🔄 Last Updated: May 6, 2026
Cybersecurity Analyst & Tech Journalist · Upstanding Hackers
James Turner is a technology journalist and cybersecurity analyst with over a decade covering the information security industry. He specialises in threat intelligence, ethical hacking methodology, and digital defense strategy, translating complex attack vectors and security frameworks into clear, actionable guidance. At Upstanding Hackers, James covers penetration testing types, social engineering attacks, OSINT tools and techniques, AI-driven threats, and zero trust security architecture.
Ethical hacking is one of the most in-demand skills in the world right now. Cybercrime costs are projected to reach $23 trillion annually by 2027, and organisations are desperately searching for professionals who can think like an attacker before the attackers strike. The ethical hacker is that professional.
The average salary of an ethical hacker in 2026 is approximately $169,226 in the US alone, according to Glassdoor. Meanwhile, the US Bureau of Labor Statistics predicts 32% job growth in cybersecurity between 2022 and 2032 — far above the average for any other profession. The demand is real, the pay is exceptional, and the work genuinely matters.
This guide covers everything you need to know — what ethical hacking is, how it works, the methodologies professionals follow, the tools they use, the certifications that open doors, and the realistic path from complete beginner to paid ethical hacker. If you have ever wondered whether this career is right for you, this is where you find out.
What Is Ethical Hacking?
Ethical hacking is the authorised practice of bypassing a system’s security to identify vulnerabilities before malicious hackers can exploit them. An ethical hacker — also called a white-hat hacker or become a penetration tester — uses the same techniques, tools, and thinking patterns as a criminal attacker. The critical difference is permission. Every test is conducted under a formal agreement with the system owner, within defined legal boundaries, to improve security rather than cause harm.
The concept is straightforward: the best way to find the holes in your defences is to try to break through them yourself. A firewall that has never been tested against real attack techniques is not a proven defence — it is an assumption. Ethical hacking replaces that assumption with evidence.
Ethical hacking sits within the broader discipline of offensive security — the practice of proactively testing systems rather than simply monitoring them. It encompasses penetration testing, red team exercises, vulnerability assessments, and bug bounty research. Each varies in scope and methodology, but all share the same foundational purpose: finding what attackers would find, before attackers do.
White Hat, Grey Hat, and Black Hat Hackers
Not all hackers operate the same way. The cybersecurity industry uses a colour-coded framework to distinguish between them. Understanding this distinction matters, particularly if you are considering a career in security.
White-hat hackers operate legally and ethically. They have explicit permission from the target organisation before conducting any testing. All findings are reported to the client. All work is governed by a contract. This is the domain of professional ethical hackers.
Grey-hat hackers occupy an ambiguous middle ground. They may test systems without permission but with no malicious intent — often disclosing vulnerabilities after discovery. While their motivations may be benign, their methods are still illegal in most jurisdictions.
Black-hat hackers are criminal attackers. They exploit vulnerabilities for financial gain, espionage, disruption, or personal satisfaction. They have no authorisation and no legal protection. This is the adversary that ethical hackers are trained to simulate.
The lines between these categories matter enormously in practice. Even well-intentioned security researchers have faced prosecution for testing systems without explicit written permission. Ethical hacking careers are built entirely in white-hat territory.
Why Ethical Hacking Matters More Than Ever in 2026
The case for ethical hacking has never been stronger. Weekly volumes of cyberattacks now hit an average of 1,968 per week — an 18% year-over-year increase from 2025, and a 70% rise since 2023. Organisations that wait for an attacker to find their vulnerabilities are playing a losing game.
The global cybersecurity market was estimated at USD 245.6 billion in 2024 and is projected to expand to USD 500.7 billion by 2030, growing at a CAGR of approximately 12.9%. A significant portion of that spend flows to penetration testing and offensive security services. The penetration testing market is projected to grow from USD 2.74 billion in 2025 to USD 6.25 billion by 2032 at a 12.5% CAGR.
Furthermore, regulatory pressure is intensifying. Frameworks like ISO 27001, SOC 2, PCI-DSS, and HIPAA increasingly require documented penetration testing as a compliance condition. Organisations that once treated ethical hacking as optional now treat it as mandatory. This has fundamentally shifted demand.
Similarly, the rise of agentic AI — autonomous AI agents for business capable of scanning networks, adapting phishing campaigns, and launching attacks with minimal human input — is one of the biggest shifts toward AI-powered cyberattacks in 2026. As attack techniques grow more sophisticated, the humans defending organisations need to stay one step ahead. Ethical hackers are how organisations do that.
Cybersecurity Certifications and Training Comparison Guide
| Certification | Level | Domains & Skills | Hands-on Labs | Target Roles |
|---|---|---|---|---|
| Certified Ethical Hacker (CEH) | Intermediate | Footprinting, Reconnaissance, Vulnerability Analysis, Malware, Social Engineering, SQL Injection, IoT/OT, Cloud, Cryptography | 220 Labs | Ethical Hacker, SOC Analyst, Pen Tester |
| Certified Cybersecurity Technician (CCT) | Beginner | Network Defence, Ethical Hacking, Digital Forensics, Security Operations, Incident Response | 85 Labs | SOC Analyst, Cybersecurity Technician |
| CompTIA Security+ | Beginner | Attacks, Threats, Architecture, Design, Governance, Risk and Compliance | 32 Labs | Security Consultant, Systems Administrator |
| Certified Penetration Testing Professional (CPENT) | Advanced | Advanced Windows Attacks, IoT/OT Pen Testing, Exploit Writing, Binary Exploitation | Cyber Range Challenges | Certified Penetration Tester |
| Certified Network Defender (CND) | Intermediate | Protecting, detecting, and responding to network threats | Major network security tools | Network Administrator |
| Certified Threat Intelligence Analyst (CTIA) | Advanced | Threat intelligence building, identifying business risks, converting unknown threats | Structured Intelligence approach | Threat Intelligence Analyst |
| CISSP / CISO | Management | Security Policy Implementation and Strategic Management | N/A | Management Class |
| OSCP / CPTE | Advanced | Offensive Security and Advanced Penetration Testing | Practical Cyber Range | Ethical Hacker, Penetration Tester |
The Ethical Hacking Methodology: How It Works Step by Step
Professional ethical hacking follows a structured methodology. This structure exists for two reasons: it ensures comprehensive coverage of the target, and it creates a defensible, documented record of the engagement. Most professional ethical hackers follow a five-phase framework.
Phase 1 — Reconnaissance
Reconnaissance is the intelligence-gathering phase. The ethical hacker collects as much information as possible about the target before touching a single system. This includes passive reconnaissance — gathering publicly available data through OSINT tools and techniques — and active reconnaissance, which involves directly probing the target’s infrastructure.
Information gathered in this phase includes IP address ranges, domain names, employee names and email formats, technologies in use, open ports, and any previously disclosed vulnerabilities. The quality of reconnaissance directly determines the quality of the rest of the engagement.
Phase 2 — Scanning and Enumeration
With reconnaissance complete, the ethical hacker moves to active scanning. Network scanning tools map the target’s live hosts, open ports, running services, and operating systems. Vulnerability scanners identify known weaknesses in software versions, configurations, and exposed interfaces.
This phase transforms the intelligence gathered in reconnaissance into a concrete attack surface. Every open port is a potential entry point. Every outdated software version is a potential vulnerability. The ethical hacker documents everything systematically.
Phase 3 — Gaining Access
This is the phase most people picture when they think of hacking. The ethical hacker uses the vulnerabilities identified in phases one and two to actually compromise the target system. This may involve exploiting a software vulnerability, cracking weak credentials, launching a social engineering attack, or chaining multiple smaller weaknesses together to achieve a meaningful level of access.
Gaining access in a professional engagement is always conducted within the agreed scope. Ethical hackers never escalate beyond what the client has authorised, and never cause damage to production systems.
Phase 4 — Maintaining Access and Privilege Escalation
Once initial access is gained, the ethical hacker tests how deeply an attacker could entrench themselves. This involves privilege escalation — moving from a limited user account to administrator or root access — and persistence testing, which determines how long an attacker could remain in the system undetected.
This phase is crucial for understanding network security vulnerabilities in realistic attack scenarios. Most significant breaches involve an attacker who has been inside the network for days or weeks before detection.
Phase 5 — Reporting
The final phase is arguably the most important from a client’s perspective. Every finding is documented in detail: the vulnerability discovered, the method used to exploit it, the potential business impact if a real attacker exploited it, and a clear, prioritised remediation recommendation. Good ethical hacking reports are actionable. They give security teams a ranked list of what to fix first.
Essential Ethical Hacking Tools in 2026
The tools used by ethical hackers are the same tools used by criminal attackers — the difference is the authorisation behind their use. These are the tools every serious ethical hacker knows thoroughly.
| Tool | Purpose | Category |
|---|---|---|
| Nmap | Network scanning and port enumeration | Reconnaissance |
| Metasploit Framework | Exploitation and post-exploitation | Exploitation |
| Burp Suite | Web application vulnerability testing | Web Security |
| Nessus / OpenVAS | Automated vulnerability scanning | Vulnerability Assessment |
| Wireshark | Network traffic analysis and packet capture | Network Analysis |
| Aircrack-ng | Wireless network security testing | Wi-Fi Security |
| Hashcat / John the Ripper | Password cracking and hash analysis | Credential Testing |
| Kali Linux | Purpose-built penetration testing OS | Platform |
| Cobalt Strike | Red team command and control | Advanced Red Team |
| BloodHound | Active Directory attack path analysis | Privilege Escalation |
Most ethical hackers build their foundational skills on Kali Linux — a Debian-based operating system pre-loaded with hundreds of security testing tools. It is the industry-standard platform for beginners and professionals alike. Setting up a home hacking lab with Kali Linux running in a virtual machine is the single most practical first step any aspiring ethical hacker can take.
Metasploit remains the most widely used exploitation framework in professional penetration testing. It provides a structured environment for launching, testing, and documenting exploits. Learning Metasploit is essential for anyone pursuing a hands-on offensive security career.
Burp Suite is the dominant tool for web application security testing. Given that web applications are the most common attack surface in modern organisations, proficiency in Burp Suite is a baseline requirement for most penetration testing roles.
Ethical Hacking Certifications: Which One Should You Get?
Certifications validate your skills to employers and clients. In ethical hacking, three certifications consistently appear in job descriptions and carry the most professional weight.
CEH — Certified Ethical Hacker (EC-Council)
The CEH is the most widely recognised entry-level ethical hacking certification globally. It covers the full ethical hacking methodology across 20 modules — reconnaissance, scanning, enumeration, system hacking, malware, sniffing, social engineering, session hijacking, and more. The CEH is primarily knowledge-based, with an exam format that favours theoretical understanding over hands-on demonstration.
The CEH is ideal if you are new to offensive security and need a vendor-recognised credential to get your first role. It opens doors. It is, however, not a substitute for hands-on skills.
OSCP — Offensive Security Certified Professional (OffSec)
The OSCP is the gold standard of hands-on penetration testing certifications. Unlike the CEH, the OSCP exam is entirely practical — candidates must compromise a series of target machines within 24 hours and submit a professional penetration testing report. There are no multiple-choice questions. You either hack the machines or you do not pass.
The OSCP is significantly harder to obtain than the CEH. It is also significantly more respected by employers, particularly for hands-on penetration testing roles. CEH vs OSCP: which certification should you get is a question every aspiring pen tester asks — and the answer depends on where you are in your career.
CompTIA Security+
Security+ is not an ethical hacking certification, but it is the most common prerequisite. It validates foundational cybersecurity knowledge and is frequently required before employers will consider candidates for offensive security roles. If you are starting from zero, Security+ is typically the right first step before pursuing CEH or OSCP.
Bug Bounty Platforms as Practical Certification
Beyond formal certifications, bug bounty platforms — specifically HackerOne and Bugcrowd — offer something certifications cannot: proof of real-world results. Ethical hackers who have found and responsibly disclosed real vulnerabilities in production systems command significant credibility in the job market. Many successful penetration testers built their reputations through legal ways to make money as a hacker via bug bounty programmes before ever holding a salaried role.
Ethical Hacking Career Paths and Salaries in 2026
Ethical hacking skills open multiple career pathways, each with different day-to-day responsibilities and compensation ranges.
| Role | Avg Salary (US, 2026) | Primary Responsibility |
|---|---|---|
| Penetration Tester | $95,000 – $145,000 | Simulated attacks on client systems |
| Security Analyst (SOC) | $90,000 – $120,000 | Monitor, detect, and respond to threats |
| Vulnerability Assessor | $85,000 – $115,000 | Identify and document system weaknesses |
| Red Team Operator | $130,000 – $175,000 | Full-scope adversary simulation |
| Ethical Hacker / Consultant | $120,000 – $169,226+ | Client-facing security testing and advisory |
| Bug Bounty Researcher | Variable ($0 – $500k+) | Independent vulnerability discovery |
Sources: Glassdoor 2026, BLS Occupational Outlook 2025
The highest-paying roles in ethical hacking consistently go to professionals who combine technical depth with strong communication skills. A penetration tester who can explain a critical finding to a CEO in plain English is worth considerably more than one who cannot. Writing clear, professional reports is therefore as important a skill to develop as technical exploitation.
How to Start Learning Ethical Hacking: A Realistic Roadmap
The path from beginner to working ethical hacker is achievable in 12 to 18 months with consistent, focused effort. This is the sequence that produces results.
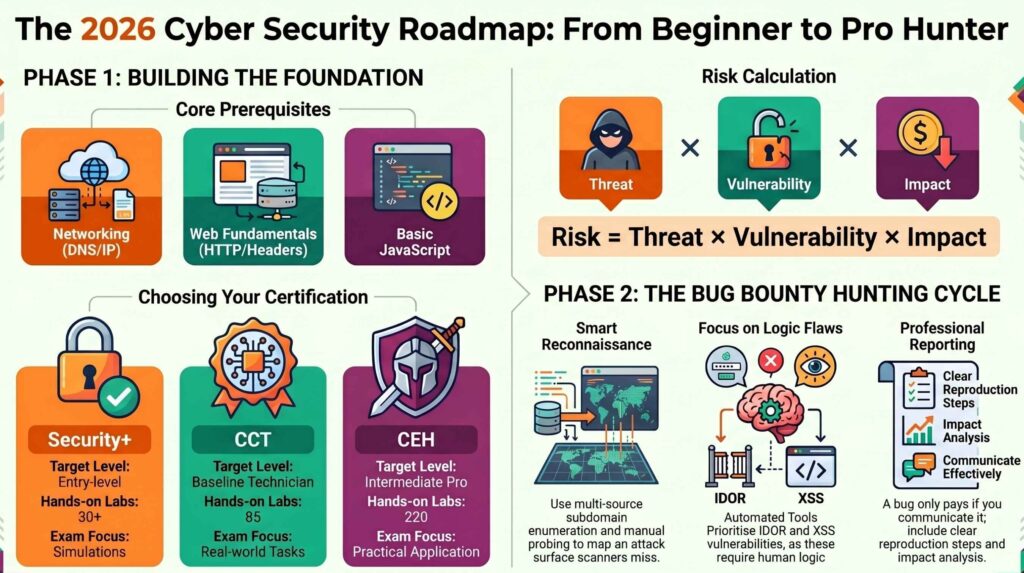
Months 1–3: Build the Foundation. Learn networking fundamentals — TCP/IP, DNS, HTTP, subnetting, and how routers and switches work. Learn Linux basics, particularly the command line. Study the CompTIA Security+ syllabus. These are not optional prerequisites — they are the ground floor. Without them, advanced hacking techniques are impossible to understand deeply.
Months 3–6: Learn Offensive Fundamentals. Set up a home hacking lab using VirtualBox or VMware with Kali Linux. Begin working through TryHackMe’s learning paths — particularly “Jr Penetration Tester.” Start understanding how to use Nmap, Metasploit, and Burp Suite in controlled, legal environments. Take your CompTIA Security+ exam.
Months 6–9: Develop Hands-On Skills. Move to HackTheBox, which presents more realistic and challenging machines. Study for and take the CEH exam. Begin following cybersecurity researchers on social media, reading security blogs, and attending virtual conferences. Start reading CVE reports to understand how real vulnerabilities are discovered and disclosed.
Months 9–18: Pursue OSCP and Enter the Job Market. Enrol in OffSec’s PWK (Penetration Testing with Kali Linux) course — the prerequisite for the OSCP exam. This course changes how you think about security. Simultaneously, begin building a portfolio: a professional GitHub, documented CTF write-ups, and if possible, a bug bounty disclosure. Understanding how to protect websites from hackers from both the offensive and defensive perspective gives you the rounded knowledge employers want.
Our full guide on how to become a penetration tester goes deeper into each of these phases, including the specific resources, labs, and learning platforms that produce the best results.
Ethical Hacking vs Penetration Testing: Is There a Difference?
These terms are often used interchangeably, but there is a meaningful distinction. Ethical hacking is the broader practice — it includes any authorised attempt to compromise a system’s security, regardless of methodology or scope. Penetration testing is a specific, structured form of ethical hacking conducted within a formally defined scope, timeframe, and rules of engagement.
Think of penetration testing as a formal, contracted service delivered to a client. Think of ethical hacking as the skill set that makes penetration testing possible. All penetration testers are ethical hackers, but not all ethical hacking takes the form of a formal penetration test.
Similarly, red teaming is a more advanced form of ethical hacking that simulates a sophisticated, persistent adversary — often with no predefined scope and with objectives like “exfiltrate this data” rather than “test this application.” Understanding penetration testing types and what you need to know is, therefore, essential context for anyone entering this field.
Legal and Ethical Boundaries: What You Must Never Do
Ethical hacking without authorisation is a criminal offence in virtually every jurisdiction. In the United States, the Computer Fraud and Abuse Act (CFAA) imposes federal criminal penalties for unauthorised computer access. In the UK, the Computer Misuse Act 1990 covers equivalent offences. Similar legislation exists in Australia, Canada, the EU, and most other major jurisdictions.
The rules are clear: never test a system you do not own or have explicit written permission to test. This includes systems you suspect are insecure, systems belonging to employers without formal authorisation, and public-facing systems of organisations you intend to help. Good intentions do not constitute legal authorisation.
Professional ethical hackers always work under a formal contract — typically called a rules of engagement document or a statement of work — that defines the scope of testing, the permitted techniques, the timeframe, and the liability boundaries for both parties. This document is your legal protection. Never begin an engagement without it.
Furthermore, responsible disclosure is the ethical standard for any vulnerability discovered outside a formal engagement. If you find a security flaw in a website or application you are using legitimately, the ethical response is to report it privately to the organisation through their security contact or bug bounty programme — not to exploit it, publish it, or disclose it publicly before a fix is available.
The Role of AI in Ethical Hacking in 2026
AI is transforming both the attack landscape and the defender’s toolkit. Ethical hackers who understand AI in cybersecurity are better positioned than those who do not. On the offensive side, AI tools now assist with automated reconnaissance, intelligent fuzzing, and generating more convincing phishing lures for social engineering tests.
On the defensive side, AI-powered detection tools make the ethical hacker’s job simultaneously harder and more valuable. Harder, because AI-based EDR systems are better at detecting standard exploitation techniques. More valuable, because organisations need human red teamers who can find the gaps that automated tools miss.
Gartner predicts that by 2026, enterprises that combine GenAI with an integrated platform-based architecture in security behaviour and culture programmes will experience 40% fewer employee-driven security incidents. This creates an expanding market for ethical hackers who can assess and test AI-integrated security environments — a specialisation that barely existed three years ago and is already commanding premium rates.
Frequently Asked Questions

What is the difference between ethical hacking and cybersecurity?
Cybersecurity is the broad discipline of protecting systems, networks, and data from attack. Ethical hacking is one specific practice within cybersecurity — the offensive, proactive side. Most cybersecurity work is defensive: monitoring systems, configuring firewalls, patching software, and responding to incidents. Ethical hacking is offensive: actively trying to breach those defences to find weaknesses before attackers do. Both are essential, and the best security professionals understand both perspectives deeply.
Do you need a degree to become an ethical hacker?
No degree is required to work as an ethical hacker. The field is heavily skills-based and certification-driven. Many working penetration testers are entirely self-taught. What matters to employers is demonstrated competence — a combination of certifications (OSCP, CEH, Security+), a portfolio of practical work (CTF write-ups, bug bounty disclosures, documented lab projects), and the ability to communicate findings clearly. A degree in computer science or cybersecurity can accelerate learning, but it is not a gate. Our guide on how to become a hacker for beginners covers the non-degree path in detail.
Is ethical hacking legal?
Ethical hacking is completely legal when conducted with explicit written authorisation from the system owner. Without that authorisation, the exact same activities constitute criminal offences under computer misuse legislation in most countries. The authorisation — typically a formal contract or rules of engagement document — is what makes hacking ethical and legal. Never test any system you do not own or have not been explicitly contracted to test.
How long does it take to learn ethical hacking?
A realistic timeline for building employable ethical hacking skills is 12 to 18 months with consistent, focused daily practice. The first three months are foundational — networking, Linux, and basic security concepts. Months three to nine develop hands-on offensive skills through lab practice and certifications. The final phase involves pursuing the OSCP and building a professional portfolio. Some people reach employment faster; some take longer. The variable is not talent — it is consistency.
What programming languages do ethical hackers need to know?
Python is the most important language for ethical hackers — it is used for scripting exploits, automating reconnaissance tasks, and building custom security tools. Bash scripting is equally essential for working efficiently on Linux systems. Beyond these two, knowledge of JavaScript is valuable for web application testing, while understanding C and Assembly helps with low-level vulnerability research and exploit development. You do not need to be a professional software developer to work in ethical hacking, but you do need to be comfortable reading, writing, and modifying code. Our guide on the easiest programming language to learn for hackers covers this in depth.
Ethical hacking is not just a career — it is one of the most meaningful roles in modern technology. Every vulnerability an ethical hacker finds and helps fix is a real-world attack prevented. Every penetration test that leads to a security improvement makes an organisation genuinely safer.
If you are serious about entering this field, the next steps are practical. Build your lab. Start your Security+ studies. Open a TryHackMe account tonight. The gap between where you are and where you want to be closes one skill at a time. For a complete view of the best cybersecurity companies hiring ethical hackers right now, and the roles they offer, our curated guide covers the employers most actively building offensive security teams in 2026.