🔄 Last Updated: April 30, 2026
I have reviewed dozens of corporate network breaches over the past several years. In almost every case, the attacker did not break through a wall. They walked through an unlocked door — usually a stolen credential, a legacy account, or an overpermissioned insider. Traditional perimeter security assumes that everything inside the network is safe. That assumption is now dangerously outdated. Zero trust security exists to fix that exact problem. This guide breaks down everything you need to know about zero trust in 2026: what it is, how it works, the seven NIST pillars, how to implement it, and which tools actually deliver results.
What Is Zero Trust Security
Zero trust security is a cybersecurity framework built on one foundational principle: never trust, always verify. No user, device, or application receives automatic trust — regardless of whether they are inside or outside the corporate network. Every access request is authenticated, authorized, and continuously validated before and during each session.
The term was coined by Forrester Research analyst John Kindervag in 2010. However, it has moved from theory to regulatory mandate in 2026. The U.S. National Security Agency published an updated Zero Trust Implementation Guideline Primer in January 2026, reinforcing that zero trust represents a fundamental enhancement in cybersecurity — requiring continuous authentication and authorization of every user, device, and application under the principles of “never trust, always verify” and “assume breach.”
The market numbers reflect the urgency. The zero trust security market is expected to grow from USD 41.72 billion in 2025 to USD 48.43 billion in 2026, and is forecast to reach USD 102.01 billion by 2031, at a 16.07% CAGR over 2026–2031. Furthermore, organizations that adopted zero trust architectures saw an 83% reduction in incident-response times and an 80% drop in successful breaches.
Zero trust is not a single product you purchase. It is a strategic architecture you build — one that replaces implicit trust with continuous verification across every access point.
Why Perimeter-Based Security No Longer Works
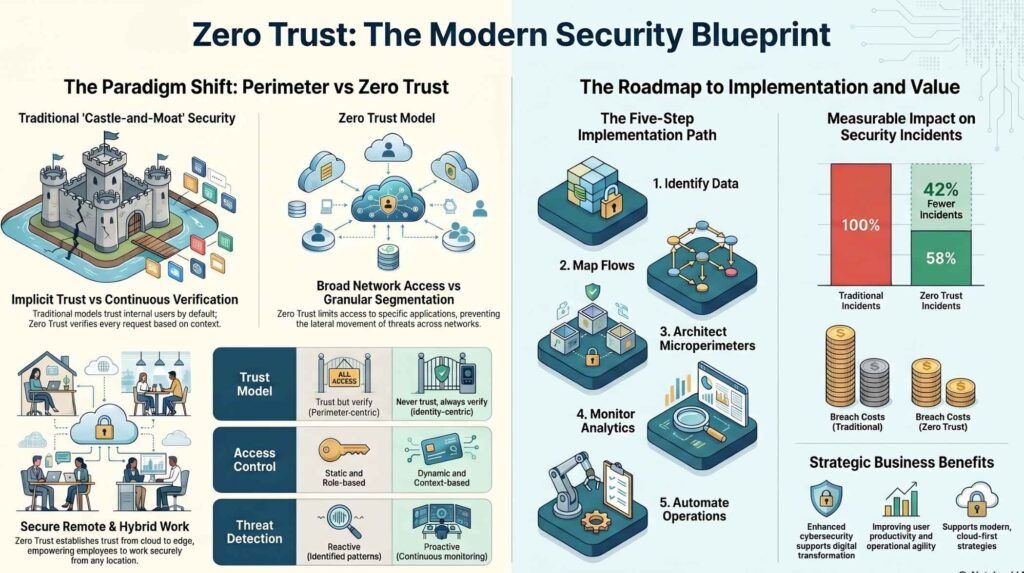
For decades, organizations operated on a castle-and-moat model. Build a strong perimeter, trust everything inside, and block everything outside. That model was designed for an era when employees worked in offices, data lived on-premises, and the network boundary was clearly defined.
That era is over. Today, employees work from homes, coffee shops, and airports. Applications live in AWS, Azure, and dozens of SaaS platforms. Partners and contractors access internal systems daily. Supply chains are deeply integrated digitally. Additionally, AI-powered attack tools now move at speeds that make perimeter-based defenses largely reactive.
The consequences are severe. Zero-day vulnerabilities tripled in 2024, and ransomware represented one-third of all breaches across 92% of industries. Human factors contributed to 68% of incidents, pressing enterprises to adopt continuous verification that assumes internal compromise. Moreover, third-party weaknesses climbed 68%, forcing organizations to extend zero trust principles to suppliers, and insider threats cost financial institutions USD 16.2 million per event on average.
In short, perimeter-based security fails because the perimeter no longer exists. Zero trust replaces the perimeter with identity, context, and continuous validation.
For a broader view of how these threats are evolving, our complete guide on threat intelligence explains how threat data should directly shape your security architecture decisions.
Zero Trust Security Implementation and Operational Strategies
| Focus Area | Implementation & Best Practices | Business Value & Benefits | Technical Challenges |
|---|---|---|---|
|
Workforce Remote & Hybrid Work “Never Trust, Always Verify” |
Key Steps:
| Benefits: Reduced cyber attack costs, improved productivity, and regional compliance. | Complex evaluation criteria; Device configuration drift; Legacy tool incompatibility. |
|
Cloud-Native Microservices / K8s “Assume Breach; Micro-segmentation” |
Key Steps:
| Benefits: Reduced attack surfaces, hyper-scalability, and limited breach impact. | Secrets management at scale; Ephemeral container volatility; K8s API exposure. |
|
Data & Info Information Security “Data-Centric Protection” |
Key Steps:
| Benefits: Intellectual Property protection; 33% reduction in data breach costs. | Transaction flow mapping complexity; Proprietary format reliance; Visibility into encryption. |
|
IoT Devices OT Systems / Assets “Mutual Authentication” |
Key Steps:
| Benefits: Ransomware protection for critical infrastructure; supply chain risk reduction. | Unmanaged device handling; Legacy OT integration; Vulnerability scanning difficulties. |
The 3 Core Principles of Zero Trust Security
Every zero trust architecture, regardless of vendor or toolset, rests on three foundational principles.
1. Verify Explicitly
Every access request must be authenticated and authorized using all available data points — including user identity, device health, location, service or workload, data classification, and behavioral anomalies. Implicit trust based on network location is eliminated entirely.
2. Use Least Privilege Access
Users and systems receive only the minimum level of access required to perform their function — nothing more. This is enforced through just-in-time and just-enough-access (JIT/JEA) policies, risk-based adaptive policies, and data protection controls that limit lateral movement if a credential is compromised.
3. Assume Breach
Design as if an attacker is already inside. Segment access, encrypt communications end-to-end, use analytics to detect unusual behavior, and automate response. This principle pushes organizations to minimize blast radius — the damage any single compromised account or device can cause.
These three principles align directly with NIST SP 800-207, the definitive U.S. government standard for zero trust architecture. Our article on network security in cloud computing explores how these principles translate specifically to cloud environments.
The 7 Pillars of Zero Trust Security (NIST Framework)
The seven pillars of zero trust as defined by NIST and CISA are: Identity, Devices, Networks, Applications and Workloads, Data, Infrastructure, and Visibility and Analytics. Each pillar addresses a distinct dimension of your security posture. Weakness in any single pillar can undermine the entire architecture.
Pillar 1: Identity
Identity is the new perimeter. Every access decision starts here. With 97% of identity-based attacks leveraging passwords, identity is the most targeted attack surface. Stolen credentials are the primary entry point for ransomware, data exfiltration, and lateral movement.
Identity controls include multi-factor authentication (MFA), single sign-on (SSO), privileged access management (PAM), and continuous user behavior analytics. In 2026, phishing-resistant FIDO2/WebAuthn credentials are the recommended MFA standard from CISA for critical infrastructure operators.
Pillar 2: Devices
Every device requesting access — laptop, mobile phone, IoT sensor, or server — must be validated before it can connect. Device trust is established through endpoint detection and response (EDR) tools, mobile device management (MDM) platforms, and compliance checks that assess patch levels, encryption status, and configuration.
A compromised device is as dangerous as a compromised credential. Therefore, zero trust treats device health as a dynamic signal, not a one-time registration.
Pillar 3: Networks
Traditional flat networks allow attackers who gain initial access to move freely across systems — a technique called lateral movement. Micro-segmentation counters this by dividing the network into isolated zones. Even if an attacker compromises one segment, they cannot move to others without re-authentication and re-authorization.
Zero Trust Network Access (ZTNA) replaces traditional VPNs by granting application-specific access rather than broad network access. 96% of organizations prefer the zero trust approach over traditional VPN, and 65% plan to replace VPN within one year.
Pillar 4: Applications and Workloads
Applications must be secured with per-application access controls, regardless of where they are hosted. This pillar covers SaaS applications, cloud-native workloads, on-premises applications, and APIs. Shadow IT — unauthorized applications used without IT oversight — is discovered and governed under this pillar.
Pillar 5: Data
Data is the ultimate target in every cyberattack. This pillar covers data classification, labeling, encryption at rest and in transit, and data loss prevention (DLP) controls. Consequently, access to sensitive data is tied to verified identity and device context rather than network location.
Pillar 6: Infrastructure
This pillar governs cloud environments, on-premises servers, containers, Kubernetes clusters, and virtual machines. Infrastructure security includes continuous vulnerability scanning, configuration management, and runtime threat detection. In February 2026, major U.S. enterprises accelerated zero trust adoption for AI-driven workloads, integrating stricter authentication, micro-segmentation, and real-time monitoring of access behavior into AI and machine learning platforms.
Pillar 7: Visibility and Analytics
Zero trust without visibility is guesswork. This pillar requires continuous monitoring of all access attempts, behavioral analytics to detect anomalies, and security information and event management (SIEM) integration. AI-powered tools now analyze access patterns in real time, flagging deviations before they become incidents.
Zero Trust Maturity Model: Where Does Your Organization Stand
CISA’s Zero Trust Maturity Model defines five pillars — Identity, Devices, Networks, Applications and Workloads, and Data — each with four maturity stages: Traditional, Initial, Advanced, and Optimal. Most organizations in 2026 fall somewhere between Traditional and Initial. Reaching Advanced across all pillars is a realistic two-to-three year goal for committed organizations.
| Maturity Stage | Characteristics | Typical Organization |
|---|---|---|
| Traditional | Perimeter-based, implicit trust, no MFA | Small businesses, legacy enterprises |
| Initial | MFA deployed, some segmentation, basic monitoring | Mid-market companies starting their journey |
| Advanced | Automated policies, behavioral analytics, ZTNA deployed | Mature enterprises, regulated industries |
| Optimal | AI-driven continuous verification, full automation, zero standing privileges | Leading financial institutions, federal agencies |
| Target for 2026 | Advanced across all five pillars (CISA recommendation) | Critical infrastructure operators |
Understanding your current maturity level is the essential first step. You cannot implement zero trust effectively without knowing your starting point.
How to Implement Zero Trust Security: A 7-Step Roadmap
81% of organizations plan to implement zero trust by the end of 2026, yet most projects fail on the same thing — a lack of a clear roadmap. Here is a proven seven-step implementation approach aligned with NIST SP 800-207.
Step 1: Map your protect surface. Identify your most critical data, applications, assets, and services — your crown jewels. Customer data, intellectual property, financial systems, and authentication infrastructure come first.
Step 2: Map your transaction flows. Document how traffic moves across your environment. You cannot segment what you do not understand. This step reveals undocumented data flows, shadow applications, and legacy system dependencies.
Step 3: Build a zero trust architecture around your protect surface. Deploy micro-segmentation starting with your highest-risk segments. Place policy enforcement points between users and your critical resources.
Step 4: Create zero trust policies. Define who, what, when, where, and how access is granted for each resource. Policies must encode least privilege — the minimum access required for each role, at each time, from each approved device.
Step 5: Deploy identity and access management tools. Implement MFA across all users. Deploy SSO to reduce password sprawl. Establish PAM for privileged accounts, which are the most dangerous if compromised.
Step 6: Integrate continuous monitoring and analytics. Centralize security telemetry from all pillars into a SIEM. Deploy user and entity behavior analytics (UEBA) to detect anomalous access patterns. Automate threat response with SOAR playbooks for common policy violations.
Step 7: Measure, iterate, and expand. Track MFA adoption rate (target: 100%), mean time to revoke access (target: under 15 minutes for automated response), and the percentage of applications behind ZTNA versus VPN.
For teams wanting to understand how automated tools accelerate implementation, our guide on low-cost AI agents for small business workflows covers automation options that fit smaller security budgets.
Zero Trust vs Traditional Security: Key Differences
| Factor | Traditional Perimeter Security | Zero Trust Security |
|---|---|---|
| Trust model | Implicit trust inside the network | No implicit trust anywhere |
| Access control | Network-based (VPN, firewall rules) | Identity and context-based (per session) |
| Lateral movement | Largely unrestricted once inside | Blocked by micro-segmentation |
| Remote access | VPN with broad network access | ZTNA with application-specific access |
| Insider threats | Difficult to detect and contain | Continuously monitored, quickly isolated |
| Cloud/SaaS apps | Bolted-on security controls | Native integration with cloud identity |
| Breach cost impact | Average USD 5.10 million per incident | Average USD 4.15 million per incident |
| Implementation | Once-and-done perimeter build | Continuous, iterative architecture |
Organizations with zero trust in place experience breach costs averaging $4.15 million compared to $5.10 million without it — a savings of $1.76 million per incident. Furthermore, the operational benefits compound over time as automation reduces manual security tasks.
Zero Trust Security and Regulatory Compliance
Compliance mandates are now among the most powerful drivers of zero trust adoption globally. Several frameworks now require or strongly recommend zero trust controls.
The U.S. Executive Order 14028, signed in 2021, mandates zero trust adoption across all federal agencies. PCI DSS 4.0 requires continuous authentication and micro-segmentation for cardholder data environments. HIPAA mandates strict access controls for protected health information. GDPR and CCPA require demonstrable data access governance — which zero trust architecture satisfies by design. The market is rapidly expanding as enterprises and governments worldwide adopt zero trust architectures amid escalating cyber threats and cloud migration, fueled by rising ransomware attacks and regulatory mandates like GDPR and NIST frameworks.
For organizations navigating multiple compliance requirements simultaneously, our guide to penetration testing types explains how regular offensive testing validates your zero trust controls are working as designed.
Zero Trust for Small and Medium Businesses
Zero trust is not exclusively for enterprise organizations with large security budgets. Small businesses with under 100 employees accounted for 58% of all ransomware victims according to the FBI’s 2025 IC3 Report. The good news is that ZTNA for SMBs is now accessible at entry-level price points.
Practically speaking, a small business can begin its zero trust journey with four foundational steps: deploying MFA across all accounts, adopting a cloud-based identity provider like Microsoft Entra ID or Okta, replacing the corporate VPN with a ZTNA solution, and implementing endpoint detection and response (EDR) on all company devices.
Cloud-delivered zero trust platforms from vendors including Zscaler, Cloudflare, and Palo Alto Networks offer subscription pricing that scales with organization size. Moreover, tariffs are accelerating adoption of software-based and cloud-delivered zero trust solutions, reducing reliance on expensive imported hardware over time. This trend benefits SMBs significantly.
Our guide to cybersecurity for small businesses provides additional tactical steps that complement a zero trust foundation.
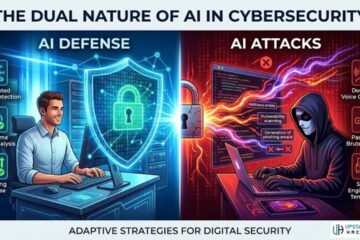
The Role of AI in Zero Trust Security
AI is transforming zero trust from a static policy framework into a dynamic, adaptive defense system. Traditional zero trust policies are rule-based — defined in advance and updated manually. AI-powered zero trust operates differently. It continuously learns normal access patterns, detects deviations in real time, and adjusts policies automatically based on risk signals.
In March 2026, Palo Alto Networks rolled out an enhanced zero trust SaaS-first platform integrating AI-driven risk scoring and automated policy orchestration, enabling organizations to dynamically adjust access controls based on real-time user and device behavior across cloud and hybrid environments.
Similarly, Microsoft announced expanded zero trust capabilities in Entra ID with AI-assisted conditional access recommendations and simplified multi-cloud resource tagging in January 2026, emphasizing automated risk-mitigation workflows and contextual signals from Microsoft Defender.
For a deeper understanding of how AI is reshaping offensive and defensive cybersecurity simultaneously, our guide on whether AI can do cybersecurity provides critical context for security leaders building zero trust programs.
Additionally, as AI-generated phishing attacks become exponentially more convincing — achieving 54% click-through rates compared to 12% for traditional phishing — zero trust’s identity pillar becomes the last reliable line of defense. Our guide on how to spot phishing emails covers the human-side controls that complement technical zero trust enforcement.
Top Zero Trust Security Vendors in 2026
The market has matured significantly. Leading platforms now integrate multiple zero trust pillars into unified cloud-delivered architectures.
| Vendor | Primary Strength | Best For |
|---|---|---|
| Zscaler | Cloud-native ZTNA, internet access security | Large enterprises, cloud-first organizations |
| Palo Alto Networks (Prisma) | AI-driven policy orchestration, endpoint integration | Comprehensive enterprise zero trust |
| Microsoft (Entra ID + Defender) | Identity-first ZTA, Microsoft ecosystem integration | Organizations on Microsoft 365/Azure |
| Okta | Identity and access management, workforce identity | Identity-led zero trust programs |
| Cisco (Duo + SD-Access) | Network segmentation, hybrid environments | Enterprises with complex network infrastructure |
| CrowdStrike | Endpoint-focused, threat intelligence integration | Security-mature enterprises |
| Cloudflare (One) | ZTNA, secure web gateway, SMB-friendly pricing | Mid-market and SMBs |
| Fortinet | Integrated hardware + software, OT security | Manufacturing, utilities, hybrid environments |
No single vendor covers all seven pillars completely. Most mature zero trust programs use two to three vendors for different layers, integrated through a SIEM platform.
Pros and Cons of Zero Trust Security
- Dramatically reduces lateral movement after a breach — one compromised account cannot access the entire network
- Reduces breach costs by an average of $1.76 million per incident compared to perimeter-based architectures
- Enables secure remote work without the risks of traditional VPN-based access
- Satisfies major compliance requirements including PCI DSS 4.0, HIPAA, GDPR, and Executive Order 14028
- Improves visibility across cloud, on-premises, and hybrid environments through centralized monitoring
- Supports AI workload security — machine identities, API endpoints, and LLM pipelines benefit from the same verification principles
- Complex to implement — requires significant planning, tool integration, and organizational change management
- Can disrupt user experience if MFA and access policies are implemented without careful UX design, driving shadow IT adoption
- Expensive initial investment — enterprise-grade zero trust programs require multi-year budgets and dedicated security engineering resources
- Legacy system compatibility remains a persistent challenge, particularly for OT environments and older on-premises applications
- Requires executive sponsorship — zero trust is not purely a technical project; cultural and process changes require leadership commitment
Our best cybersecurity companies guide covers vendors and managed service providers that can help organizations navigate these implementation challenges without building every capability in-house.
Real-World Zero Trust Failure: The Microsoft Midnight Blizzard Breach
No discussion of zero trust is complete without confronting a stark real-world lesson. In January 2024, Microsoft disclosed that Russian state-sponsored hackers from the Midnight Blizzard group had breached their corporate email systems. The entry point was not a sophisticated zero-day exploit. It was a simple password spray attack on a legacy test account that lacked multi-factor authentication.
Consequently, the attackers moved laterally for weeks, accessing senior leadership emails and source code repositories. Microsoft — a company that sells zero trust products — was compromised because one overlooked account operated outside their zero trust perimeter.
This is the exact scenario zero trust is designed to prevent. A mature zero trust program would have detected the anomalous login, required step-up authentication, and flagged the lateral movement attempt within minutes. The lesson is clear: zero trust is only as strong as its coverage. Partial implementation leaves critical gaps.
For teams building detection capabilities alongside zero trust controls, our guide on detecting deepfake audio in real time demonstrates how AI-powered detection tools are increasingly essential alongside architectural zero trust controls.
Frequently Asked Questions

What is zero trust security in simple terms?
Zero trust security means that no user, device, or application is automatically trusted — even if they are already inside your network. Every access request is verified every time using identity, device health, location, and behavior signals. It operates on the principle of “never trust, always verify,” which eliminates the dangerous assumption that anything inside the corporate firewall is safe.
What are the 7 pillars of zero trust security?
The seven pillars of zero trust as defined by NIST and CISA are: Identity (verifying users through MFA and continuous authentication), Devices (assessing endpoint health and compliance), Networks (implementing micro-segmentation and encrypted communications), Applications and Workloads (securing apps with per-application access controls), Data (classifying and protecting data at rest, in transit, and in use), Infrastructure (securing cloud, on-premises, and hybrid environments), and Visibility and Analytics (continuous monitoring and threat detection across all pillars).
How long does it take to implement zero trust security?
A basic ZTNA deployment for a 50-person business typically takes four to eight weeks end-to-end. Full zero trust maturity — reaching CISA’s Advanced level across all five pillars — is a six-to-eighteen month journey depending on legacy infrastructure complexity and organizational size. Most enterprises plan zero trust as a multi-year program, expanding coverage pillar by pillar rather than attempting a full simultaneous transformation.
Is zero trust security only for large enterprises?
No. Small businesses with under 100 employees account for 58% of all ransomware victims, making zero trust essential for organizations of every size. Cloud-delivered ZTNA platforms from Cloudflare, Zscaler, and Fortinet now offer subscription pricing accessible to SMBs. The foundation — MFA, a cloud identity provider, and EDR on all endpoints — is achievable for most small businesses within weeks, at modest cost.
What is the difference between zero trust and VPN?
A VPN grants broad network access once a user authenticates — effectively placing them inside the perimeter. Zero trust network access (ZTNA) grants access only to specific applications for which the user is explicitly authorized, session by session. Furthermore, ZTNA continuously validates identity and device health throughout the session, while a VPN authenticates once at connection. The shift from VPN to ZTNA is one of the highest-impact first steps in any zero trust implementation.
Final Thoughts
The castle-and-moat era of cybersecurity is definitively over. Perimeter-based security cannot protect organizations whose data lives in dozens of cloud services, whose employees work from everywhere, and whose supply chains are deeply digitally integrated. Zero trust security is not a trend — it is the foundational security architecture of the modern enterprise.
The path forward is clear. Start with identity. Enforce MFA everywhere. Deploy ZTNA to replace your VPN. Segment your network to limit lateral movement. Build visibility into every access request. And expand coverage pillar by pillar until continuous verification becomes the default for every user, device, and application in your environment.
Organizations that commit to zero trust in 2026 will be dramatically better positioned against the AI-powered threats, ransomware campaigns, and credential-based attacks that are defining the current threat landscape. Those that delay are operating on borrowed time.