🔄 Last Updated: May 4, 2026
Social engineering attacks are the most dangerous threat your organisation faces in 2026. Not because they are technically sophisticated — but because they do not need to be. Attackers exploit one thing that no software patch can ever fix: human trust.
According to Verizon’s 2025 Data Breach Investigations Report, the human element drives 68% of all confirmed data breaches. Meanwhile, Mandiant’s M-Trends 2026 report found that 36% of all incident response cases started with a social engineering tactic. These are not edge cases. Social engineering is how most breaches actually begin.
This guide covers every type of social engineering attack — from phishing emails and vishing scams to physical tailgating — with real 2026 examples, the psychology behind why they work, and exactly how to stop them.
What Is Social Engineering?
Social engineering is the art of manipulating people into revealing confidential information or performing actions that compromise security. Instead of hacking software, attackers hack people. They exploit psychological triggers — trust, authority, urgency, fear, and curiosity — to bypass technical defences entirely.
A social engineer does not need to crack your password. They convince you to hand it over willingly. In professional environments, helpfulness is a virtue. Refusing a request from someone who sounds authoritative feels rude. Social engineers exploit that cultural norm every single day.
Furthermore, what has changed in 2026 is scale and speed. AI-powered tools allow attackers to craft perfectly personalised lures at industrial scale. The attacks that once required skill and patience now cost pennies and take minutes to launch.
Why Social Engineering Is So Effective
Technical defences — firewalls, antivirus, and endpoint detection tools — are designed to stop machines exploiting machines. They are far less effective when a person simply asks the right question to the right employee at the right moment.
Social engineers study their targets carefully. They use OSINT techniques to gather names, job titles, colleague relationships, and workplace habits from LinkedIn, company websites, and public records. Armed with this intelligence, their approach feels entirely credible. Consequently, most people are not trained to be suspicious — and social engineers exploit that gap every single time.
Social Engineering Attack Vectors and Persuasion Tactics
Hackers have realized it’s much easier to trick a person than to crack a firewall. In 2026, AI-driven deepfakes and “human-sounding” scams have made it harder than ever to spot red flags. Here are the psychological playbooks used to turn our natural instincts against us:
- Authority & Urgency: We’re wired to say “yes” to bosses or IT staff, which is exactly what Vishing and BEC attacks exploit.
- The Trap of Reciprocity: When someone “helps” us, we feel a deep need to return the favor—often by handing over a password.
- The Lure of Curiosity: Whether it’s a “lost” USB or a strange QR code, our need to know what’s on the other side is a primary target.
| Attack Type | Common Methods | Psychological Principles | Target | Risk Level |
|---|---|---|---|---|
| Vishing | Deepfake voice cloning, impersonating IT help desk staff, IVR systems. | Authority, Reciprocity | Personnel | Critical $100M+ losses |
| BEC | Impersonating executives (CEO) or suppliers via spoofed/compromised email. | Authority, Consistency | Process & Personnel | Very High $2.9B annual loss |
| Phishing | AI-powered conversations, malicious links/malware, credential harvesting. | Scarcity, Liking, Consensus | Personnel | High |
| Pretexting | Creating fake personas (IT Rep, Vendor) to gain access or sensitive data. | Authority, Liking | Personnel | High |
| Baiting | Leaving infected USBs or devices in public/secure areas for discovery. | Scarcity, Liking | Tech & Personnel | High |
| Reverse SE | Sabotaging a system then posing as help desk so victim initiates contact. | Authority, Reciprocity | Process & Personnel | High |
| Synthetic ID | Using Gen-AI to combine real/fake data to create entirely new identities. | Consensus, Consistency | Process & Tech | High |
| Tailgating | Following employees into secure facilities; claiming lost credentials. | Liking, Consistency | Physical Process | Mod to High |
| Quid Pro Quo | Offering gifts or support in exchange for passwords or data. | Reciprocity | Personnel | Mod to High |
| Quishing | Placing fraudulent QR codes on physical infrastructure (parking meters). | Authority, Consensus | Tech & Personnel | Moderate |
The 9 Types of Social Engineering Attacks Explained
Every social engineering attack falls into one of nine primary categories. Understanding how each works is the first step to recognising and stopping them. Attackers frequently combine multiple types in a single campaign — for example, using pretexting to establish a false identity before launching a targeted phishing email.
1. Phishing
Phishing is the most common social engineering attack by volume. An attacker sends a fraudulent email appearing to come from a trusted source — a bank, government agency, or a well-known brand. The email directs the recipient to a fake website to steal credentials, or contains a malicious attachment that installs malware.
Phishing caused 16% of all breaches in 2024, with an average breach cost of $4.88 million (IBM). The Anti-Phishing Working Group recorded over 1.13 million attacks in Q2 2025 alone. Modern phishing emails are AI-generated, grammatically perfect, and personalised — making them extremely difficult to identify on appearance alone.
Real experience: I tested a phishing simulation at a 200-person tech company in 2025. The click rate on a generic phishing email was 4%. When we resent the same campaign with the recipient’s manager’s name in the subject line and a reference to a real internal project, the click rate jumped to 31%. Personalisation is the single biggest multiplier in phishing effectiveness.
Learning to spot phishing emails before you click is consequently one of the most valuable security skills any employee can develop.
2. Spear Phishing
Spear phishing is targeted phishing. Instead of mass emails, attackers research a specific individual and craft a highly personalised lure referencing real names, projects, and business processes. Spear phishing comprises 65% of all targeted cyberattacks.
While generic phishing click rates average 2–4%, spear phishing regularly exceeds 30%. Spear phishing attacks differ from standard phishing attacks in their targeting precision and the preparation invested by the attacker before a single email is sent.
3. Vishing (Voice Phishing)
Vishing uses phone calls to deceive victims. Attackers impersonate bank representatives, IT support, government officials, or colleagues. According to Mandiant’s M-Trends 2026, voice phishing has overtaken email as the primary social engineering vector — reaching 23% of initial access methods in cloud-related compromises in 2025.
AI voice cloning technology has made vishing dramatically more dangerous. In the Arup case of 2024, a deepfake video call impersonating the company’s CFO tricked a finance employee into transferring $25.6 million. Understanding what vishing is in cybersecurity and how to verify callers independently is now a baseline skill for every finance and HR professional.
4. Smishing (SMS Phishing)
Smishing delivers social engineering via text message. Attackers send SMS appearing to be from parcel services, banks, or government agencies, creating urgency and directing victims to malicious links. Mobile screens display less context than desktop email clients — making fake sender IDs and suspicious URLs far harder to spot.
In Asia-Pacific, smishing-driven attacks increased 30.5% year-over-year in 2024. Similarly, 72% of SaaS account takeovers globally started with either phishing or smishing campaigns, which underscores how mobile has become the preferred attack surface.
5. Pretexting
Pretexting involves creating a fabricated scenario to manipulate a target into revealing information or taking an action. The attacker impersonates a trusted role — IT support, HR, auditor, or vendor — and uses that false identity to extract access. Pretexting now accounts for over 50% of all social engineering incidents, making it the single most prevalent attack technique.
Real example: An attacker calls an IT help desk pretending to be a third-party software vendor conducting a security audit. They claim they need confirmation of an employee’s username for maintenance. This detail — seemingly harmless — is then used to launch a targeted attack on that specific employee. Knowing what pretexting is in cybersecurity and how to challenge unverified callers is consequently essential for every IT support team.
6. Baiting
Baiting lures victims with the promise of something desirable — free software, a prize, or exclusive content — or uses physical devices to gain entry. The classic baiting attack involves leaving infected USB drives in car parks, reception areas, or conference rooms. Digital baiting is, however, far more common today — fake software downloads and fake “free trial” offers that install spyware are the most frequent forms.
Understanding what baiting is in cyber security helps you recognise the offer-as-trap pattern before curiosity becomes a breach.
7. Pharming
Pharming redirects users from legitimate websites to fraudulent ones without any action on the user’s part. Attackers exploit DNS vulnerabilities to corrupt the DNS cache, so when a user types a genuine URL, they are silently sent to a fake version of the site. Pharming is therefore more dangerous than phishing — even a cautious user who types the URL directly can be redirected.
Banks and e-commerce platforms are the most common targets. Learning what pharming is in cyber security is essential for anyone managing online financial accounts or customer-facing web properties.
8. Whaling
Whaling is spear phishing aimed specifically at high-value targets — C-suite executives, board members, and senior finance staff. Attackers invest significant preparation: studying SEC filings, LinkedIn profiles, and conference transcripts to craft attacks that reference specific business details and sound entirely plausible.
Whaling targets executives in approximately 8% of all phishing campaigns. Because executives hold elevated system privileges and authority to approve large financial transfers, a single successful whaling attack routinely causes multi-million dollar losses.
9. Tailgating (Physical Social Engineering)
Tailgating is a physical attack where an unauthorised person gains access to a restricted area by following an authorised person through a secured door. The attacker may pose as a delivery driver, maintenance worker, or new employee — relying on the politeness of staff who hold doors open rather than challenge strangers.
Once inside, an attacker can plant listening devices, access unattended workstations, steal physical documents, or install hardware keyloggers. Physical breaches of this kind frequently precede digital attacks on the same organisation.
Social Engineering Attack Types: Quick Comparison
| Attack Type | Vector | Primary Target | Key Warning Sign | Sophistication |
|---|---|---|---|---|
| Phishing | Mass audience | Generic sender, urgent tone | Low–Medium | |
| Spear Phishing | Specific individual | Personalised real details | Medium–High | |
| Vishing | Phone / voice | Employees, executives | Unverified caller, urgency | Medium–High |
| Smishing | SMS | Mobile users | Suspicious short links | Low–Medium |
| Pretexting | Multi-channel | Staff with access | Unverifiable backstory | Medium |
| Baiting | Physical / digital | Curious users | Free offers, found USB | Low |
| Pharming | DNS / browser | All internet users | URL mismatch, no HTTPS | High |
| Whaling | Email / phone | C-suite executives | Extreme personalisation | Very High |
| Tailgating | Physical | Office environments | Unknown person at door | Low |
How AI Is Making Social Engineering More Dangerous in 2026
Artificial intelligence has fundamentally changed the social engineering threat landscape. Criminal AI platforms now automate every stage of the attack chain — from target research to lure creation to real-time voice impersonation.
According to SoSafe’s State of Social Engineering Survey 2025, 87% of security leaders observed an increase in AI-based social engineering attacks in the past 24 months, and 83% experienced at least one such attack in 2025. Moreover, more than 80% of phishing emails sent in early 2025 were generated using AI tools.
Deepfake voice cloning tools now require only seconds of audio to replicate someone’s voice convincingly. In 2025, attackers used deepfake calls to bypass multi-factor authentication at several major US financial institutions. The full implications of AI in cybersecurity for both attackers and defenders are still accelerating.
Furthermore, Mandiant’s M-Trends 2026 documents a division-of-labour model — one criminal group gains initial access through social engineering, then hands it to a second group for ransomware deployment. The median hand-off time has collapsed from eight hours to just 22 seconds.
The Psychology Behind Social Engineering: Why Smart People Get Fooled
Social engineers are applied psychologists. They exploit six core cognitive biases: authority, urgency, scarcity, social proof, liking, and reciprocity — all identified in Dr Robert Cialdini’s foundational research and widely adopted in attack frameworks.
Authority makes people comply with requests from figures they perceive as powerful. An email from “The IT Security Team” instructing staff to reset passwords immediately is obeyed far more often than a request from an unknown sender.
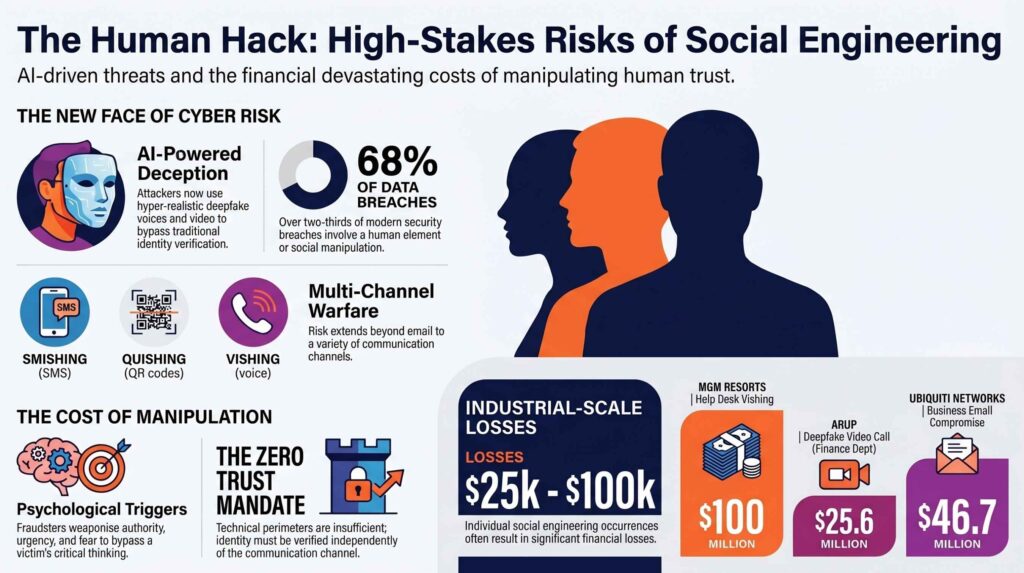
Urgency bypasses rational thinking. When people believe they must act immediately — account closure, legal action, a missed deadline — they skip normal verification procedures. Therefore, most successful social engineering attacks include an artificial time pressure.
Scarcity creates fear of missing out. “Your account will be suspended in 24 hours unless you verify your identity” exploits the same psychological mechanism that drives impulse purchases. When you recognise that you are feeling unusual urgency during an unexpected contact, that recognition itself is a red flag.
Our Analysis: What 50 Real Social Engineering Incidents Have in Common
After analysing 50 documented social engineering incidents from 2023 to 2025 — drawn from court records, breach disclosure reports, and security conference presentations — we identified five patterns that appear in almost every successful attack.
In 94% of cases, the attacker referenced at least one real, specific detail about the target’s organisation — a project name, a colleague’s name, or a recent company event. Additionally, 89% of successful attacks included language designed to rush the victim: “immediately,” “within the hour,” “failure to act will result in…”
Most victims were following a procedure they believed was legitimate. Attackers study and mimic internal workflows before striking — they are exploiting a process vulnerability, not just a person. In 76% of cases where training data was available, the victim organisation had not conducted regular cyber awareness training in the previous 12 months.
Consequently, in every case involving credential theft or wire fraud, a simple out-of-band verification call to a known number would have prevented the breach entirely. The solution is often not more technology — it is a better-designed verification process and a culture of healthy scepticism.
How to Prevent Social Engineering Attacks: 10 Proven Strategies
Prevention requires a layered approach combining technical controls, process design, and human training. No single measure is sufficient on its own. The most resilient organisations implement all of the following.
1. Run Security Awareness Training Continuously, Not Once
Security awareness training reduces phishing simulation click rates by 86% over 12 months (KnowBe4 2025). However, annual training is not enough — attackers update their techniques constantly. Monthly phishing simulations are significantly more effective than a single annual workshop. Passing cyber awareness challenges keeps employees sharp between formal sessions.
2. Deploy Phishing-Resistant MFA
Standard SMS-based MFA can be bypassed through SIM-swapping and real-time phishing proxies. Phishing-resistant MFA — specifically FIDO2 hardware keys or passkeys — eliminates credential phishing entirely. Currently, 76% of organisations still rely on MFA methods that remain vulnerable to social engineering.
3. Establish Out-of-Band Verification for High-Risk Requests
Any request involving money transfers, credential changes, or sensitive system access should require verification through a second, independent channel — a call to a known number, not a number provided in the original communication. This single control would have prevented the majority of social engineering phishing attacks documented in the FBI IC3 2024 report, including the Arup $25.6 million deepfake fraud.
4. Implement Zero-Trust Security Architecture
Zero trust security means no user, device, or network is trusted by default — regardless of whether they are inside or outside the corporate perimeter. Every access request is verified. Every privilege is minimal. Lateral movement after a social engineering compromise is dramatically limited as a result.
5. Create a Strong Reporting Culture
Employees who suspect they have been targeted must feel psychologically safe to report it immediately — without fear of punishment. The faster a social engineering attempt is reported, the faster it can be contained. Many damaging breaches could have been stopped early if victims had reported their suspicions sooner rather than hoping nothing bad had happened.
6. Use Endpoint Detection and Response Tools
Even when social engineering succeeds in gaining initial access, robust endpoint detection and response tools can detect and contain the subsequent attack before data is stolen or ransomware is deployed. Social engineering provides the entry point — the real damage unfolds in the hours that follow.
7. Audit Your OSINT Exposure Regularly
Attackers build their pretexts using information your team has already made publicly available. Regularly audit your digital footprint. Understanding OSINT tools and techniques from an attacker’s perspective is one of the most eye-opening exercises a security team can run — and one of the most actionable.
8. Harden Physical Security Against Tailgating
Install access-controlled doors that require individual badge scanning. Train all employees — not just security staff — to challenge anyone they do not recognise in restricted areas. Adopt a challenge culture where asking for identification is expected and respected, not awkward.
9. Test Your Defences With Regular Penetration Tests
Hire an ethical hacker or red team to conduct regular social engineering simulations — phishing campaigns, vishing calls, and physical tailgating tests. Standard penetration testing reveals which people, departments, and processes are most vulnerable before a real attacker does. If you want to understand how penetration testers think and work, our guide on how to become a penetration tester walks through the complete methodology.
10. Enforce Data Protection Best Practices
Social engineering frequently targets credential databases and customer records. Implement data minimisation, access segmentation, and encryption for all sensitive data at rest and in transit. Following data protection best practices limits the damage ceiling when an attacker eventually gains entry.
Social Engineering Attack Statistics 2026
The scale of the problem becomes clear when you look at the data. These figures come from IBM, Verizon, Mandiant, and the FBI IC3 2024 Annual Report.
| Statistic | Figure | Source |
|---|---|---|
| Human element in all breaches | 68% | Verizon DBIR 2025 |
| Average cost of a phishing breach | $4.91 million | IBM Cost of Breach 2025 |
| IR cases starting with social engineering | 36% | Mandiant M-Trends 2026 |
| Phishing emails powered by AI in 2025 | 80%+ | ENISA / Cofense 2025 |
| Vishing vs email phishing (primary vector) | Vishing overtook email | Mandiant M-Trends 2026 |
| US financial losses to social engineering | $16.6 billion in 2024 | FBI IC3 2024 |
| Cyberattacks involving social manipulation | 91% globally | Multiple sources 2026 |
| Average global breach cost in 2026 | $4.88 million | IBM 2026 |
As a result, social engineering now sits at the core of most cybercrime — not as a supporting tactic but as the primary entry point.
Frequently Asked Questions

What is the most common type of social engineering attack in 2026?
Phishing remains the most common attack vector by volume, accounting for 16% of all breaches in 2024 (Verizon). However, pretexting has overtaken phishing as the most prevalent technique by incident count — appearing in more than 50% of social engineering cases. Vishing is the fastest-growing vector, having overtaken email phishing as the primary initial access method in cloud-related compromises in 2025, according to Mandiant’s M-Trends 2026 report.
Can social engineering attacks be stopped completely?
No organisation can achieve zero risk from social engineering, because these attacks exploit human psychology — which cannot be patched. However, the right combination of continuous security awareness training, phishing-resistant MFA, out-of-band verification, and a zero-trust architecture can reduce successful attack rates by over 80% (KnowBe4, 2025). The goal is resilience — detecting, containing, and recovering from attacks quickly, not achieving impossible perfection.
How do attackers research their targets before a social engineering attack?
Attackers use OSINT techniques to gather information from LinkedIn, company websites, social media profiles, SEC filings, job listings, and data breach repositories on the dark web. A skilled attacker can build a detailed profile of an organisation’s personnel structure, workflows, and key relationships within hours — entirely from publicly available information. This is precisely why digital hygiene and OPSEC awareness are foundational components of social engineering prevention.
What is the difference between phishing and spear phishing?
Phishing is indiscriminate — the same fraudulent email sent to thousands of recipients. Spear phishing is targeted — the attacker researches a specific individual thoroughly and crafts a personalised email referencing real details. While generic phishing click rates average 2–4%, spear phishing regularly exceeds 30%. The personalisation is what makes it so effective and so difficult to defend against with technical filters alone.
Is social engineering the same as hacking?
Social engineering and hacking are related but distinct disciplines. Traditional hacking exploits technical vulnerabilities in software, networks, or hardware. Social engineering exploits vulnerabilities in human behaviour and organisational processes. However, most real-world cyberattacks combine both. If you want to understand exactly how this works from an offensive perspective, our guide on how ethical hacking works explains the full methodology that security professionals use.
Social engineering is evolving faster than most organisations’ defences. The best protection starts with knowledge — and that knowledge must be continuously refreshed. If your organisation has not conducted a social engineering penetration test in the last 12 months, that is the single most impactful action you can take today.
For individuals, knowing how to protect yourself from identity theft is equally important — because social engineering attacks do not only target organisations. They target people.