ignore 💡
When I tested cloud environments for security audits, one issue kept appearing—over-trusting internal traffic.
Many organizations focus heavily on external threats but ignore internal communication between services.
However, attackers who gain access often move laterally within the network.
Therefore, securing internal traffic with micro-segmentation and encryption is just as important as protecting external endpoints.
Future Trends in Cloud Network Security 🔮
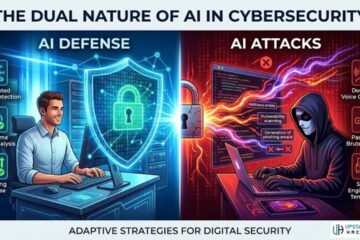
The future of cloud security is driven by automation and intelligence.
AI-powered threat detection is becoming more accurate and faster. These systems can identify patterns that humans might miss.
Moreover, Secure Access Service Edge (SASE) is redefining how organizations manage network security by combining networking and security into a unified model.
Zero Trust will also become the default standard rather than an advanced strategy.
Conclusion: Building a Secure Cloud Network Strategy
Network security in cloud computing is not about a single tool—it’s about a layered, strategic approach.
Organizations must combine technology, policies, and continuous monitoring to stay protected.
The cloud offers incredible flexibility, but without proper security, it also introduces serious risks.
Therefore, investing in strong network security practices is not optional—it’s essential for survival in the digital age.
FAQs

What are the biggest risks in cloud network security?
The biggest risks in cloud network security are misconfigurations, unauthorized access, and exposed APIs. These vulnerabilities often arise from human error rather than sophisticated attacks. Therefore, organizations must prioritize proper configuration, access control, and continuous monitoring to reduce these risks effectively.
How does Zero Trust improve cloud network security?
Zero Trust improves cloud network security by requiring strict identity verification for every user and device. It assumes no entity is trustworthy by default, even inside the network. As a result, it reduces the chances of unauthorized access and limits the impact of potential breaches.
What is the role of firewalls in cloud security?
Firewalls play a critical role by filtering incoming and outgoing traffic based on predefined rules. They act as a barrier between trusted and untrusted networks. In cloud environments, virtual firewalls help protect resources from unauthorized access and external threats.
Why is network segmentation important in the cloud?
Network segmentation is important because it isolates different parts of a cloud environment. This prevents attackers from moving freely across systems if they gain access. Therefore, it significantly reduces the impact and spread of potential security breaches.
How can businesses improve cloud network security in 2026?
Businesses can improve cloud network security by adopting Zero Trust, enabling MFA, and using advanced monitoring tools. Regular audits and automated security policies also help maintain a strong defense. Additionally, investing in AI-driven threat detection provides a proactive approach to handling modern cyber threats.
See Also: Building Blocks of Uptime: Engineering Server Reliability with Modular UPS