🔄 Last Updated: May 11, 2026
Cybersecurity Analyst & Tech Journalist · Upstanding Hackers
James Turner is a technology journalist and cybersecurity analyst with over a decade covering the information security industry. He specialises in threat intelligence, ethical hacking methodology, and digital defense strategy, translating complex attack vectors and security frameworks into clear, actionable guidance. At Upstanding Hackers, James covers penetration testing types, social engineering attacks, OSINT tools and techniques, AI-driven threats, and zero-trust architecture.
A watering hole attack is one of the most dangerous and least understood threats in cybersecurity today. It bypasses your email filters, evades your firewall, and exploits the one thing no security tool can fully protect: your users’ trust in websites they visit every single day.
The concept borrows from nature. A predator that cannot reach its prey directly waits patiently at the watering hole — the one place prey must eventually go. In cybersecurity, attackers who cannot breach a hardened target directly compromise the external websites that target’s employees visit routinely. Industry forums. Vendor portals. Government resource sites. Trade association pages. The victim visits a site they trust completely. The attack happens invisibly in the background.
Nation-state groups like APT29 have used this technique against government websites as recently as 2024 and 2025. Meanwhile, a researcher described the DarkSword campaign as a textbook watering hole: it compromises a website and then waits for victims to visit. In late December 2025, the official download page of EmEditor — a widely used text and code editor — was compromised by attackers distributing a trojanized version of the software to every user who downloaded it normally.
This guide covers exactly what a watering hole attack is, how it works step by step, every major real-world case from 2023 through 2026, how it differs from phishing and supply chain attacks, and the layered defenses that actually stop it.
What Is a Watering Hole Attack? The Core Definition
A watering hole attack is a form of cyberattack that targets groups of users by infecting websites that they commonly visit. The name takes its cue from animal predators that lurk by watering holes waiting for an opportunity to attack prey when their guard is down. Likewise, watering hole attackers lurk on niche websites waiting to infect websites — and in turn, infect their victims with malware.
What makes this attack category distinctly dangerous is its approach to trust. Unlike phishing, which requires the victim to click a deceptive link in a message, a watering hole attack requires no deception at all. The victim visits a real, legitimate website they have visited hundreds of times before. They do nothing wrong. They receive no suspicious message. They simply go to a website they trust — and that trust is the weapon the attacker uses against them.
Watering hole attacks are distinct from phishing or email-based malware because they exploit the trust users place in legitimate, well-known websites. Instead of tricking users into clicking fake links or attachments, these attacks operate through backdoors, drive-by downloads, or prompts to download malicious files. This method makes detection much more challenging for users and even cybersecurity systems.
Furthermore, watering hole attacks are among the hardest attacks to attribute and detect precisely because the compromised website is legitimate. Standard blacklists and reputation-based URL filters do not flag real, established websites — which is exactly why attackers choose this vector when targeting high-value organizations with mature perimeter defenses.
How a Watering Hole Attack Works: The Complete Step-by-Step
Understanding the mechanics of a watering hole attack reveals both why it is so effective and where defensive opportunities exist. The attack unfolds in four distinct phases.
Phase 1 — Target Profiling
Every watering hole attack begins with intelligence gathering. The attacker identifies a specific target — a defense contractor, a government agency, a financial institution, a research organization, or an industry sector — and then researches which external websites that organization’s employees visit regularly. Industry forums, professional association sites, regulatory body pages, trade publications, vendor portals, and community-specific news sites are common candidates.
This research uses multiple sources: analyzing the target organization’s public web presence, monitoring their employees’ LinkedIn activity, reviewing industry publications they frequently reference, and sometimes deploying initial reconnaissance malware to observe browsing patterns directly.
The goal is to identify a site that is inherently trusted by the target group, visited frequently enough to guarantee victim exposure within a reasonable timeframe, and vulnerable enough to be compromised through known web application exploits.
Phase 2 — Compromising the Watering Hole Website
With the target site identified, the attacker compromises it. This typically happens through one of several methods: exploiting unpatched content management system vulnerabilities (WordPress, Joomla, and Drupal core and plugin vulnerabilities remain the most common entry points), stealing administrative credentials through prior phishing or credential stuffing, or exploiting web application flaws like SQL injection or cross-site scripting.
Once inside, the attacker injects malicious JavaScript, an iframe loading an exploit kit, or a redirect that activates specifically for visitors from certain IP ranges, organizations, or geographic regions. Attackers looking for specific information may only target users coming from a specific IP address. This also makes the attacks harder to detect and research. A visitor from outside the target organization’s IP range sees the site perfectly normally. A visitor from inside the target’s network — or from a targeted geographic region — receives the malicious payload.
This IP-filtering technique has a profound defensive implication: even security researchers visiting a compromised site from outside the target’s network may see nothing wrong, causing the infection to go undetected for weeks or months.
Phase 3 — Drive-By Download and Payload Delivery
When a qualifying victim visits the compromised site, the malicious code executes silently in their browser. The most common delivery mechanisms include drive-by downloads that exploit browser or plugin vulnerabilities to install malware without any user interaction, malicious iframes that redirect the browser to an exploit kit hosted on attacker infrastructure, and strategic JavaScript injection that runs in the background while the legitimate page appears and functions normally.
The malware delivered varies by campaign objective. Nation-state campaigns typically deliver remote access trojans (RATs), keyloggers, or sophisticated spyware frameworks that enable persistent surveillance. Criminal campaigns more commonly deliver ransomware, banking trojans, or information stealers. In either case, the infection completes without the victim taking any deliberate action beyond visiting a website they visit routinely.
Phase 4 — Persistence and Lateral Movement
Once initial compromise is achieved on an employee’s device, attackers establish persistence — ensuring their foothold survives reboots and security scans — and begin moving laterally through the corporate network. The watering hole serves as the initial access vector. Everything that follows exploits the level of trust that the compromised employee account or device has within the organization’s environment.
This is why watering hole attacks are particularly dangerous for organizations: the initial compromise often grants attacker access from inside the network perimeter, bypassing firewalls and perimeter defenses that only inspect traffic crossing the boundary from outside. From inside, lateral movement to domain controllers, file servers, and sensitive data repositories proceeds with far less friction.
Watering Hole vs. Phishing vs. Supply Chain Attack
Organizations frequently confuse watering hole attacks with phishing and supply chain attacks because all three exploit trust. However, they differ significantly in mechanism, detection difficulty, and required defenses.
| Factor | Watering Hole | Phishing | Supply Chain Attack |
|---|---|---|---|
| Initial victim action | Visit a trusted website | Click a deceptive link or attachment | Install or update legitimate software |
| Deception required | None — legitimate site is compromised | Yes — fake message or sender | None — legitimate vendor is compromised |
| Target scope | Group of users sharing website behavior | Individual or mass targeting | Everyone using the compromised product |
| Detection by email gateway | None — no email involved | Moderate effectiveness | None — no email involved |
| Detection by URL filter | Low — legitimate domain | Moderate — suspicious domains often flagged | None — legitimate update servers |
| Primary threat actor | Nation-state APTs, advanced criminal groups | Criminal groups, script kiddies | Nation-state APTs (SolarWinds model) |
| Notable 2024–2026 examples | APT29 Mongolian government sites, SilentSelfie | APWG 3.8M attacks in 2025 | XZ Utils backdoor, 3CX supply chain |
| Average time to detection | 287 days (industry estimate) | 21 days (email-based) | 150–300 days |
Specific targets of watering hole attacks are highly targeted, often focusing on industries like defense, government, finance, healthcare, and energy — sectors targeted because of the sensitive or valuable data they handle, such as classified information, financial details, or patient records.
Understanding how phishing and social engineering differ from technical web-based attacks is foundational when building a layered defense — each attack class requires different defensive controls, and confusing them leads to dangerous coverage gaps.
Real Watering Hole Attack Cases: 2023 Through 2026
Studying real incidents is the fastest path to genuine understanding. These cases shaped the current threat landscape.
APT29 Mongolian Government Websites (2023–2024)
Between November 2023 and July 2024, the Russian-linked hacking group APT29, also known as Cozy Bear, compromised Mongolian government websites. They targeted site audiences with vulnerable devices with spyware, leading to data breaches and unwanted access. APT29 is one of the most sophisticated threat actors in the world — responsible for the SolarWinds supply chain attack and numerous high-profile diplomatic intrusions. Their selection of Mongolian government websites reveals a calculated approach: compromise sites visited by diplomatic and government personnel across Central Asia, then harvest credentials and intelligence from the resulting infections. Visitors from targeted IP ranges received iOS and Android spyware delivered silently through browser exploits.
SilentSelfie — Kurdish Minority Sites (2024)
In 2024, a watering hole attack on 25 websites linked to the Kurdish minority compromised sensitive user information. The attack, dubbed SilentSelfie, involved four different attack variants, ranging from stealing user location information to installing malicious applications on Android devices. This campaign exemplifies the political surveillance dimension of watering hole attacks. Attackers did not need to identify individual targets. They simply compromised the community websites a specific ethnic and political group relied upon, then let the audience deliver itself to the malware. The geographic targeting and political motivation make SilentSelfie a textbook state-sponsored surveillance operation.
Tortoiseshell — Israeli Shipping and Logistics Sites (2023)
In 2023, at least eight Israeli shipping and logistics websites were compromised in a watering hole attack linked to the Iran-affiliated group Tortoiseshell, targeting sensitive industrial systems. The choice of logistics sector websites was strategic. Supply chain and shipping personnel routinely visit industry-specific portals to track cargo, check regulatory updates, and coordinate with partners. Compromising those sites guaranteed exposure to exactly the operational technology personnel whose credentials and network access Tortoiseshell sought.
EmEditor Download Page Compromise (December 2025)
In late December 2025, EmEditor — a widely used text and code editor — published a security advisory warning users that its official download page had been compromised. The attackers’ goal was to distribute a trojanized version of the software. This case straddles the boundary between a watering hole attack and a supply chain attack. The attacker compromised the vendor’s official distribution point rather than a third-party site, meaning every developer or technical user who downloaded the software through legitimate channels received the malicious version. Developer tools are particularly high-value targets because the compromise propagates into every codebase the infected developer works on.
DarkSword Campaign (2026)
DarkSword operates as a watering hole attack: it compromises a website and then waits for victims to visit. Discovered in early 2026, DarkSword demonstrated the “set and wait” patience that distinguishes sophisticated watering hole operations from opportunistic attacks. The campaign targeted technical and professional forums, deploying a zero-day browser exploit that executed at browser level without requiring any plugin or software vulnerability — a particularly difficult attack to stop through conventional patching.
JPCERT Reported Campaign — Japan (December 2024)
In December 2024, multiple watering hole attacks were reported by JPCERT/CC, where attackers compromised legitimate sites for malware distribution. Instead of exploiting software vulnerabilities, the attackers relied on social engineering techniques. As a result, they successfully tricked users into executing malicious files. This case is notable because it demonstrates that watering hole attacks do not always require zero-day browser exploits. Injecting social engineering prompts — fake download dialogs, fake plugin update requests — into compromised legitimate sites can be equally effective and requires no sophisticated exploit code.
Why Watering Hole Attacks Are Growing More Dangerous in 2026
Three converging trends make watering hole attacks more threatening in 2026 than at any prior point.
Zero-day availability has increased. Eleven of the 15 top routinely exploited CVEs in 2023 were initially exploited as zero-days — compared to just two in 2022. Watering hole campaigns frequently leverage zero-day browser and plugin vulnerabilities that victims cannot patch against because patches do not yet exist. The growing availability and commercialization of zero-day exploits — available on dark web markets and through broker ecosystems — gives more threat actors access to the browser exploits that watering hole attacks depend on.
Browser-based attack surfaces are expanding. Modern browsers support an increasingly complex web of JavaScript APIs, WebAssembly execution, browser extensions, and privileged system access. Each new capability creates new attack surface. Watering hole operators are particularly attentive to newly disclosed browser vulnerabilities — often deploying exploit code within days of a proof-of-concept publication, before the majority of users apply the available patch.
Legitimate websites are increasingly vulnerable. Most small and medium-sized industry and community websites run outdated CMS software, unpatched plugins, and minimal security monitoring. They are plausible, trusted, and trivial to compromise — the ideal combination for a patient attacker profiling a high-value target’s browsing behavior.
Understanding how AI is transforming cybersecurity defenses becomes directly relevant here: AI-assisted threat detection that monitors behavioral anomalies in web traffic is currently the most promising tool for detecting watering hole activity before payload delivery completes.
How to Defend Against Watering Hole Attacks: Layered Controls
No single control stops a watering hole attack. Effective defense requires overlapping layers — each catching what the others miss.
Deploy a Secure Web Gateway with URL and Content Inspection
A Secure Web Gateway (SWG) sits between your users and the internet, inspecting all outbound and return web traffic. Modern SWGs — including cloud-delivered variants integrated into SASE platforms — perform real-time page content analysis, JavaScript deobfuscation, and behavioral sandboxing that detects malicious code even on legitimate domains.
This is where SWGs fundamentally outperform traditional URL reputation filters: they analyze what the page is doing, not just where the page lives. A legitimate website that has been injected with malicious JavaScript triggers content-based detection even though its domain reputation remains clean. For organizations exploring zero trust security architectures, SASE-integrated SWGs represent the web traffic inspection component of a complete zero trust security web access policy.
Enforce Browser Isolation
Browser isolation — particularly remote browser isolation (RBI) — executes all web content in a sandboxed cloud environment and streams only a safe visual representation to the user’s device. Even if a compromised site delivers a perfect zero-day exploit, that exploit executes in an isolated container that has no access to the user’s device, network credentials, or corporate resources.
RBI is particularly valuable for employees who must regularly access high-risk external sites — vendor portals, community forums, industry publications — that cannot be blocked without disrupting legitimate workflows. The browsing experience remains essentially normal while the risk is effectively eliminated at the execution layer.
Patch Browser and Plugin Vulnerabilities Aggressively
Defense against watering hole attacks requires layers: patch continuously, deploy EDR tools, use Secure Web Gateways, apply zero trust to web traffic, and train your users. Browser patching deserves special emphasis because it directly closes the exploit window that watering hole attacks depend on. Implement a browser update policy that ensures all enterprise browsers apply security patches within 24 hours of release — not the standard 30-day patch cycle used for other software. Additionally, audit and minimize browser extensions across your organization. Extensions with broad host permissions represent significant attack surface for both watering hole delivery and post-compromise credential theft.
Deploy Endpoint Detection and Response
Even if a watering hole attack delivers its payload successfully, a capable EDR platform detects the post-exploitation behavior — process injection, lateral movement attempts, credential dumping, unusual outbound connections — and enables rapid containment before significant damage occurs. Understanding how endpoint detection tools prevent data breaches demonstrates why EDR is the critical last line of defense when perimeter and web controls fail.
Pairing EDR with threat intelligence feeds that include known watering hole campaign indicators — malicious domains, C2 server addresses, known exploit signatures — dramatically accelerates detection. Several threat intelligence providers now specifically track active watering hole campaigns and surface indicators before the malware reaches victim networks in volume.
Network Segmentation and Zero Trust Access
Because watering hole attacks typically compromise a single employee device and then rely on lateral movement, network micro-segmentation directly limits the blast radius. A compromised device in a properly segmented network cannot freely reach domain controllers, file servers, or sensitive application environments. The attacker gains a foothold but cannot advance it.
Apply zero trust principles to web traffic specifically — no employee device, regardless of network location, should receive implicit trust when accessing internal resources. Every access request requires authentication, device health validation, and scope-limited authorization. This principle, documented in NIST SP 800-207, is the architectural evolution that makes watering hole lateral movement dramatically harder to execute.
Conduct Threat Hunting for Watering Hole Indicators
Proactive threat hunting focuses specifically on signals consistent with watering hole activity: unusual outbound connections from browsers to unfamiliar external IPs immediately after visiting legitimate sites, unexpected process spawning from browser processes, DNS queries to newly registered or low-reputation domains initiated by browser processes, and lateral movement indicators appearing shortly after an employee’s normal browsing session.
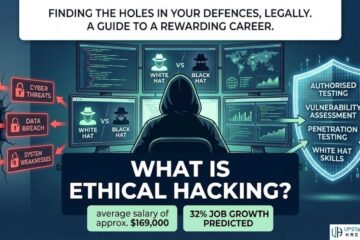
Penetration testing that simulates watering hole delivery measures whether your EDR, SWG, and network monitoring stack actually detects the attack chain — and identifies the specific gaps that real attackers would exploit. This is especially important because watering hole attacks are rarely included in standard penetration test engagements, leaving organizations with blind spots that tested phishing and external perimeter scans would never reveal.
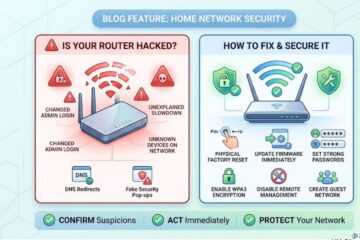
Additionally, securing your own web properties matters — because your organization’s website may itself be a target for compromise if your industry makes you a useful watering hole. Attackers targeting organizations in your supply chain or sector may attempt to weaponize your site against your partners and customers. Continuous web application monitoring, integrity checking, and content security policy enforcement protect against your site being used as a watering hole against others.
For small businesses with limited security staff, AI-powered cybersecurity tools designed for SMBs now offer cloud-delivered SWG and behavioral anomaly detection capabilities that previously required enterprise-grade infrastructure. The barrier to entry for meaningful watering hole defense has dropped significantly in 2026.
For organizations building formal incident response plans, both CISA’s Advanced Persistent Threat guidance and the UK National Cyber Security Centre’s watering hole attack documentation provide authoritative frameworks for both detection and response specifically covering watering hole scenarios.
Understanding the full social engineering threat landscape — including how baiting attacks, phishing emails, and vishing calls often complement watering hole campaigns in multi-stage attacks — builds the comprehensive threat model that effective security strategy requires. Attackers rarely use a single technique in isolation: a watering hole may deliver initial access, followed by a vishing call that social-engineers the victim into disabling their security software, followed by credential-based lateral movement through the corporate network.
For ongoing awareness of the techniques attackers combine with watering hole infrastructure, monitoring threat intelligence for AI-augmented attack campaigns keeps your understanding current as the threat evolves.
Frequently Asked Questions

What is a watering hole attack in simple terms?
A watering hole attack is when a hacker compromises a legitimate website that a specific group of people regularly visits — then uses that compromised site to infect visitors with malware. Instead of sending fake emails or links to their targets, attackers simply wait for victims to visit a site they already trust. The name comes from the predator strategy of waiting at a watering hole for prey to come to them. No suspicious link, no deceptive message, no user error required — just a routine visit to a familiar website that has been secretly weaponized.
How is a watering hole attack different from phishing?
Phishing requires the attacker to send a deceptive message — typically an email — and persuade the victim to click a malicious link or open a dangerous attachment. The victim must take a specific action in response to a message they receive. A watering hole attack requires no deception and no message. The victim simply visits a website they trust and visit regularly. The malicious code executes in the background without any interaction beyond loading the page. This makes watering hole attacks significantly harder to prevent through user training alone, because the victim does nothing wrong — they visit a real site they have every reason to trust.
Who is typically targeted by watering hole attacks?
Watering hole attacks disproportionately target high-value sectors: government agencies, defense contractors, financial institutions, healthcare organizations, energy companies, and research institutions. They are primarily a tool of sophisticated threat actors — nation-state APT groups and advanced criminal organizations — who need access to specific, well-defended targets that cannot be easily compromised through direct attacks. The targeting logic is sector-specific: defense researchers visit specific technical forums; government diplomats use specific government portals; healthcare compliance teams consult specific regulatory sites. Compromising those niche, sector-specific sites guarantees a steady stream of high-value victims from the intended target group.
Can antivirus software detect watering hole attacks?
Standard signature-based antivirus software has limited effectiveness against sophisticated watering hole attacks, particularly those using zero-day browser exploits or heavily obfuscated JavaScript. Detection is more reliable through behavioral analysis tools — specifically, EDR platforms that monitor process behavior rather than file signatures, and Secure Web Gateways that analyze JavaScript execution in sandboxed environments. The best defense combines a SWG for pre-execution analysis, an EDR for post-execution behavioral detection, network segmentation to limit lateral movement if compromise occurs, and threat intelligence feeds that provide early warning of active watering hole campaigns targeting your sector.
How do I know if my organization has been hit by a watering hole attack?
Watering hole attacks are notoriously difficult to detect because they originate from legitimate, trusted websites and deliver malware through browser processes that appear normal. Key indicators to monitor include: unusual outbound network connections from browser processes to unfamiliar external IPs immediately after visiting legitimate sites; unexpected new processes spawning from browser parent processes; DNS queries to newly registered or low-reputation domains initiated by browsers during normal browsing sessions; behavioral anomalies in user accounts — lateral movement, privilege escalation, unusual file access — appearing shortly after routine browsing activity; and EDR alerts for process injection or credential dumping on endpoints that have not received suspicious email or executed unknown files. Proactive threat hunting that specifically looks for these browser-originating anomalies is the most reliable detection method, supplemented by threat intelligence feeds covering active watering hole campaigns in your sector.