🔄 Last Updated: April 30, 2026
Vishing in cybersecurity is one of the fastest-growing threats your organization faces right now — and most employees would not recognize it if it happened to them today.
Voice phishing, commonly called vishing, is a social engineering attack delivered entirely over the phone. An attacker calls you, impersonates a trusted authority — your bank, your IT department, the IRS, even your CEO — and manipulates you into handing over passwords, account credentials, or money. No malware required. No suspicious link to click. Just a convincing voice and a well-rehearsed script.
In 2024 alone, vishing attacks surged by 442% between the first and second half of the year, according to CrowdStrike’s Global Threat Report. By 2025, the volume had already exceeded the entire previous year’s total. Meanwhile, 70% of organizations globally have been targeted by at least one voice phishing attack, and the average recovery cost per major incident sits at $1.5 million.
I have spent time reviewing incident response data and enterprise security reports specifically for this guide. The pattern is clear: vishing is no longer a consumer scam. It is a primary initial access vector used by ransomware groups, nation-state actors, and professional fraud operators alike. Understanding it is now a baseline requirement for anyone serious about security.
What Is Vishing? A Clear Definition
Vishing is short for voice phishing. It combines the mechanics of traditional phishing attacks — deception, impersonation, urgency — with the directness and psychological weight of a live phone call.
The name follows the pattern established by the broader threat category. Phishing uses email. Smishing uses SMS text messages. Vishing uses voice — via regular phone calls, VoIP systems, or increasingly, AI-generated audio that mimics real people’s voices.
What makes vishing particularly dangerous is the trust people instinctively place in human voices. A well-crafted email raises flags. A confident, authoritative voice on the phone triggers compliance instincts that written words simply do not. Attackers exploit this psychological gap deliberately and systematically.
Furthermore, caller ID spoofing means the call can appear to originate from a legitimate number — your bank’s official line, your company’s IT helpdesk extension, or even a colleague’s personal number. That visual confirmation of legitimacy is precisely what breaks down a target’s defenses before the conversation even begins.
How Vishing Attacks Work: The Step-by-Step Playbook
Understanding the mechanics of a vishing attack is the first step toward defeating one. Most vishing campaigns follow a predictable, repeatable structure regardless of who is behind them.
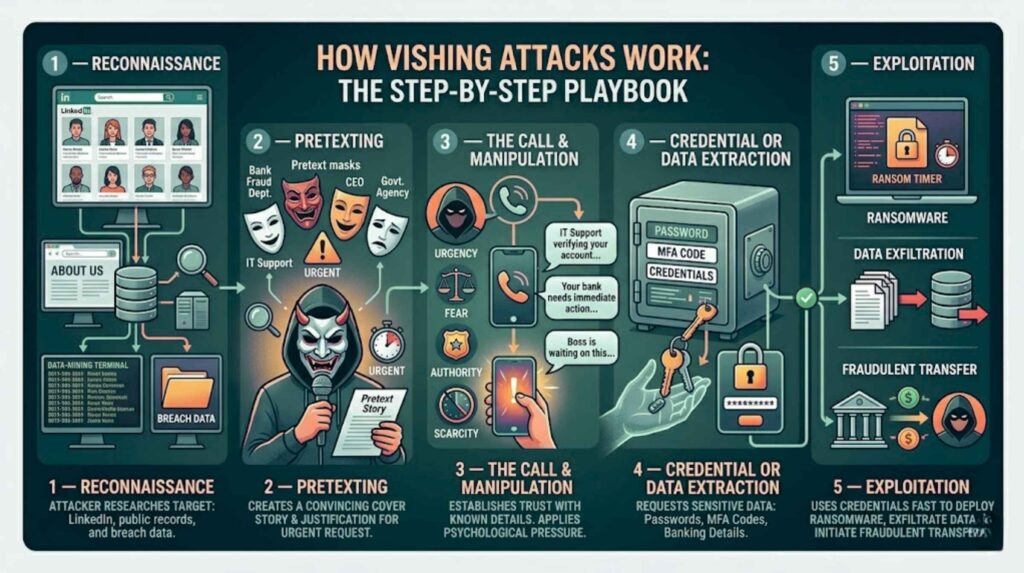
Step 1 — Reconnaissance
Before making a single call, attackers research their target thoroughly. They use LinkedIn to understand job titles and reporting structures. They mine public company websites, press releases, and social media. They purchase data from breached databases to find employee names, phone numbers, and email addresses. This reconnaissance phase transforms a cold call into a hyper-personalized attack.
Step 2 — Pretexting
The attacker constructs a convincing cover story, called a pretext. Common pretexts include an IT security team performing an urgent account verification, a bank’s fraud department flagging suspicious activity, a government agency conducting a compliance audit, or a vendor requiring immediate payment confirmation. The pretext is designed to justify why the caller needs sensitive information — and why the request is urgent.
Step 3 — The Call and Manipulation
The attacker makes contact. They confirm details the target already knows — partial account numbers, recent transactions, the name of a real manager — to establish credibility. Then they apply psychological pressure: urgency, authority, fear, or scarcity. They may tell you your account will be frozen in 24 hours, that your boss is waiting on this, or that failure to comply carries legal consequences.
Step 4 — Credential or Data Extraction
Once trust is established and pressure is applied, the attacker asks for what they came for. This may be a password, a one-time MFA code, banking credentials, remote access to a device, or authorization for a wire transfer. In enterprise attacks, help desk impersonation is especially common — attackers call IT support and social-engineer password resets for targeted employee accounts.
Step 5 — Exploitation
With credentials in hand, attackers move fast. They log in, escalate privileges, deploy ransomware, exfiltrate data, or initiate fraudulent financial transfers — often within minutes of the call ending.
Vishing vs. Phishing vs. Smishing: Key Differences
Understanding how vishing relates to other attack types clarifies where your defenses need to focus.
| Attack Type | Channel | Primary Tactic | Detection Method |
|---|---|---|---|
| Phishing | Malicious links, fake attachments | Email gateway, link scanning | |
| Smishing | SMS/Text | Fake links, fake delivery alerts | Mobile threat detection |
| Vishing | Voice call | Impersonation, social pressure | Security awareness training |
| Quishing | QR Code | Fake login pages via QR | URL inspection tools |
| TOAD | Email + Phone | PDF lure → fake support call | Multi-channel monitoring |
Vishing is uniquely resistant to technical filtering. Unlike phishing emails or smishing texts, a phone call cannot be scanned by a security gateway. It bypasses every layer of your email and network security stack entirely. Consequently, human awareness is the only reliable first line of defense against voice phishing.
Telephone-Oriented Attack Delivery (TOAD) represents a particularly dangerous hybrid. Attackers send a convincing PDF via email, then prompt the recipient to call a fake support number embedded in the document. The call completes the deception that the email began. Multi-channel attacks like TOAD are increasing rapidly — smishing and vishing combined now account for 19% of all data breaches, according to the Verizon DBIR 2025.
The AI Deepfake Vishing Threat in 2026
The vishing threat has fundamentally shifted with the rise of AI voice cloning. This is not a future risk. It is happening right now, at scale.
AI voice cloning technology can replicate a person’s voice from as few as three seconds of audio. Recordings from earnings calls, YouTube videos, podcasts, or even voicemail greetings provide enough source material. The resulting synthetic voice is virtually indistinguishable from the real person — 25% of people are deceived even when they know a deepfake might be present.
The most cited real-world case involved a finance employee at a Hong Kong-based multinational who was deceived into transferring $25 million after a video call with what appeared to be the company’s CFO and other executives. Every person on the call was a deepfake. The employee transferred funds because the faces and voices matched the people they knew.
In May 2025, the FBI issued a formal public service announcement warning that malicious actors were using AI-generated voice messages to impersonate senior U.S. government officials, targeting current and former federal officials for credential harvesting. The ShinyHunters and Scattered Spider campaigns of 2025-2026 used professional vishing kits to compromise over 760 organizations — including confirmed breaches at major enterprises — with operators paid $500-$1,000 per call using pre-written helpdesk targeting scripts.
Deepfake fraud losses are projected to reach $40 billion globally by 2027, according to Deloitte estimates. Furthermore, the number of AI-driven scam calls reaching Americans reached 3.1 billion per month in 2025 — up from 2.7 billion the year prior.
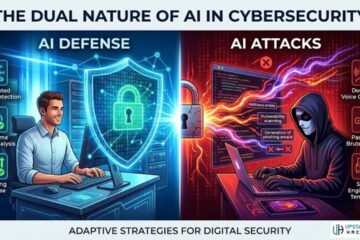
This is precisely why AI in cybersecurity defense must now evolve to detect AI-generated threats, not just human-crafted ones. The arms race is fully underway.
Real Vishing Attack Examples
Understanding real vishing scenarios makes the threat tangible and training more effective.
The IT Help Desk Scam is the most common enterprise vishing vector in 2026. An attacker calls posing as an IT support technician and claims they detected unusual activity on the target’s account. They ask the employee to confirm their username, then provide a one-time verification code that the attacker uses simultaneously to log in. Cisco Talos reports that vishing of IT administrators is now three times more common than user-based registration fraud.
The Bank Fraud Call targets consumers and businesses alike. The caller ID displays the bank’s real phone number (via spoofing). The “fraud agent” warns that a large unauthorized transaction is in progress. They ask the victim to verify recent activity and provide credentials to “freeze” the account immediately. By the time the call ends, the attacker has everything they need.
The Executive Impersonation (or CEO vishing) targets finance and accounting employees. An attacker, often using a cloned voice of a real executive, calls and requests an urgent wire transfer to a new vendor account. The voice sounds authentic. The urgency feels real. The transfer goes through before anyone verifies the request through official channels.
The Government Impersonation exploits fear of legal authority. Callers claim to be from the IRS, Social Security Administration, immigration enforcement, or law enforcement. They threaten arrest, fines, or account suspension unless immediate payment or information is provided. Americans aged 60 and older reported $4.8 billion in internet crime losses in 2024, with voice phishing disproportionately affecting this demographic.
How to Protect Yourself From Vishing Attacks
Protection requires a layered approach combining technical controls, policy, and human training. Neither technical tools nor awareness alone is sufficient in 2026.
For Individuals
The most powerful defense for individuals is a simple rule: never act on an unsolicited call that creates urgency around money, credentials, or personal data. Hang up. Call back on the official number you find independently — not the one provided by the caller.
Additionally, enable multi-factor authentication on all financial and personal accounts. Even if an attacker obtains your password, MFA creates an additional barrier. However, be aware that attackers increasingly call and ask for MFA codes directly — never read an authentication code to anyone who calls you. No legitimate organization needs your MFA code over the phone.
Register with the FTC’s Do Not Call registry and use a call-blocking app. While these steps do not stop determined targeted attacks, they significantly reduce exposure to opportunistic robocall campaigns.
For Businesses and IT Teams
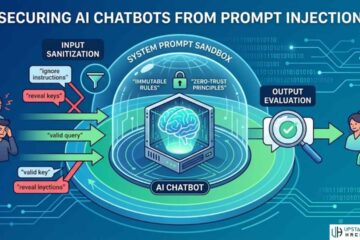
Implement a strict call-back verification policy for any request involving password resets, wire transfers, or privilege escalation. This single control stops the majority of enterprise vishing attacks. The policy must require verification through a pre-established channel — not the phone number provided during the suspicious call.
Train your IT help desk specifically. Cisco Talos data confirms that help desks are the primary target of enterprise vishing in 2026. Help desk staff need explicit scripts for handling requests for account resets from unverified callers, including mandatory identity verification steps before any action is taken.
Security awareness training that includes live vishing simulation exercises reduces susceptibility dramatically. KnowBe4’s benchmarking data shows that phishing susceptibility drops from 33.1% to 4.1% after 12 months of consistent training — an 86% reduction. Similarly structured vishing simulation programs deliver comparable results.
Moreover, implement FIDO2 hardware security keys as your MFA standard for privileged accounts. Hardware keys cannot be socially engineered over the phone — they require physical presence. This eliminates the most common MFA bypass technique used in vishing attacks.
Finally, enforce a call verification code system for internal communications — a simple pre-agreed word or phrase that employees use to confirm the identity of callers requesting sensitive actions. This low-tech control is remarkably effective against voice cloning attacks because the attacker cannot know the current verification word in advance.
Technical Controls Worth Deploying
Deploy a VoIP monitoring solution that logs call metadata and flags unusual patterns — high-volume calls to HR or IT from unknown external numbers, for instance. Integrate these logs with your SIEM for cross-correlation with authentication events. An attacker calling the help desk followed immediately by a password reset request for the same user is a detectable signal.
Additionally, use endpoint detection tools to catch the downstream activity that follows successful vishing attacks: unauthorized remote access tool installation, credential dumping, or lateral movement. Even if the initial call succeeds, strong endpoint monitoring gives your team an opportunity to detect and contain the breach before significant damage occurs.
Consider implementing threat intelligence feeds that include known vishing campaign indicators — spoofed number ranges, emerging attacker scripts, and sector-specific targeting patterns. Several threat intelligence providers now offer real-time vishing campaign tracking as part of their enterprise feeds.
For small businesses, AI-powered cybersecurity tools designed for limited budgets can provide call monitoring and anomaly detection capabilities that previously required enterprise-grade infrastructure. The barrier to entry has dropped significantly in 2026.
Regulatory and Compliance Implications
Vishing is increasingly a compliance concern, not just a security one. In February 2026, New York’s Department of Financial Services issued the first state-level vishing-specific advisory, requiring financial institutions to implement vishing controls and reporting procedures. More regulators are expected to follow.
Under frameworks including SOC 2, HIPAA, and PCI-DSS, organizations are required to demonstrate that they maintain controls against social engineering attacks. A successful vishing attack that results in unauthorized data access may trigger breach notification requirements, regulatory penalties, and civil liability — in addition to direct financial losses. Building a documented disaster recovery plan that explicitly addresses voice phishing scenarios is now a regulatory expectation for financial services and healthcare organizations.
For organizations subject to federal compliance frameworks, the CISA Social Engineering guidance provides authoritative recommended controls specifically covering phone-based social engineering, including vishing.
Additionally, the FBI’s official vishing resource page provides current reporting mechanisms and guidance for individuals and organizations that have been targeted. Reporting vishing attempts to the FBI’s IC3 contributes to threat intelligence that benefits the broader security community.
Vishing and the Broader Social Engineering Threat Landscape
Vishing does not operate in isolation. It is one element of an expanding social engineering attack surface that now includes baiting, pretexting, quid pro quo attacks, and increasingly sophisticated multi-channel campaigns.
Understanding how phishing emails are crafted helps you recognize the same psychological manipulation techniques when they appear over the phone. The urgency, the authority, the fear trigger — these are identical across every social engineering vector. Training your pattern recognition on one vector makes you more resilient against all of them.
Similarly, understanding what pharming is in cybersecurity — where attackers redirect legitimate web traffic to malicious sites — reveals how attackers combine technical exploits with social engineering to create layered traps. A vishing attack that succeeds in obtaining partial credentials may be followed immediately by a pharming redirect that captures the remainder.
If your organization is building a comprehensive security program, penetration testing that includes social engineering scenarios is the most reliable way to measure your actual susceptibility to vishing and other voice-based attacks — before a real attacker does.
Frequently Asked Questions

What is vishing in cybersecurity in simple terms?
Vishing is a phone-based scam where attackers impersonate a trusted person or organization — your bank, IT department, or government agency — and manipulate you into sharing passwords, MFA codes, or personal data over the phone. The name combines “voice” and “phishing.” Unlike email phishing, vishing uses a live or AI-generated voice call to create urgency and bypass your natural skepticism. It is one of the fastest-growing cybersecurity threats in 2026, with attacks surging 442% between the first and second half of 2024 alone.
How is vishing different from phishing and smishing?
Phishing attacks arrive via email with malicious links or attachments. Smishing uses SMS text messages. Vishing uses voice calls — either from a live human attacker or, increasingly, from AI-generated synthetic voices that convincingly mimic real people. The key difference is the attack channel and the psychological leverage it provides. A phone call creates real-time pressure that email cannot replicate, making vishing highly effective even against people who are otherwise aware of digital scams.
Can AI voice cloning make vishing impossible to detect?
Modern AI voice cloning can replicate a person’s voice from as little as three seconds of audio, and 25% of people are fooled even knowing the call may be a deepfake. However, detection is still possible. Organizations can implement pre-agreed voice verification codes, call-back policies on verified numbers, and behavioral anomaly detection in their VoIP systems. The most effective defense is never acting on an unsolicited call that requests credentials or financial action — regardless of how authentic the voice sounds. When in doubt, hang up and call back on the official number.
What should I do if I receive a vishing call?
First, do not provide any information. Tell the caller you need to verify their identity and will call back on the official number. Hang up. Look up the organization’s official contact number independently — never use a number provided during the call. If the call appeared to come from your bank or employer, contact them directly to report the attempt. Additionally, report vishing attempts to the FBI’s Internet Crime Complaint Center (IC3) at ic3.gov, and to the FTC at reportfraud.ftc.gov. If you did share sensitive information, change your passwords immediately and contact your bank or IT team.
Are businesses or individuals more at risk from vishing?
Both face significant risk, but the attack profiles differ. Individuals are typically targeted by opportunistic campaigns impersonating banks, government agencies, or tech support. Businesses face more targeted, researched attacks — particularly IT help desks and finance teams — with attackers seeking credential access or wire transfer authorization. In 2026, enterprise vishing has become a primary initial access vector for ransomware groups. Financial services organizations face the highest targeting rate, with 44.1% of vishing calls directed at that sector in recent datasets. Both individuals and organizations benefit from the same core defense: a firm policy of never complying with unsolicited calls that request sensitive data or immediate action.