🔄 Last Updated: April 30, 2026
During a penetration testing engagement for a mid-sized financial firm, I uncovered the personal email addresses, home cities, LinkedIn profiles, and previously used passwords from old data breaches, along with three exposed subdomains — all before touching a single system or sending a single packet.
I used no hacking tools. Everything came from publicly available sources. That is the power of OSINT. It is the phase of every serious cyberattack and every serious security assessment that happens before the first exploit is ever attempted. Understanding OSINT in 2026 is not optional for anyone working in cybersecurity, journalism, law enforcement, or corporate risk management.
This guide covers everything — what it is, how it works, the best tools available, real techniques professionals use, and the ethical framework that separates responsible practitioners from bad actors.
What Is OSINT
OSINT stands for Open Source Intelligence. It is the process of collecting, analyzing, and applying information gathered from publicly available sources to produce actionable intelligence. The word “open source” does not refer to open-source software. It refers to information that is open to the public — available without hacking, without coercion, and without breaching any system.
OSINT sources include websites, social media platforms, news outlets, government records, academic publications, court filings, satellite imagery, DNS records, WHOIS data, job postings, dark web forums, metadata embedded in publicly shared files, and much more. The fundamental distinction is this: if a member of the public can access it legally, it qualifies as an open source.
The practice has deep roots in military and intelligence communities. The U.S. government formally recognized OSINT as a distinct intelligence discipline in the Intelligence Reform and Terrorism Prevention Act of 2004. Today, however, OSINT is practiced across the private sector, law enforcement, investigative journalism, cybersecurity, and corporate risk management with equal intensity.
The market reflects the urgency. The global Open Source Intelligence market is expected to grow from $18.07 billion in 2025 to $22.95 billion in 2026 at a compound annual growth rate of 27%, driven by social media-driven fraud and the rising cybersecurity threat landscape. Furthermore, over 68% of government security agencies now rely on OSINT platforms for digital threat mapping, and nearly 50% of cybersecurity teams use OSINT for real-time monitoring of public data.
Why OSINT Matters More Than Ever in 2026
The digital footprint of every individual, company, and government has expanded exponentially. Every employee LinkedIn profile, every press release, every domain registration, every job posting, and every GitHub commit leaks information. Attackers harvest this data systematically before launching targeted attacks. Defenders must understand exactly what attackers can see — because that intelligence shapes every security decision that follows.
Moreover, AI has turbocharged both the offensive and defensive application of OSINT. The AI security segment dominates the OSINT market with a 23% share in 2025 and is growing at a CAGR of 29.4% from 2026 to 2035, as AI and machine learning automate threat prediction, pattern identification, and anomaly detection at the velocity and scale of global information flows.
Additionally, the attack surface of organizations has expanded dramatically. Remote work, cloud infrastructure, third-party integrations, and AI-powered workflows create thousands of new data points that attackers actively harvest through OSINT before they strike. Understanding what is publicly visible about your organization is therefore the essential first step in any serious security program.
For context on how this reconnaissance phase feeds into offensive security work, our complete guide on penetration testing types explains how OSINT directly enables every subsequent phase of a professional security assessment.
The OSINT Intelligence Cycle
Professional OSINT practitioners do not simply search Google and call it intelligence. They follow a structured intelligence cycle that transforms raw public data into actionable, reliable findings.
Planning and Direction — Define the intelligence requirement. What specific question are you trying to answer? What is the scope? Who is the target? Without a clear objective, OSINT investigations produce noise rather than insight.
Collection — Gather raw data from relevant open sources. This phase uses both manual research techniques and automated tools across multiple source types simultaneously.
Processing — Clean, organize, and structure the collected data. Raw data from dozens of sources must be deduped, validated, and formatted before analysis is possible.
Analysis — Apply critical thinking to identify patterns, connections, gaps, and anomalies in the processed data. This is the highest-value phase — where raw information becomes actual intelligence.
Dissemination — Deliver findings to the relevant stakeholder in a format they can act on. A penetration testing report, a threat intelligence brief, or a corporate risk assessment all represent different forms of OSINT dissemination.
Feedback — Evaluate whether the intelligence answered the original question. Use feedback to refine collection strategy for future investigations.
This cycle distinguishes professional OSINT from casual internet searching. Every serious practitioner, whether working in a government intelligence agency, a corporate threat team, or a penetration testing firm, follows some version of this process.
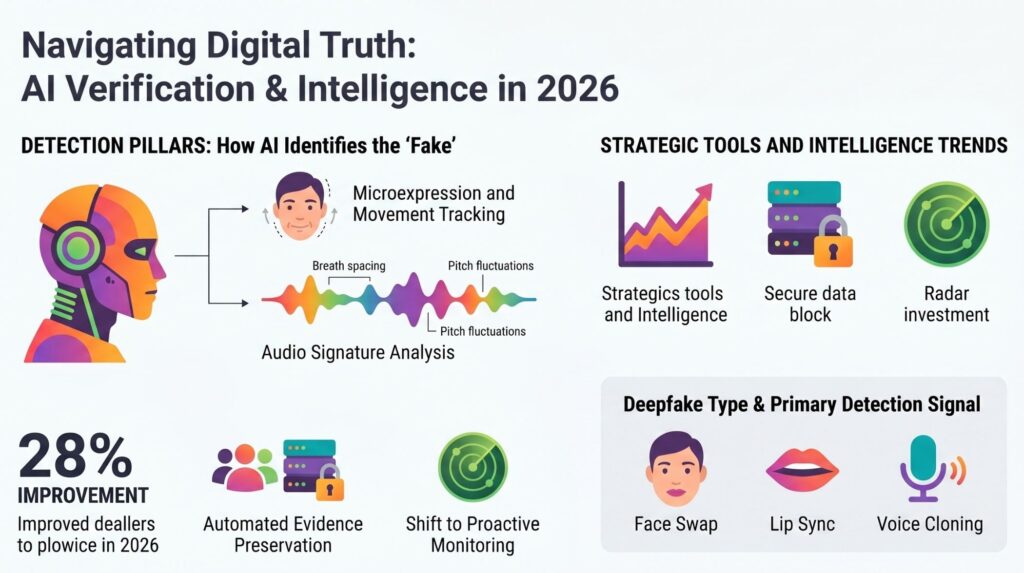
Current Methods and Future Trends in Deepfake Detection
| Focus Area | Implementation & Best Practices | Business Value & Benefits | Technical Challenges |
|---|---|---|---|
|
Workforce Remote & Hybrid Work “Never Trust, Always Verify” |
Key Steps:
| Benefits: Reduced cyber attack costs, improved productivity, and regional compliance. | Complex evaluation criteria; Device configuration drift; Legacy tool incompatibility. |
|
Cloud-Native Microservices / K8s “Assume Breach; Micro-segmentation” |
Key Steps:
| Benefits: Reduced attack surfaces, hyper-scalability, and limited breach impact. | Secrets management at scale; Ephemeral container volatility; K8s API exposure. |
|
Data & Info Information Security “Data-Centric Protection” |
Key Steps:
| Benefits: Intellectual Property protection; 33% reduction in data breach costs. | Transaction flow mapping complexity; Proprietary format reliance; Visibility into encryption. |
|
IoT Devices OT Systems / Assets “Mutual Authentication” |
Key Steps:
| Benefits: Ransomware protection for critical infrastructure; supply chain risk reduction. | Unmanaged device handling; Legacy OT integration; Vulnerability scanning difficulties. |
OSINT Techniques Used by Professionals in 2026
Techniques are the methods practitioners use during the collection phase. Each technique targets a different type of publicly available information.
Passive vs Active Reconnaissance
All OSINT techniques fall into one of two categories. Passive reconnaissance collects information without interacting with the target’s systems at all — no packets are sent, no requests touch their servers. Active reconnaissance involves direct interaction, such as performing DNS lookups, port scanning, or web crawling against the target’s infrastructure.
Most OSINT investigations begin with passive techniques and escalate to active methods only when necessary and authorized. Passive reconnaissance carries essentially no risk of detection. Active reconnaissance, conversely, may trigger intrusion detection systems and crosses into legal grey areas without explicit authorization.
Google Dorking (Advanced Search Operators)
Google dorking is the use of advanced search operators to find information that is indexed by search engines but not easily discoverable through standard searches. Operators like site:, filetype:, inurl:, and intitle: allow investigators to surface exposed configuration files, unprotected login portals, employee directories, and sensitive documents that organizations never intended to make findable.
For example, searching site:target.com filetype:pdf confidential may surface internal documents that were inadvertently indexed. Similarly, inurl:admin site:target.com may reveal administrator panels. Google dorking is entirely passive — no interaction with the target’s systems occurs.
Social Media Intelligence (SOCMINT)
Social media intelligence holds the largest share of OSINT activities, comprising around 38% of total OSINT use cases, driven by political risk and crisis monitoring needs. Practitioners analyze LinkedIn profiles for technology stack clues revealed in job postings, Twitter/X accounts for operational security failures, Facebook profiles for personal details used in social engineering, and GitHub repositories for accidentally committed credentials and internal code.
Job postings are particularly revealing. A company advertising for an “AWS Lambda and Terraform engineer with experience in Palo Alto Prisma” has just publicly disclosed key elements of its infrastructure to every attacker reading that listing.
DNS and WHOIS Reconnaissance
Domain Name System (DNS) records and WHOIS registration data reveal IP addresses, mail servers, name servers, historical registrant information, and related domain infrastructure. Tools like nslookup, dig, and online WHOIS lookup services extract this data passively. Certificate Transparency logs — which record every SSL/TLS certificate issued for a domain — are especially powerful for discovering subdomains that an organization may not have publicized.
Metadata Extraction
Files shared publicly — PDFs, Word documents, images, spreadsheets — often contain embedded metadata that reveals author names, internal network paths, software versions, GPS coordinates, and editing history. A photograph posted to a company website may contain GPS coordinates from where it was taken. A PDF of a business proposal may reveal the author’s Windows username and the internal network share path where it was stored.
ExifTool remains the most comprehensive metadata extraction tool in 2026, supporting over 100 file formats. This single technique has exposed sensitive internal information in countless organizations that had no idea their public documents were broadcasting it.
Dark Web Monitoring
The dark web hosts forums, marketplaces, and repositories where stolen credentials, leaked databases, and threat actor communications circulate. OSINT practitioners monitor these sources to identify leaked employee credentials, stolen customer data, and emerging threat actor discussions about specific targets — all before an incident is officially detected.
Platforms like Fivecast ONYX provide access to billions of data points from millions of sources, including over 200,000 unique dark websites and 300+ social media platforms for comprehensive intelligence coverage.
Geolocation Intelligence
Geolocation OSINT extracts physical location data from images, social media check-ins, IP addresses, and other digital signals. Investigators use background details in photographs — street signs, building architecture, vegetation, shadows — to pinpoint locations with remarkable precision. Conflict journalists have used this technique to verify the locations of disputed military incidents, by law enforcement to locate missing persons, and by red teams to identify the physical locations of target organizations’ key personnel.
Attack Surface Mapping
Attack surface mapping applies OSINT to identify every externally visible asset belonging to a target organization. This includes IP ranges, web applications, exposed APIs, cloud storage buckets, employee email formats, technology stacks, and third-party services. The result is a comprehensive map of potential entry points that an attacker could exploit — and that a defender must protect.
Our guide on threat intelligence covers how attack surface findings from OSINT feed directly into actionable threat intelligence programs.
Best OSINT Tools in 2026
The tool landscape has matured significantly. Professional investigators combine multiple tools rather than relying on any single platform.
Maltego — Best for Visual Link Analysis
Maltego is the gold standard for visual OSINT investigations. It maps relationships between entities — people, organizations, domains, IP addresses, social media accounts, phone numbers, and email addresses — and presents them as an interactive graph showing how everything connects. What would take hours of manual research and spreadsheet tracking, Maltego accomplishes in minutes through automated “transforms” that query dozens of external data sources simultaneously.
Maltego is widely used for cybercrime investigations and network analysis, enabling users to visualize relationships between entities like domains, IP addresses, and organizations through extensive integration with third-party APIs, making it one of the most versatile OSINT tools available. A community edition is available for free, though premium transforms require paid licensing.
Shodan — Best for Device and Infrastructure Discovery
Shodan is frequently described as “the Google for hackers.” Where traditional search engines index web pages, Shodan indexes internet-connected devices — servers, routers, webcams, industrial control systems, IoT devices, and any other system with an exposed port.
Shodan remains one of the most powerful tools for discovering internet-connected devices and vulnerabilities, especially with its 2025 update integrating AI-based threat predictions. Security teams use Shodan to discover their own exposed infrastructure before attackers do. Penetration testers use it to map a target’s internet-facing attack surface passively. A free tier is available with limited monthly searches. Paid plans begin at $69 per month.
Recon-ng — Best Modular Reconnaissance Framework
Recon-ng is a modular web reconnaissance framework built in Python, familiar to anyone who has used Metasploit. It provides a command-line environment for chaining together dozens of modules that query APIs, scrape web content, and enrich findings across multiple data sources in a single session. Results are stored in a local database, enabling repeatable searches and structured reporting.
Recon-ng offers a powerful command-line framework with full functionality and no paid tiers, making it ideal for analysts who prefer a scriptable, extensible platform for comprehensive investigations. It comes pre-installed on Kali Linux, making it immediately accessible to anyone running a standard security testing environment.
SpiderFoot — Best for Automated Multi-Source Profiling
SpiderFoot automates OSINT collection across over 200 data sources simultaneously. It pulls information on domains, IP addresses, email addresses, and usernames, then links findings to reveal relationships across all collected data. It offers both a web interface and command-line mode, supports scheduled scans, and integrates with external APIs for expanded coverage.
For reconnaissance before a penetration test, SpiderFoot is particularly valuable for the initial automated collection phase — building a comprehensive picture of the target’s digital presence before manual analysis begins.
theHarvester — Best for Email and Subdomain Reconnaissance
theHarvester is a focused, purpose-built tool for gathering email addresses, employee names, subdomains, IP addresses, and URLs from public sources including search engines, public PGP key servers, and various online services. It is lightweight, fast, and produces clean output that feeds directly into subsequent investigation phases.
For reconnaissance before a penetration test, starting with theHarvester and Recon-ng builds an initial picture of the target’s email addresses, subdomains, and exposed infrastructure before following up with Shodan or Censys to map internet-facing systems and identify potentially vulnerable services.
ExifTool — Best for Metadata Extraction
ExifTool extracts metadata from virtually any file type — images, PDFs, Word documents, spreadsheets, audio files, and video. It reads over 100 different metadata formats and presents all embedded data in structured output. ExifTool is entirely free, open source, and available on all major operating systems.
OSINT Framework — Best Directory of Resources
The OSINT Framework is not a data collection tool. It is a comprehensive, categorized directory of OSINT resources organized by investigation type. When investigators need to find the right tool for a specific question — “where do I find historical DNS records?” or “what tools exist for vehicle identification by image?” — the OSINT Framework provides a structured map of the available options.
OSINT Tools Comparison Table
| Tool | Primary Use | Cost | Skill Level | Best For |
|---|---|---|---|---|
| Maltego | Visual link analysis, entity mapping | Free (CE) / Paid | Intermediate | Cybercrime investigations, threat actor mapping |
| Shodan | Internet-connected device discovery | Free tier / $69+/mo | Beginner–Advanced | Attack surface mapping, IoT security |
| Recon-ng | Modular web reconnaissance | Free | Intermediate | Automated multi-source data gathering |
| SpiderFoot | Automated multi-source profiling | Free / Paid (HX) | Beginner–Intermediate | Penetration test recon, digital footprinting |
| theHarvester | Email and subdomain enumeration | Free | Beginner | Initial target reconnaissance |
| ExifTool | Metadata extraction | Free | Beginner | Document and image forensics |
| OSINT Framework | Tool directory | Free | Beginner | Finding the right resource for any task |
| ShadowDragon | Social media and identity correlation | Paid (enterprise) | Advanced | Law enforcement, large-scale investigations |
| IntelX | Dark web and breach data search | Free tier / Paid | Intermediate | Leaked credential monitoring |
| Censys | Internet infrastructure discovery | Free tier / Paid | Intermediate | Alternative to Shodan, certificate analysis |
Ethical Use Cases for OSINT in 2026
OSINT is a dual-use capability. The same techniques and tools that enable attackers to profile targets also enable defenders to protect organizations, journalists to expose corruption, and law enforcement to investigate crimes. The difference lies entirely in authorization, intent, and methodology.
Cybersecurity and Penetration Testing
Security teams use OSINT in the reconnaissance phase of penetration tests and red team engagements to map an organization’s attack surface from an attacker’s perspective. This is explicitly authorized work — conducted under signed agreements with full organizational consent. The goal is to identify what attackers would find before attackers find it themselves.
Red teams use OSINT to collect information about their target’s digital assets, employees, infrastructure, and possible entry points before launching simulated attacks. This reconnaissance phase often produces the most surprising findings — not because organizations lack security technology, but because they lack visibility into their own public exposure.
For teams combining OSINT with offensive security techniques, our pillar article on penetration testing types explains how OSINT integrates with black box, grey box, and social engineering test methodologies. Similarly, understanding how to become a hacker ethically covers the professional pathway that authorizes practitioners to conduct OSINT investigations legally.
Threat Intelligence and Dark Web Monitoring
Corporate security teams use OSINT to monitor for leaked employee credentials, discussions of their organization on threat actor forums, and early indicators of targeted attack planning. This proactive threat intelligence capability allows organizations to respond before an attacker exploits what they have already gathered.
Our comprehensive guide to threat intelligence covers how OSINT feeds into structured threat intelligence programs across organizations of every size.
Investigative Journalism
Journalists use OSINT to verify sources, investigate financial crimes, expose corruption, track supply chains of illicit goods, and document human rights abuses. Major investigative organizations, including Bellingcat, BBC Verify, and the New York Times visual investigations team, have pioneered advanced OSINT methodologies for conflict verification — geolocating military footage, identifying weapon systems, and tracking the movements of individuals of public interest.
These investigations operate entirely within ethical and legal boundaries because the information is publicly available and the purpose is clear public interest reporting.
Corporate Due Diligence and Competitive Intelligence
Organizations use OSINT to evaluate potential partners, suppliers, acquisition targets, and executive hires. This includes verifying business registration, screening for adverse media coverage, identifying undisclosed conflicts of interest, and analyzing competitive positioning.
This application is entirely legal when conducted on public information. It crosses ethical and legal lines when it extends to non-public information obtained through deception or unauthorized access.
Law Enforcement Investigations
Over 68% of government security agencies now rely on OSINT platforms for digital threat mapping. Law enforcement agencies globally use OSINT to investigate cybercrime, fraud, terrorism, trafficking, and missing persons. OSINT allows investigators to build comprehensive digital profiles of suspects, map criminal networks, and locate individuals using only publicly available information — without requiring warrants or legal process for the initial investigation phase.
Protecting Individuals and Families
OSINT is also used defensively by individuals. Privacy-conscious people use OSINT techniques against themselves — searching for their own information online, identifying what stalkers or bad actors could find, and taking steps to reduce their public exposure. This personal OSINT audit is increasingly recommended by privacy advocates as a standard protective practice.
Our guide on how to stop AI from reading your Gmail covers privacy hygiene practices that complement a personal OSINT audit. Additionally, our article on baiting in cybersecurity explains how OSINT findings are weaponized in social engineering attacks — critical reading for anyone wanting to protect themselves or their organization.
The Legal and Ethical Boundaries of OSINT
OSINT is legal when it collects publicly available information for legitimate purposes. However, the line between legal OSINT and illegal surveillance is real and consequential. Practitioners must understand exactly where it sits.
Legal OSINT involves gathering information from public sources without bypassing any access controls, without violating any platform’s terms of service, and without deceiving anyone to obtain information. Searching LinkedIn profiles, reading public court records, analyzing WHOIS data, and reviewing public GitHub repositories are all legal OSINT activities.
Illegal activity that masquerades as OSINT includes creating fake personas to befriend targets and extract private information, scraping platforms in ways that violate their terms of service, accessing private accounts through exploited credentials, or using OSINT findings to stalk, harass, or harm individuals.
Furthermore, data privacy regulations including GDPR in Europe and CCPA in California impose additional constraints. In 2024, 42% of potential OSINT data sources became partially or fully restricted, with privacy compliance audits spiking 125% year-over-year, and 67% of OSINT vendors reporting increased operational costs due to licensing and anonymization requirements.
Professional practitioners adhere to three ethical principles: authorization (always operate with clear legal authority), proportionality (collect only what is necessary for the defined objective), and minimization (do not retain personal data beyond what the investigation requires).
For the specific context of cybersecurity investigations and how AI tools are increasingly automating detection of malicious actors using OSINT data, our guide on automating WhatsApp scam detection demonstrates how OSINT-informed automation works in practice.
OSINT and AI: The 2026 Frontier
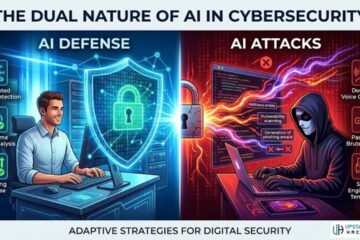
AI is transforming OSINT from a primarily manual, investigator-driven practice into a partially automated, always-on intelligence function. Modern OSINT platforms now use machine learning to correlate identities across platforms, detect emerging threats in real time, classify dark web content, and surface relevant signals from enormous volumes of public data.
Artificial intelligence enhancements have unlocked analysis of 380 million data points per hour, compared to 95 million in 2020, with deep-learning modules now deployed in 64% of OSINT offerings, detecting anomalies in text streams at 42,000 entries per second.
However, AI-powered OSINT also introduces risks. Deepfakes, AI-generated misinformation, and synthetic personas make source verification more difficult than ever. Nearly 35% of OSINT analysts cite source validation as their top concern when leveraging open data streams, as distinguishing authentic public information from deliberately planted disinformation becomes an increasingly sophisticated analytical challenge.
Our guide on detecting deepfake audio in real time covers AI-based verification techniques directly relevant to the source validation challenge in modern OSINT investigations. Additionally, for professionals wanting to understand how AI is reshaping the broader threat landscape that OSINT investigates, our article on AI augmenting humans in cybersecurity provides essential strategic context.
OSINT in Penetration Testing: A Practical Workflow
Professional penetration testers follow a structured OSINT workflow during the reconnaissance phase of every engagement. Here is how a real-world OSINT reconnaissance workflow looks in practice.
Phase 1 — Passive Footprinting (Days 1–2): Use theHarvester to enumerate email addresses, employee names, and subdomains. Query Certificate Transparency logs to discover all certificates issued for target domains. Review WHOIS records and DNS data. Analyze LinkedIn for technology stack clues in job postings. Check GitHub for accidentally committed credentials or internal code.
Phase 2 — Infrastructure Mapping (Days 2–3): Use Shodan or Censys to identify internet-facing systems, exposed ports, and vulnerable services. Use SpiderFoot to automate collection across all available sources simultaneously. Review cloud storage buckets for public accessibility.
Phase 3 — Metadata and Document Analysis (Day 3): Download publicly available documents from the target’s website. Run ExifTool across all collected files to extract author names, internal network paths, software versions, and GPS coordinates.
Phase 4 — Social and Dark Web Analysis (Days 3–4): Search breach databases for leaked employee credentials. Monitor relevant dark web forums for any discussions of the target. Check paste sites for recently leaked sensitive data.
Phase 5 — Analysis and Reporting (Day 4–5): Use Maltego to visualize all discovered relationships. Identify the highest-risk findings — leaked credentials, exposed services, social engineering vectors — and document them with clear evidence and remediation recommendations.
This workflow represents ethical, authorized OSINT practice. Every step uses publicly available information, and the entire engagement operates under a signed authorization agreement.
Frequently Asked Questions

What is OSINT in simple terms?
OSINT stands for Open Source Intelligence. It is the practice of collecting and analyzing information from publicly available sources — websites, social media, government records, databases, and more — to produce actionable intelligence. The key distinction is that all information gathered through OSINT is legally accessible to the public. No hacking, no unauthorized access, and no deception are required.
Is OSINT legal?
Yes, OSINT is legal when it gathers information from genuinely public sources for legitimate purposes. The legality depends on what is collected, how it is collected, and what it is used for. Gathering public social media posts, WHOIS records, or government filings is legal. Creating fake personas to extract private information, bypassing access controls, or using OSINT findings to stalk or harass individuals is not. Additionally, GDPR, CCPA, and other privacy regulations impose compliance requirements on how personal data gathered through OSINT may be stored and used.
What is the best free OSINT tool for beginners?
For beginners, theHarvester and SpiderFoot are the most accessible starting points. theHarvester has a simple command-line interface that teaches basic reconnaissance concepts clearly. SpiderFoot offers a web interface with automated multi-source collection that makes it easier to get meaningful results without deep technical expertise. Both are entirely free and widely documented. The OSINT Framework directory is also invaluable for beginners learning what tools exist for different investigation types.
How do cybersecurity professionals use OSINT?
Cybersecurity professionals use OSINT across multiple disciplines. Penetration testers use it in the reconnaissance phase to map an organization’s attack surface before conducting authorized offensive testing. Threat intelligence analysts use it to monitor for leaked credentials, track threat actors, and detect early warning signs of targeted attacks. Incident responders use it to research attacker infrastructure during active incidents. Security engineers use it to audit their own organization’s public exposure and reduce unnecessary risk.
How is AI changing OSINT in 2026?
AI is dramatically accelerating OSINT in two directions. On the analysis side, machine learning models now correlate identities across platforms, detect anomalies in massive data streams, and surface relevant signals from volumes of public data that would be impossible for human analysts to process manually. On the threat side, AI-generated deepfakes, synthetic personas, and disinformation campaigns make source validation more challenging. The result is that modern OSINT practice increasingly requires both AI-powered tooling and strong human judgment to distinguish authentic intelligence from deliberately planted noise.